About Chaos CC Hacker Group
Typically, computer productivity slow-downs, sudden crashes, software errors and failure, and BSOD can be symptoms of different problems, and the presence of a Trojan Horse is only one of the many possible causes for such issues. Also, in many cases, a Trojan infection wouldn’t really show anything visible that may draw the user’s attention to the ongoing infection. Still, in many cases, the disturbances we mentioned may indeed be caused by a Trojan present in the system, and in those instances, the user’s attention, caution and quick actions could be what makes the difference between cleaning your computer on time, and facing some very serious consequences of the attack that has happened to the system.
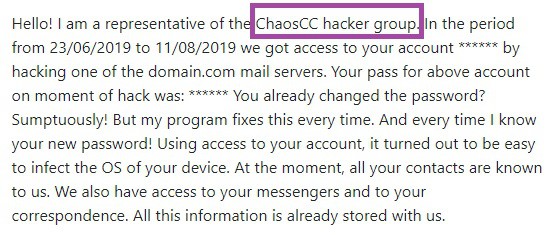
Chaos CC Hacker Group Email will be the focus of our article today – it is a nasty representative of the Trojan Horse family (Drive by exploit, Save Yourself) and you surely wouldn’t want it to be anywhere near your computer. However, since you are reading this, it is probably too late for you to keep Chaos CC Hacker Group away from your system, because it has already gotten there. If this is the case and you are looking for help against this insidious malware program, the article you are reading right now may be exactly what you need in order to take care of this infection. Know, however, that the Trojans are sneaky threats and it is important to know them in order to be able to successfully fight them. Therefore, before we give you the guide for the removal of Chaos CC Hacker Group, we should first mention a few more things about this nefarious malware piece.
What you could expect from this virus
Usually, in order to achieve any of its goals, a Trojan needs to have administrative privileges in the infected computer. That way, it can do pretty much everything that you, yourself, can do on the computer. This means that the Trojan could initiate different processes, have access to most of the data stored on the machine and even download stuff from the Internet. This is one of the reasons why the Trojan infections are so commonly used as distribution tools for Ransomware cryptoviruses.
In order to gain administrative rights in the computer, most Trojans are presented to their victims as executable files. Once you open the file and click on Agree when asked whether you’d allow the executable to make changes in your system, the Trojan gains all of the Admin rights on the attacked computer and begins to carry out its insidious tasks. Now, what those tasks may be is a topic we’d need a whole separate article in order to fully cover. Suffice to say that once Chaos CC Hacker Group has Admin rights in your computer, it could cause many different forms of harm, and in many cases, the victims wouldn’t even be aware of the fact their system has been silently infiltrated.
Now, if you have somehow noticed the virus or at least think that it is in your system, we strongly advise you to start completing the following steps in order to prevent the Trojan from completing its criminal activities.
SUMMARY:
| Name | Chaos CC Hacker Group |
| Type | Trojan |
| Danger Level | High (Trojans are often used as a backdoor for Ransomware) |
| Symptoms | The symptoms related to Trojan infections may vary greatly – from BSOD crashes, and sudden system freezes, to slow-down and software failure. |
| Distribution Method | There are many methods that can be used to spread such infections – spam e-mails, misleading ads in sketchy sites, pirated content and more. |
[add_third_banner]
Remove Chaos CC Hacker Group Email
1: Preparations
Note: Before you go any further, we advise you to bookmark this page or have it open on a separate device such as your smartphone or another PC. Some of the steps might require you to exit your browser on this PC.
2: Task Manager
Press Ctrl + Shift + Esc to enter the Task Manager. Go to the Tab labeled Processes (Details for Win 8/10). Carefully look through the list of processes that are currently active on you PC.
If any of them seems shady, consumes too much RAM/CPU or has some strange description or no description at all, right-click on it, select Open File Location and delete everything there.

Also, even if you do not delete the files, be sure to stop the process by right-clicking on it and selecting End Process.
3: IP related to Chaos CC Hacker Group
Go to c:\windows\system32\drivers\etc\hosts. Open the hosts file with notepad.
Find where it says Localhost and take a look below that.

If you see any IP addresses there (below Localhost) send them to us here, in the comments since they might be coming from the Chaos CC Hacker Group.
[add_forth_banner]
4: Disable Startup programs
Re-open the Start Menu and type msconfig.
Click on the first search result. In the next window, go to the Startup tab. If you are on Win 10, it will send you to the Startup part of the task manager instead, as in the picture:

If you see any sketchy/shady looking entries in the list with an unknown manufacturer or a manufacturer name that looks suspicious as there could be a link between them and Chaos CC Hacker Group , disable those programs and select OK.
5: Registry Editor
Press Windows key + R and in the resulting window type regedit.
Now, press Ctrl + F and type the name of the virus.
Delete everything that gets found. If you are not sure about whether to delete something, do not hesitate to ask us in the comments. Keep in mind that if you delete the wrong thing, you might cause all sorts of issues to your PC.
6: Deleting potentially malicious data – Chaos CC Hacker Group
Type each of the following locations in the Windows search box and hit enter to open the locations:
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
%Temp%
Delete everything you see in Temp linked to Chaos CC Hacker Group. About the other folders, sort their contents by date and delete only the most recent entries. As always, if you are not sure about something, write to us in the comment section.
Leave a Reply