About Caphaw Malware
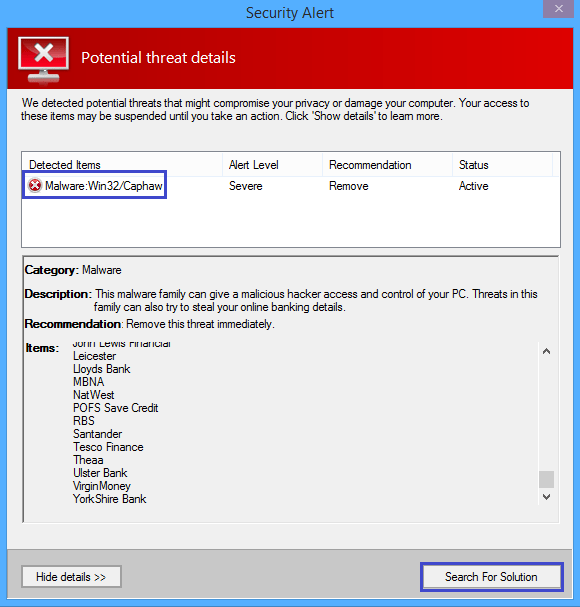
Trojan Horse infections an threaten your computer in many different ways as those are among the most versatile forms of malware that can be encountered on the Internet. Caphaw is yet another addition to this family of software threats – it is a dangerous program and many users have reported the presence of this malware in their system. If you are among those users and are looking for help with the removal of the insidious Caphaw Malware, you should definitely check out the guide at the end of this page. However, you must also make sure that you are aware of the main characteristics of this threat – being informed about the different types of malware is an essential part of keeping your system safe.
The stealthiness and sneakiness of the Trojans is well known. Initially, the main goal of such a virus is to enter the computer and gain Admin privileges so that it would have almost full control over the attacked computer and would also be able to access most of the data stored on it. In order to achieve this, the virus is usually presented to its victim as some form of seemingly harmless piece of data. This is why pirated games and other illegally distributed pieces of software are so popular tools of Trojan Horse distribution – the hackers can easily disguise a threat such as Caphaw or Idle Buddy as the installer of some pirated game or some other program. Once the user executes the fake installer and allows it to make changes to the system through an Admin’s account, the infection that’s hidden in the .exe file would gain all the rights that the Admin profile of the user has. What this means is the hacker behind the Trojan would be able to access, modify and delete data on the computer, they’d also be able to initiate different processes and activities in the machine without the user’s knowledge or permission. In some cases, Trojans are even used to download other harmful programs onto the infected computer. We are talking about Ransomware, Spyware, Rootkits and many more. As a matter of fact, the Trojan Horse representatives are one of the most commonly used tools for spreading Ransomware and getting such infections inside more computers. All in all, there are more than enough reasons why you simply cannot waste time if you think Caphaw Malware is in your machine.
To successfully rid your computer of the nasty Trojan named Caphaw, you will need to carefully follow each and every step from the guide below and also use the suggested removal program in case the manual steps didn’t fully remove the infection. Also, remember to think about future safety – a good security tool can go a long way towards ensuring the protection of your system and data. If you don’t currently have any software security – know that the tool we already mentioned could greatly improve the security levels of your system.
SUMMARY:
| Name | Caphaw |
| Type | Trojan |
| Danger Level | High (Trojans are often used as a backdoor for Ransomware) |
| Symptoms | Symptoms of a Trojan infection may include the slow-down of your machine, sudden system crashes, software errors, and more similar system disruptions. |
| Distribution Method | The distribution of pirated software is oftentimes associated with Trojan Horse infections. |
[add_third_banner]
Remove Caphaw Malware
1: Preparations
Note: Before you go any further, we advise you to bookmark this page or have it open on a separate device such as your smartphone or another PC. Some of the steps might require you to exit your browser on this PC.
2: Task Manager
Press Ctrl + Shift + Esc to enter the Task Manager. Go to the Tab labeled Processes (Details for Win 8/10). Carefully look through the list of processes that are currently active on you PC.
If any of them seems shady, consumes too much RAM/CPU or has some strange description or no description at all, right-click on it, select Open File Location and delete everything there.

Also, even if you do not delete the files, be sure to stop the process by right-clicking on it and selecting End Process.
3: IP related to Caphaw
Go to c:\windows\system32\drivers\etc\hosts. Open the hosts file with notepad.
Find where it says Localhost and take a look below that.

If you see any IP addresses there (below Localhost) send them to us here, in the comments since they might be coming from the Caphaw.
[add_forth_banner]
4: Disable Startup programs
Re-open the Start Menu and type msconfig.
Click on the first search result. In the next window, go to the Startup tab. If you are on Win 10, it will send you to the Startup part of the task manager instead, as in the picture:

If you see any sketchy/shady looking entries in the list with an unknown manufacturer or a manufacturer name that looks suspicious as there could be a link between them and Caphaw , disable those programs and select OK.
5: Registry Editor
Press Windows key + R and in the resulting window type regedit.
Now, press Ctrl + F and type the name of the virus.
Delete everything that gets found. If you are not sure about whether to delete something, do not hesitate to ask us in the comments. Keep in mind that if you delete the wrong thing, you might cause all sorts of issues to your PC.
6: Deleting potentially malicious data – Caphaw
Type each of the following locations in the Windows search box and hit enter to open the locations:
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
%Temp%
Delete everything you see in Temp linked to Caphaw Malware. About the other folders, sort their contents by date and delete only the most recent entries. As always, if you are not sure about something, write to us in the comment section.
Leave a Reply