About .Mosk Virus
What is Mosk Virus? How does Mosk Virus work? How to try and restore files, encrypted by Mosk Virus ransomware?
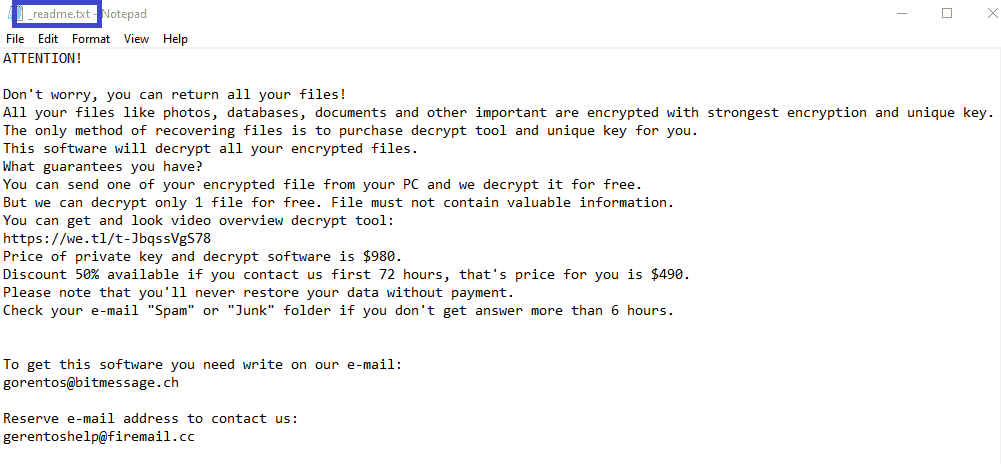
.Mosk Virus is a very stealthy infection from the Ransomware cryptovirus type. You surely have been infected with .Mosk Virus if a note on yours screen has told you that some of your files have been encrypted, and that you must pay a ransom for their release. We do not wish to scare you, but this is one of the most terrifying pieces of malware that might enter your system. Ransomware secretly locks your personal files with a complex encryption algorithm, and then requires a ransom payment in order to send you the encryption key you need to get back your files.
In the text below, however, you will find comprehensive guidelines for removing .Mosk. Having the malware removed from your system will not automatically restore your files, therefore, we have created a special section in the removal guide with some file-recovery suggestions that do not involve paying ransom to the hackers behind the infection. But before you scroll down, we would like to first give you a little more information, so you can better comprehend the way in which .Mosk, .Meka, .Coot and other Ransomware threats operate. This understanding will enable you to better protect your system from malware of this kind in the future.
What is .Mosk Virus?
Mosk Virus is a cryptovirus that can be found in many web locations. Typically, the .Mosk Virus can be hidden inside seemingly harmless files, email attachments, torrents, spam messages, ads, and more. Therefore, if you want to keep away from such threats, be extremely cautious when opening emails from unknown sources, especially if they include attachments and/or links. Also, stay away from potentially risky websites, and shady online platforms. It goes without saying that you should avoid downloading content from untrusted websites, and have a strong antivirus program running at all times.
.Mosk Virus file encryption
The .Mosk Virus file encryption process mostly occurs without getting unnoticed. The effects of the .Mosk Virus file encryption will only be revealed once the Ransomware has applied its encoding to all the files. If you are reading this, you may have been scared by the ransom demanding notification on your screen, and you have been made to believe that you should pay the money as quickly as possible, or you may risk losing your documents forever.
However, paying the hackers may not be the best course of action for you. Yes, they may promise to send you a decryption key for your files, but even if they really send you one, they certainly wouldn’t assist you if it turns out there is some kind of a defect with the key, and not all files can be decrypted. Not to mention that you will encourage these criminals to continue to blackmail more people with the Ransomware, and create more advanced versions of it if you pay the ransom.
Therefore, we recommend that you first try to handle this issue on your own, and focus on how to remove the infection with the help of the removal guide below. It will help you secure your system, and avoid future encryption of more files.
Also, if you’d like to be protected from future threats of this kind, we recommend that you have a working antivirus at all times, and frequently perform virus checks to avoid such things from happening again. Do not visit shady, potentially dangerous websites, and be very cautious when opening messages from unknown sources, especially those with links, and/or attachments.
SUMMARY:
| Name | .Mosk Virus |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Very few and unnoticeable ones before the ransom notification comes up. |
| Distribution Method | From fake ads and fake system requests to spam emails and contagious web pages. |
[add_third_banner]
.Mosk Virus Removal Instructions
1: Preparations
Note: Before you go any further, we advise you to bookmark this page or have it open on a separate device such as your smartphone or another PC. Some of the steps might require you to exit your browser on this PC.
2: Task Manager
Press Ctrl + Shift + Esc to enter the Task Manager. Go to the Tab labeled Processes (Details for Win 8/10). Carefully look through the list of processes that are currently active on you PC.
If any of them seems shady, consumes too much RAM/CPU or has some strange description or no description at all, right-click on it, select Open File Location and delete everything there.

Also, even if you do not delete the files, be sure to stop the process by right-clicking on it and selecting End Process.
3: IP related to .Mosk
Go to c:\windows\system32\drivers\etc\hosts. Open the hosts file with notepad.
Find where it says Localhost and take a look below that.

If you see any IP addresses there (below Localhost) send them to us here, in the comments since they might be coming from the .Mosk.
[add_forth_banner]
4: Disable Startup programs
Re-open the Start Menu and type msconfig.
Click on the first search result. In the next window, go to the Startup tab. If you are on Win 10, it will send you to the Startup part of the task manager instead, as in the picture:

If you see any sketchy/shady looking entries in the list with an unknown manufacturer or a manufacturer name that looks suspicious as there could be a link between them and .Mosk Virus , disable those programs and select OK.
5: Registry Editor
Press Windows key + R and in the resulting window type regedit.
Now, press Ctrl + F and type the name of the virus.
Delete everything that gets found. If you are not sure about whether to delete something, do not hesitate to ask us in the comments. Keep in mind that if you delete the wrong thing, you might cause all sorts of issues to your PC.
6: Deleting potentially malicious data – .Mosk
Type each of the following locations in the Windows search box and hit enter to open the locations:
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
%Temp%
Delete everything you see in Temp linked to .Mosk Virus Ransomware. About the other folders, sort their contents by date and delete only the most recent entries. As always, if you are not sure about something, write to us in the comment section.
7: .Mosk Virus Decryption
The previous steps were all aimed at removing the .Mosk Virus Ransomware from your PC. However, in order to regain access to your files, you will also need to decrypt them or restore them. For that, we have a separate article with detailed instructions on what you have to do in order to unlock your data. Here is a link to that guide.
Leave a Reply