Lokf Virus
About Lokf Virus
Would you like to learn how to remove the Lokf Virus infection from your system? We can assist you to do that right here. If you’ve become a victim of this extremely harmful file-encrypting Ransomware, you’ll find the exact steps on how to get rid of it successfully in the next lines. Not only that, but you may also get some ideas on how to restore your encrypted files without paying the ransom with the help of the instructions below. But let’s first say a few words about the exact malware piece you are facing, and the possible ways to deal with it.
What Is Lokf Virus?
Lokf Virus works is very different from the way any other type of malware functions. Most viruses and malware programs attempt to cause some system damage, collect credentials, spy on you, or steal some sensitive information that can later be used for cyber crimes. Lokf Virus, on the other hand, uses a unique technique called file-encryption that does not ruin your system or files, but instead simply locks the data with a powerful algorithm. Once the Ransomware finds its way to your machine, it quietly activates a file-encryption process in the background of the system. As a result, all the files stored on the computer become unreadable and, cannot be opened or used without the application of a special decryption key.
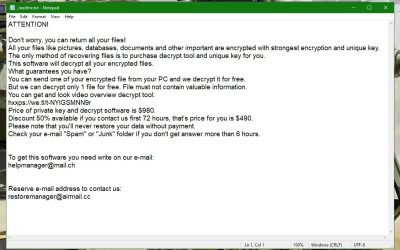
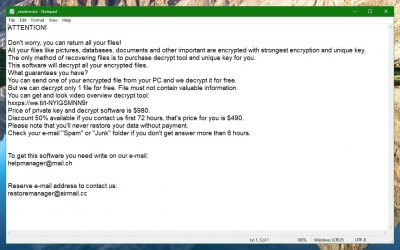
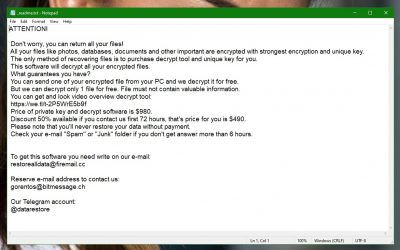
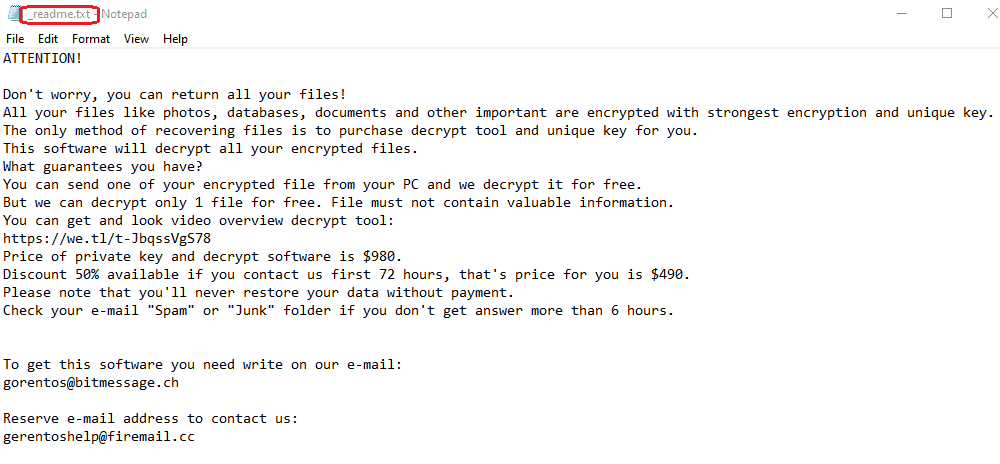
Upon the completion of the encryption process, the malware reveals itself with a ransom note that gets directly on the victim’s screen. This note contains a message from the cyber criminals who control the infection. They inform you that your files have been locked with secret encryption, and the only way you can access them is by paying a ransom in exchange for the decryption key they possess. The payment is typically requested in Bitcoins as, for cyber-thefts, this is a very convenient money transaction method, because this online currency is untraceable, and helps them to remain hidden from the authorities. The crooks provide all the payment instructions to the victims, and often give a short deadline. If the payment is not made within the set deadline, however, the hackers oftentimes threaten to double the ransom amount, or even destroy the unique decryption key, capable of recovering your encrypted data.
The Lokf Virus file encryption
Unfortunately, there’s not much you can do when you fall a victim to a Ransomware like Lokf Virus, Coot or Mosk. There are basically two possible choices – pay the ransom, and leave yourself at the mercy of the crooks, or remove the infection by yourself, and try to get your files back via other means. The unscrupulous crooks are not afraid to use various manipulative approaches to press the victims into paying the ransom. However, abiding the hackers’ demands does not guarantee that the victims would actually get a working decryption key. At the same time, the infected machine remains vulnerable to all kinds of malicious threats and attacks, while the Ransomware is present on it.
That’s why cleaning your system from Lokf Virus is a good way to block the hacker’s access to your computer. You can do this if you follow the instructions below. We also recommend that you have a look at our file-recovery suggestions that are included in the guide. You may potentially find a solution for decrypting your files there. We should inform you, though, that the developers of Ransomware are one step ahead of the security researchers. Therefore, some encryption algorithms of Ransomware are more challenging to decrypt than others. Regardless, regaining control over your computer and not paying a penny to the unscrupulous cyber-criminals is still the preferable option.
SUMMARY:
| Name | Lokf Virus |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Very few and unnoticeable ones before the ransom notification comes up. |
| Distribution Method | From fake ads and fake system requests to spam emails and contagious web pages. |
Remove Lokf Virus Ransomware Guide
1: Preparations
Note: Before you go any further, we advise you to bookmark this page or have it open on a separate device such as your smartphone or another PC. Some of the steps might require you to exit your browser on this PC.
2: Task Manager
Press Ctrl + Shift + Esc to enter the Task Manager. Go to the Tab labeled Processes (Details for Win 8/10). Carefully look through the list of processes that are currently active on you PC.
If any of them seems shady, consumes too much RAM/CPU or has some strange description or no description at all, right-click on it, select Open File Location and delete everything there.
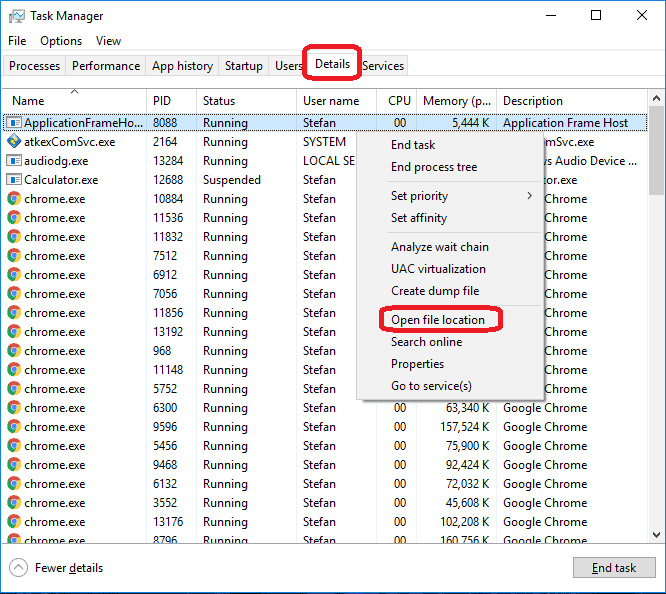
Also, even if you do not delete the files, be sure to stop the process by right-clicking on it and selecting End Process.
3: IP related to Lokf Virus
Go to c:\windows\system32\drivers\etc\hosts. Open the hosts file with notepad.
Find where it says Localhost and take a look below that.

If you see any IP addresses there (below Localhost) send them to us here, in the comments since they might be coming from the Lokf Virus.
[add_forth_banner]
4: Disable Startup programs
Re-open the Start Menu and type msconfig.
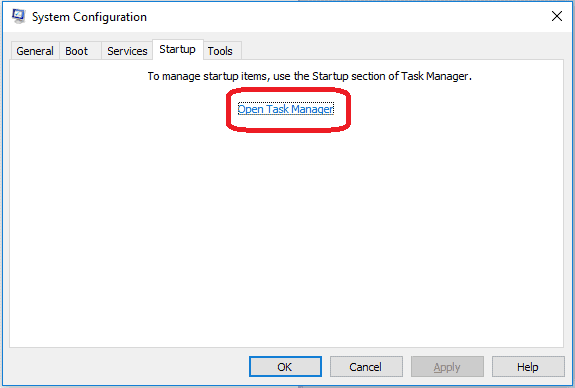
Click on the first search result. In the next window, go to the Startup tab. If you are on Win 10, it will send you to the Startup part of the task manager instead, as in the picture:
If you see any sketchy/shady looking entries in the list with an unknown manufacturer or a manufacturer name that looks suspicious as there could be a link between them and Lokf Virus , disable those programs and select OK.
5: Registry Editor
Press Windows key + R and in the resulting window type regedit.
Now, press Ctrl + F and type the name of the virus.
Delete everything that gets found. If you are not sure about whether to delete something, do not hesitate to ask us in the comments. Keep in mind that if you delete the wrong thing, you might cause all sorts of issues to your PC.
6: Deleting potentially malicious data – Lokf Virus
Type each of the following locations in the Windows search box and hit enter to open the locations:
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
%Temp%
Delete everything you see in Temp linked to Lokf Virus Ransomware. About the other folders, sort their contents by date and delete only the most recent entries. As always, if you are not sure about something, write to us in the comment section.
7: Lokf Virus Decryption
The previous steps were all aimed at removing the Lokf Virus Ransomware from your PC. However, in order to regain access to your files, you will also need to decrypt them or restore them. For that, we have a separate article with detailed instructions on what you have to do in order to unlock your data. Here is a link to that guide.