Win.Exploit.CVE_2019_0903-6966169-0 – Details
If a Trojan Horse named Win.Exploit.CVE_2019_0903-6966169-0 has recently attacked your computer, there’s no time to wast – you ought to take immediate measures against this malware piece and find a way to remove it from your system before it has fulfilled its nefarious tasks. Speaking of the task of this infection, we can’t really tell you the exact goal that it may be after. This Trojan is a rather new representative of its respective malware family and the information about it is still not sufficient enough. These types of malware programs are unlike other kinds of malware in the sense that their abilities may be highly varied and multi-functional. Other threatening malware programs like Ransomware or Rootkits usually have their purposes limited to only one or two tasks that those infections are supposed to complete. For instance, a Ransomware cryptovirus would use its advanced encryption to make its victim’s data inaccessible and would then request a payment for the locked data’s liberation – but it wouldn’t normally do anything else. A Rootkit, too, would only be used to complete a single goal, that goal being to block the user’s security software. Aside from that, it wouldn’t do much else. With Trojans like Win.Exploit.CVE_2019_0903-6966169-0, Cve-2019-0708 BlueKeep, however, things tend to be rather different – these infections are well known for how versatile they can be and how many different types of harm they may be able to cause. To give you an idea about just how multi-functional a Trojan might be, here is a short list of some of the more common uses of this type of infections:
- A Trojan could have the ability to impose remote control over any machine that it attacks and make it a part of its massive botnet of compromised machines. The computers from the botnet could be used for large-scale criminal tasks like Denial of Service attacks, cryptocurrency mining, spam online message campaigns and many more.
- Some Trojans are basically tools similar to Spyware in the sense that they can monitor your virtual activities and then report the gathered information to their creators. Needless to say, the acquired info could then be used in all kinds of insidious ways.
- A big number of Trojan Horse infections are used as tools for backdooring Ransomware and other infections inside the computers of the users they have attacked. In such cases, it is the delivered infection that usually carries out the main criminal task, with the Trojan being a secondary threat.
- Since the examples above were only that, examples, there could be many, many more potential ways in which Win.Exploit.CVE_2019_0903-6966169-0 Virus or another similar infection could be used by its makers.
Removing Win.Exploit.CVE_2019_0903-6966169-0 Virus manually
We hope that the guide we have prepared and included in this post will be enough to allow those of our readers with Win.Exploit.CVE_2019_0903-6966169-0 Virus in their machines remove the invasive malware. In case you need extra help with the removal, you may want to check out the anti-malware program we have linked on this page and know that you can also write us a comment in case you have any questions related to Win.Exploit.CVE_2019_0903-6966169-0 and its removal.
SUMMARY:
| Name | Win.Exploit.CVE_2019_0903-6966169-0 |
| Type | Trojan |
| Danger Level | High (Trojans are often used as a backdoor for Ransomware) |
| Symptoms | The Trojan could cause your computer to crash and the Blue Screen of Death to appear on your screen. Errors and system slow-downs are also a commonplace during Trojan Horse infections. |
| Distribution Method | The most frequently used methods usually have something to do with pirated software and clickbait ads from shady or illegal sites. |
[add_third_banner]
Remove Win.Exploit.CVE_2019_0903-6966169-0 Virus
1: Preparations
Note: Before you go any further, we advise you to bookmark this page or have it open on a separate device such as your smartphone or another PC. Some of the steps might require you to exit your browser on this PC.
2: Task Manager
Press Ctrl + Shift + Esc to enter the Task Manager. Go to the Tab labeled Processes (Details for Win 8/10). Carefully look through the list of processes that are currently active on you PC.
If any of them seems shady, consumes too much RAM/CPU or has some strange description or no description at all, right-click on it, select Open File Location and delete everything there.
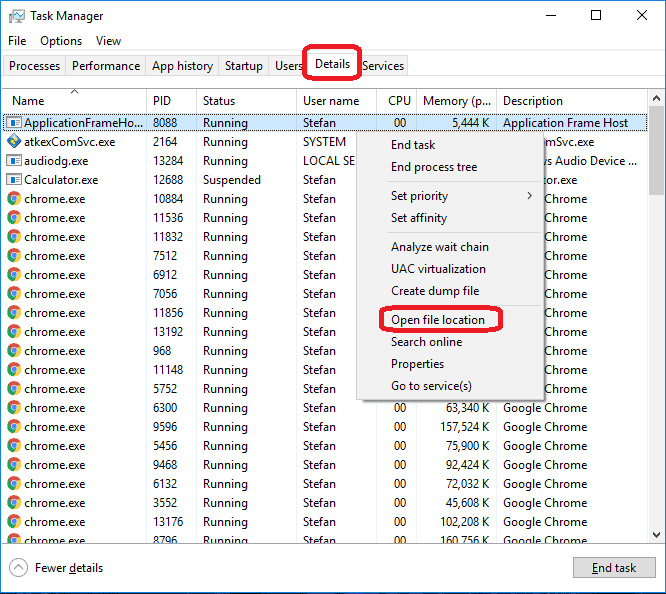
Also, even if you do not delete the files, be sure to stop the process by right-clicking on it and selecting End Process.
3: IP related to Win.Exploit.CVE_2019_0903-6966169-0
Go to c:\windows\system32\drivers\etc\hosts. Open the hosts file with notepad.
Find where it says Localhost and take a look below that.

If you see any IP addresses there (below Localhost) send them to us here, in the comments since they might be coming from the Win.Exploit.CVE_2019_0903-6966169-0.
[add_forth_banner]
4: Disable Startup programs
Re-open the Start Menu and type msconfig.
Click on the first search result. In the next window, go to the Startup tab. If you are on Win 10, it will send you to the Startup part of the task manager instead, as in the picture:

If you see any sketchy/shady looking entries in the list with an unknown manufacturer or a manufacturer name that looks suspicious as there could be a link between them and Win.Exploit.CVE_2019_0903-6966169-0 , disable those programs and select OK.
5: Registry Editor
Press Windows key + R and in the resulting window type regedit.
Now, press Ctrl + F and type the name of the virus.
Delete everything that gets found. If you are not sure about whether to delete something, do not hesitate to ask us in the comments. Keep in mind that if you delete the wrong thing, you might cause all sorts of issues to your PC.
6: Deleting potentially malicious data – Win.Exploit.CVE_2019_0903-6966169-0
Type each of the following locations in the Windows search box and hit enter to open the locations:
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
%Temp%
Delete everything you see in Temp linked to Win.Exploit.CVE_2019_0903-6966169-0 Virus. About the other folders, sort their contents by date and delete only the most recent entries. As always, if you are not sure about something, write to us in the comment section.
Leave a Reply