One Updater in Depth
The malicious programs of the Trojan Horse malware family are extremely stealthy and malicious pieces of software. Sometimes, they can enter the system using browser vulnerabilities or the users’ lack of attention and carelessness. Their authors use unsafe websites filled with malicious ads, or distribute them through unsafe spam email attachments and links. Each time a user visits such sites and clicks on an infected component, a dangerous script immediately installs the Trojan without showing any visible symptoms. The victim usually does not notice anything suspicious since this threat does not show any installation messages, dialog boxes or warning windows. That’s why many users end up with an infection of this type without even knowing it.
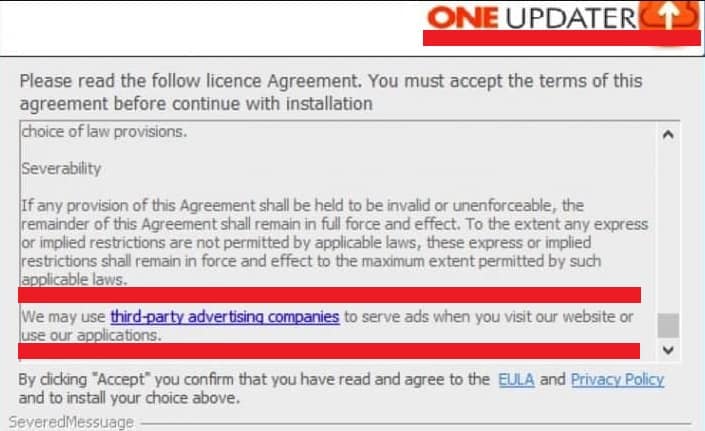
On this page, we will talk about the latest Trojan Horse representative, which the security experts call One Updater Malware. This threat can sometimes install itself along with other unsafe applications or fake software updates or sneak in the system after the users open some infected files, malicious email attachments, fake ads or illegal websites. As most of the infections of its kind, One Updater Malware can enter the system without the users’ knowledge or consent and operate inside the system while remaining fully hidden. The worst part is, once inside, the malware can exploit the system’s resources, launch different harmful activities or open the door for other viruses and malware (such as Ransomware (.Lokas, .Cezor), Spyware, etc.) by creating certain security vulnerabilities.
If you are reading the article from this page because the One Updater Virus has already sneaked inside your system, you should stick with us until the end because there is a detailed Removal Guide on this page, which will show you exactly how to detect and safely remove this nasty Trojan from your system. This is very important because, if not removed on time, the attackers can contact the infected computer with the help of this malicious program and gain unauthorized access to the system or take control over certain programs and processes without your knowledge.
How Dangerous is One Updater ?
Trojans are multifunctional tools which can be programmed to perform many different malicious tasks. That’s why they are the malware of choice for many cybercriminals and are effectively used to perform multiple criminal tasks while hidden in the infected system. If not eliminated on time, pieces of malware like One Updater may corrupt or rewrite files, modify or replace essential system components and even secretly download even ore malware such as Ransomware or Rootkits, which can later be used for blackmailing as well as for other types of harassment. The Trojans can also corrupt the system and make it unusable by deleting key OS files or by formatting all the information stored on the hard drives. Another very harmful ability of those threats is to steal banking details such as credit/debit card numbers, passwords, login credentials and other valuable personal information such as documents, names, etc. They can send the collected data to remote servers and hand it over to the criminals, which can use it to further blackmail and harass their victims in all kinds of ways. One Updater and other infections similar to it may even install a backdoor in the infected machine in order to give remote access to the attacker and allow them to take control over the computer. That’s why the best thing you can do now is take a look at the guide, follow the steps that are given in it and maybe download and install a reliable antivirus/anti-malware program such as the one we have recommended here in case you have no such software at the moment.
SUMMARY:
| Name | One Updater |
| Type | Malware |
| Danger Level | High (Trojans are often used as a backdoor for Ransomware) |
| Symptoms | Usually, the Trojan tries to hide in the system without showing any visible symptoms. |
| Distribution Method | Spam, malicious email attachments, malvertising, cracked software, torrents, sketchy sites, illegal web locations. |
[add_third_banner]
Remove One Updater Malware
1: Preparations
Note: Before you go any further, we advise you to bookmark this page or have it open on a separate device such as your smartphone or another PC. Some of the steps might require you to exit your browser on this PC.
2: Task Manager
Press Ctrl + Shift + Esc to enter the Task Manager. Go to the Tab labeled Processes (Details for Win 8/10). Carefully look through the list of processes that are currently active on you PC.
If any of them seems shady, consumes too much RAM/CPU or has some strange description or no description at all, right-click on it, select Open File Location and delete everything there.

Also, even if you do not delete the files, be sure to stop the process by right-clicking on it and selecting End Process.
3: IP related to One Updater
Go to c:\windows\system32\drivers\etc\hosts. Open the hosts file with notepad.
Find where it says Localhost and take a look below that.

If you see any IP addresses there (below Localhost) send them to us here, in the comments since they might be coming from the One Updater.
[add_forth_banner]
4: Disable Startup programs
Re-open the Start Menu and type msconfig.
Click on the first search result. In the next window, go to the Startup tab. If you are on Win 10, it will send you to the Startup part of the task manager instead, as in the picture:

If you see any sketchy/shady looking entries in the list with an unknown manufacturer or a manufacturer name that looks suspicious as there could be a link between them and One Updater , disable those programs and select OK.
5: Registry Editor
Press Windows key + R and in the resulting window type regedit.
Now, press Ctrl + F and type the name of the virus.
Delete everything that gets found. If you are not sure about whether to delete something, do not hesitate to ask us in the comments. Keep in mind that if you delete the wrong thing, you might cause all sorts of issues to your PC.
6: Deleting potentially malicious data – One Updater
Type each of the following locations in the Windows search box and hit enter to open the locations:
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
%Temp%
Delete everything you see in Temp linked to One Updater Malware. About the other folders, sort their contents by date and delete only the most recent entries. As always, if you are not sure about something, write to us in the comment section.
Leave a Reply