In the text down below, the users that have visited our website will be presented crucial details about a specific dangerous program known as .Cezor virus ransomware.
.Cezor Virus in details
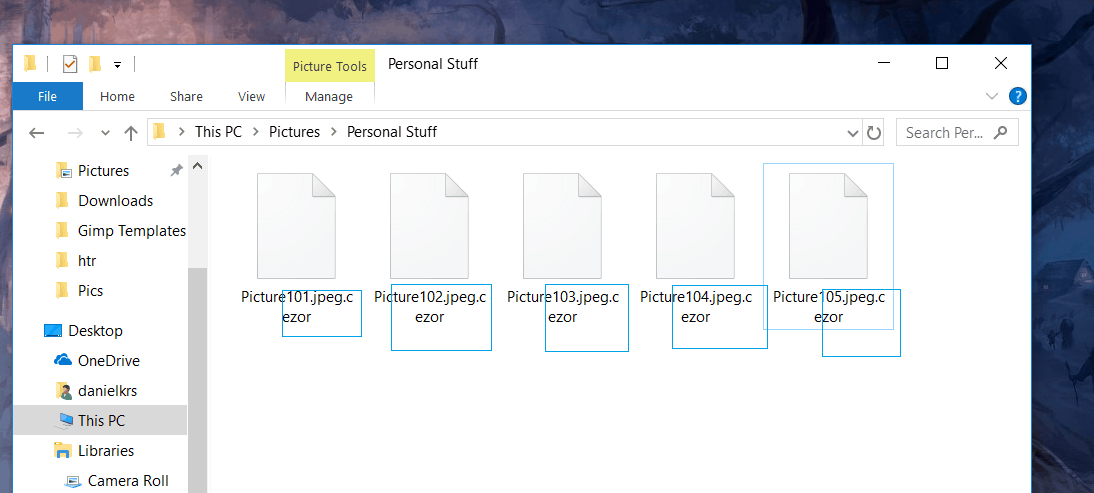
.Cezor viris belongs to the STOP ransomware with notable previous versions like .Besub and .Litar . According to the malware categorization, this virus program is what experts would refer to as Ransomware. This type of dangerous software program is normally capable of encrypting the targeted user’s private data files the moment their device gets infiltrated by the malware. As soon as the encryption is completed, the malware would normally create an intimidating notification message inside of which a ransom payment is requested. Usually, within this notification, certain transaction instructions may be included which are there to explain the exact way the demanded money transaction should be executed. Additional threats that might perhaps be included in the ransom note could tell the affected victim that the refusal to make the requested ransom payment may lead to an utter loss of the locked data. Without a doubt, a lot of you have ended up here since the dangerous .Cezor has gotten hold of your documents. If this is your situation, there is a Ransomware removal guide manual down below which may assist you in handling your issue.
How dangerous is .Cezor virus?
Ransomware may be labeled as a PC virus, yet, it should be noted that it’s a fairly unique kind of malware. Sadly, that is also why there are not many antivirus programs out there that can in fact deal with a Ransomware threat effectively. Perhaps, this is due to the fact that the Ransomware cryptoviruses (the likes of .Cezor) never act by directly damaging anything on your computer. Consequently, none of the processes ran by the Ransomware are to be regarded as shady and potentially hazardous enough to alert the anti-virus software program that the user may have. The encryption Ransomware PC virus employs to stop you from getting to your computer data never really harms the targeted documents. In other words, the noxious malicious cryptovirus is known to employ a non-harmful process and exploit it for a noxious task such as blackmailing. Noticing the infection of Ransomware in time may be accomplished, though it is rather unlikely. The signs one needs to be on the lookout for are slow-down of your PC, decrease in your free Hard disk space and also Ram memory and/or CPU surges in your Task Manager.
Dealing with .Cezor by yourself?
Clearly, the best case scenario regarding any form of virus is to simply keep such virus programs away from your machine. To assist you in improving the security and safety of your computer system, we have prepared a few precaution recommendations.
One very crucial aspect which can contribute to the exposure of your system to potential hazards is what your online activities are and what online sites you typically visit. The instant you notice that you have ended up on some obscure and potentially hazardous web-site, ensure that you close it. Additionally, you must remember to not interact with any junkmail emails along with other sorts of online spam. Ransomware may commonly be discovered inside of a variety of spam email letters and shady social media messages. Just be sure to not click on any hyperlinks included inside this type of online messages and do not download any file attachments whenever you cannot know if it’s safe to do this.
What can really save you from any Ransomware cryptoviruses from now on is making sure to make copies of your most valued documents and saving them on separate devices and locations that do not have connection to your computer system. This way, a Ransomware infection to your Computer will likely be just a mere irritation!
SUMMARY:
| Name | .Cezor |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | A Ransomware will stay silently hidden until it locks-up your files and informs you that a ransom must be paid for their release. |
| Distribution Method | Illegal sites, pirated programs, clickbait ads, spam and more. |
[add_third_banner]
Remove .Cezor Virus Ransomware Guide
1: Preparations
Note: Before you go any further, we advise you to bookmark this page or have it open on a separate device such as your smartphone or another PC. Some of the steps might require you to exit your browser on this PC.
2: Task Manager
Press Ctrl + Shift + Esc to enter the Task Manager. Go to the Tab labeled Processes (Details for Win 8/10). Carefully look through the list of processes that are currently active on you PC.
If any of them seems shady, consumes too much RAM/CPU or has some strange description or no description at all, right-click on it, select Open File Location and delete everything there.

Also, even if you do not delete the files, be sure to stop the process by right-clicking on it and selecting End Process.
3: IP related to .Cezor
Go to c:\windows\system32\drivers\etc\hosts. Open the hosts file with notepad.
Find where it says Localhost and take a look below that.

If you see any IP addresses there (below Localhost) send them to us here, in the comments since they might be coming from the .Cezor.
[add_forth_banner]
4: Disable Startup programs
Re-open the Start Menu and type msconfig.
Click on the first search result. In the next window, go to the Startup tab. If you are on Win 10, it will send you to the Startup part of the task manager instead, as in the picture:

If you see any sketchy/shady looking entries in the list with an unknown manufacturer or a manufacturer name that looks suspicious as there could be a link between them and .Cezor , disable those programs and select OK.
5: Registry Editor
Press Windows key + R and in the resulting window type regedit.
Now, press Ctrl + F and type the name of the virus.
Delete everything that gets found. If you are not sure about whether to delete something, do not hesitate to ask us in the comments. Keep in mind that if you delete the wrong thing, you might cause all sorts of issues to your PC.
6: Deleting potentially malicious data – .Cezor
Type each of the following locations in the Windows search box and hit enter to open the locations:
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
%Temp%
Delete everything you see in Temp linked to .Cezor Ransomware. About the other folders, sort their contents by date and delete only the most recent entries. As always, if you are not sure about something, write to us in the comment section.
7: .Cezor Decryption
The previous steps were all aimed at removing the .Cezor Ransomware from your PC. However, in order to regain access to your files, you will also need to decrypt them or restore them. For that, we have a separate article with detailed instructions on what you have to do in order to unlock your data. Here is a link to that guide.
Leave a Reply