About the Akamaihd.net Virus
Akamaihd.net “Virus” is an application which might cause some unexpected page redirects and a quite unpleasant overall browsing disturbance if you get it installed on your PC. This application operates as a browser hijacker and we suggest you spend a few minutes on this page to learn more about its specifics as it’s important to be aware of what exactly this kind of software is. Generally, the browser hijackers are seen as potentially unwanted pieces of software which tend to disturb the users’ web browsing with various paid commercials. They oftentimes tend to change the settings of the default browser without asking for approval and tend to install some new toolbars, search engines and homepage domains that are usually unwanted by the user. It doesn’t really make any difference the kind of a browser you are using (it could be Chrome, Firefox, Explorer or another one) because the hijacker is usually able to latch onto most of them and to modify their settings in favor of some sponsored components. Most of the users who have an application like Akamaihd for mac, Results Value, Structured Service on their system usually complain about the never-ending ad-broadcasting, which they are forced to endure. We have done some tweaks to the removal guide however you can find the origianl removal guide for Akamaihd mac here
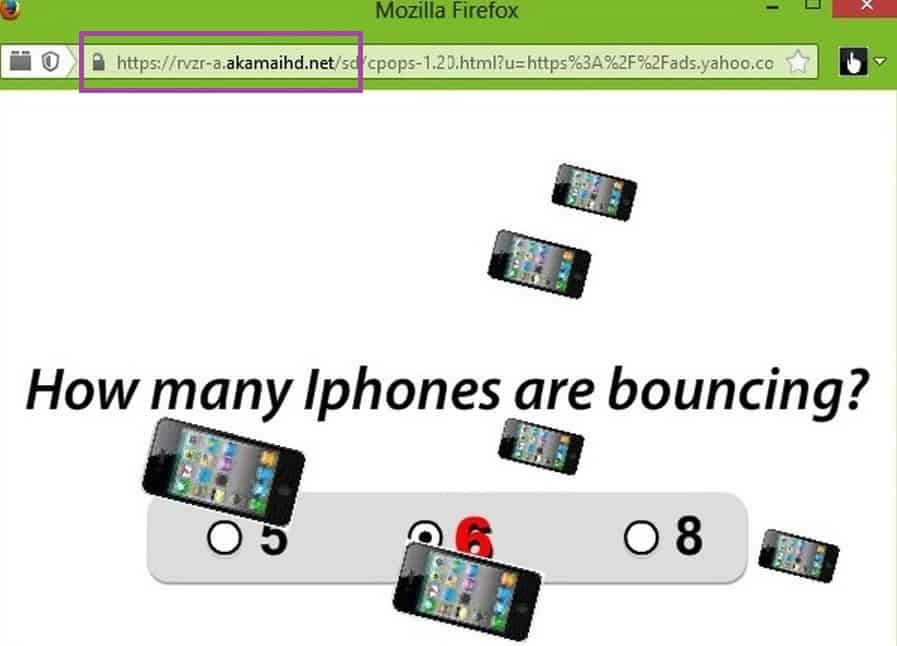
The hijacker normally starts to spam their screen with hundreds of pop-ups, ads, banners, redirect links and blinking boxes won’t stop appearing no matter how hard the customer tries to put an end to them. This behavior is frequently confused with some sort of a virus-inflicted activity and a lot of people get panicked when they first face it. However, the good news is that the activity of the browser hijackers is not related to some criminal deeds. It actually serves the needs of the online marketing industry. The Akamaihd.net Virus and the apps of this kind are pieces of software primarily developed for aggressive online advertising and revenue generation from pay-per-click ads. Their developers earn income every time you use the newly installed homepages, search engines or tools and click on the sponsored content that is generated. That’s why, they normally set their creations to literally hijack your browser by imposing some changes on its settings and flooding it with ads. It is usually somewhat difficult for an inexperienced user to revoke the changes and remove the ad-generating software if they don’t know how and where to correctly locate the browser hijacker-related files. For this reason, the effective removal process typically requires either the use of professional removal software or that of a detailed removal guide. That’s why, if Akamaihd.net is disturbing you, we suggest you take a look at the removal methods that our team has published below and use either (or both) of them for an effective removal of the pesky app.
What are the risks related to browser hijackers?
The browser hijackers are pieces of software which are normally considered to be relatively harmless mainly because their purpose isn’t inherently malicious.They significantly differ from malicious threats such as Ransomware, Spyware or Trojans, and do not contain harmful code which could cause damage to the system. Still, keeping them on the computer could lead to some quite unpleasant and irritating experiences. For instance, since the main purpose of the browser hijackers is to promote pay-per-click ads and to generate profits for their developers, they would hardly ever provide the end-user with any useful functionality. Furthermore, an application like Akamaihd.net Virus is very likely to negatively affect the normal web surfing activity of each user by initiating page-redirects to different sponsored websites, promotional links, offers, and sales pages, the sole purpose of which is to sell and to increase the web traffic to these products and locations.
If you are really looking to buy something, this might be a helpful activity, but if you have to deal with it every day, it could easily turn into a nuisance. Not to mention that the hijacker may not let you have control over the pages you land on and the content that gets displayed on your screen. This may greatly increase your chances of landing on something malicious such as a Ransomware, a Trojan or a Spyware carrier. That’s why, what we recommend you is avoid clicking on the randomly displayed ads and consider the uninstallation of the page-redirecting software.
Select the correct options when installing new software!
Browser hijackers could be found for free all over the Internet. These pieces of software are not malicious and that’s why it is totally possible that you may come across them while installing software updates, adding some plugins to your browser, interacting with ad-supported websites or downloading different free apps, optimization tools, games or similar easily available software. In most of the cases, the hijackers are bundled with the main installation package of another program or app and are promoted as “recommended” or “bonus” components. If you pay close attention to the setup configuration settings, however, you can disable them before they get installed on your PC and make changes to your browser. The easiest way to do that is to select the Custom/Advanced setup options and remove any preselected checkmarks that allow some unfamiliar or potentially unwanted applications to make changes to your settings and to your software.
SUMMARY:
| Name | Akamaihd.net |
| Type | Browser Hijacker |
| Danger Level | Medium (nowhere near threats like Ransomware, but still a security risk) |
| Symptoms | Your normal browsing may get interrupted with various unfamiliar ads, pop-ups and page-redirects. |
| Distribution Method | Spam messages, different software bundles, free download sites, torrents, automatic installers, ads. |
[add_third_banner]
Remove Akamaihd.net Virus
Step 1: Closing Safari (or any other browser that you may be using at the moment)
First, you will need to close your browser if it is still open. If you can’t do that normally, you will need to Force Quit it:
Open the Apple Menu and select Force Quit to do that. You can also use the ⌘ key + Option Key combination to open the Force Quit Applications dialog box. In this box, select the Safari browser (or whatever browser you are using) and then click on the Quit button. Confirm the action by selecting Force Quit again.
Step 2: Killing suspicious processes
Open Finder and go to Applications > Utilities and then open Activity Monitor. Now take a careful look at the processes there – look for any that seem suspicious, unknown and questionable. If you think that a given process may be the culprit behind the issue or may at least be related to it, highlight it with the mouse and select the i option at its top.
In the box that opens, click on Sample.
Scan the sample files with the online scanner we have on this page and if any of them get flagged as malicious, delete them and then kill their processes.
Step 3: Safely launching the browser
Hold the Shift from your keyboard and then launch Safari – holding Shift will prevent any previously opened pages to load again, just in case any of them were related to the problem.
If any problematic pages still load after you safe-launch the browser, then do the following:
Force-Quit the browser (Safari) again and then turn off your Wi-Fi connection by clicking on the Wi-Fi off option from the Mac Menu. If you are using cable Internet, simply disconnect the cable from your Mac.
Step 4: Uninstalling suspicious extensions
After you safe-launch Safari and are sure none of the previously opened pages load now, go to Preferences > Extensions.
Select and uninstall (by clicking on the Uninstall button) all extensions there that are unfamiliar to you or that you think may be suspicious. If you are not sure about a certain extension, it’s better to uninstall it – no extension is required for the normal functioning of the browser.
Step 5: Cleaning Safari
If you have other browsers aside from Safari, do the following:
In Safari, open Preferences from the browser’s menu and go to Privacy.
Select Remove All Website Data and then Remove Now. Note that this will delete all stored site data including any saved passwords and usernames. In other words, you will have to manually log-in to every site where you have a registration so make sure you remember your usernames and passwords.
Back in Preferences, click on General and see what your Safari’s homepage is. If it has been changed without your permission, change it back to what it used to be or to whatever you like it to be now.
Now go to the History menu and select the Clear History option.
Do the same to all other browsers you may have in your computer – here are examples with Chrome and Firefox.
[add_forth_banner]
Cleaning Chrome

Open Chrome and open its main menu, then go to More Tools > Extensions. Click on the Remove button next to all of the extensions that you do not trust.

Next, from the main menu, go to Settings and type Manage Search Engines in the search bar. Open the result that shows up and then delete all search engines other than the one you normally use by clicking on the three-dot icon next to the other ones and selecting Remove from list.

Back in Settings, type Reset and clean up and open the option that shows up (Restore settings to their original defaults). Confirm by selecting Reset Settings.
Cleaning Firefox

Open Firefox and then open its main menu. Go to Add-ons and open the Extensions menu from the left. Look at the extensions and Remove the ones you do not trust.

Next, open the menu again, go to Help > Troubleshooting information and in the page that opens, select Refresh Firefox and then confirm the action in the window that opens.
Leave a Reply