Godlua Backdoor Malware in Depth
The number of web users attacked by a Trojan Horse named Godlua has been rapidly growing and some of the victims have recently contacted our “How to remove” team with a request to help them deal with this nasty infection. This is the reason why this post exists – to assist everyone who has had the misfortune of encountering this advanced computer infection remove it from their computer. In the next lines, you will find some essential information about the nature of the Trojans, as a whole as well as a step-by-step removal guide for the quick and effective elimination of Godlua Malware.
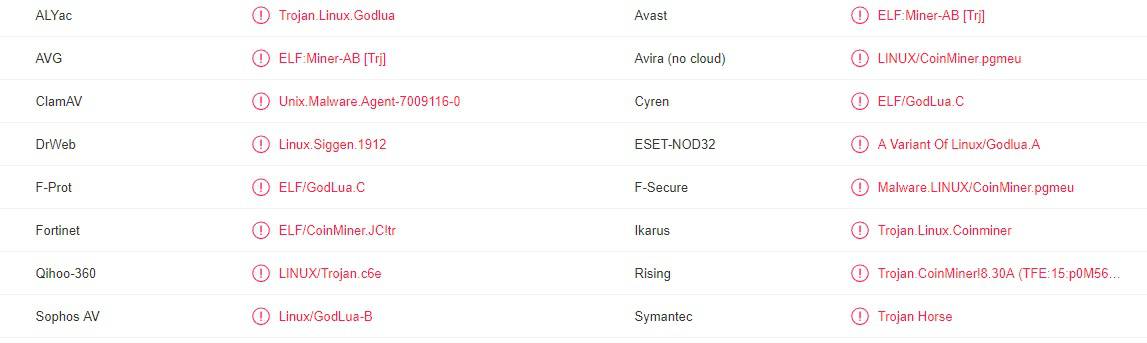
Godlua is backdoor malware that can infect both Windows OS and Linux OS. The malevolent program uses DNS over HTTPS protocol to avoid detection from the antivirus programs. There are two known versions for this malicious software, one targets Windows and the other one targets both OS. One of the main purposes of Godlua is to perform DDoS attacks. The version that can target both Windows and Linux platforms, is being constantly updated, which means that it might include additional features.
Among all the threats that are lurking on the web, the Trojans are some of the most widely spread forms of malware and also some of the most feared ones. As one of the latest representatives of this family of viruses, Godlua Malware isn’t falling behind and could be kept responsible for a number of nasty criminal activities, which usually take place in the background of the system and could hardly be noticed without the help of professional security software. This is because the infection typically hides deep inside the system and uses various types of camouflage in order to remain undetected. When spreading Trojans like this one, the criminals typically mask them as something that the web users might like to click on. This could be a link, an ad, an offer, an image, an email attachment, or some attractive message, which may draw the attention and interest of the potential victim and make them interact with the harmful payload. Sadly, once the users click on the camouflaged transmitter, oftentimes, no symptoms may indicate that a malicious infection has just taken place. The Trojan silently sneaks through and nests deep in the OS where it can start performing the harmful deeds it’s been programmed for. In many cases, it may take some time until the threat launches its malicious activities which is why the moment of the contamination and the moment of the actual attack may be different. However, once the Trojan gets activated, the effects of its activities are usually damaging both to the system and to the user’s virtual privacy.
How Dangerous is Godlua Malware?
That’s a good question the answer to which you should learn here rather than experience it on your own. To start with, you should know that the Trojans are extremely versatile in their abilities to cause harm. They are the malware of choice for many different criminal tasks, because the hackers can program them to perform different malicious activities, depending on what exactly their criminal intentions are. That’s why, if you’ve been infected with Godlua Backdoor Malware, Bearfoos, Trojan.Win32.SEPEH.gen it is perfectly possible that you may face total system corruption while the system of another victim of this virus may get harmed in a different way. For instance, their data may get stolen or they may get spied upon through their webcam or mic. Theft, fraud, espionage, remote access and system resources exploitation are common activities performed by the criminals with the help of this malware. However, the worst of all is the ability of the Trojans to insert other viruses inside the system. Nasty malware such as Ransomware can often find their way inside your computer thanks to the system vulnerabilities that a Trojan may create. That’s why it is extremely important to remove such malware as soon as you detect it.
SUMMARY:
| Name | Godlua |
| Type | Trojan |
| Danger Level | High (Trojans are often used as a backdoor for Ransomware) |
| Symptoms | Typically, Trojans don’t show visible sytmpoms and try to remain hidden in the system. |
| Distribution Method | Spam, fake ads, mislading links, torrents, cracked software, illegal websites. |
[add_third_banner]
Remove Godlua Backdoor Malware
1: Preparations
Note: Before you go any further, we advise you to bookmark this page or have it open on a separate device such as your smartphone or another PC. Some of the steps might require you to exit your browser on this PC.
2: Task Manager
Press Ctrl + Shift + Esc to enter the Task Manager. Go to the Tab labeled Processes (Details for Win 8/10). Carefully look through the list of processes that are currently active on you PC.
If any of them seems shady, consumes too much RAM/CPU or has some strange description or no description at all, right-click on it, select Open File Location and delete everything there.

Also, even if you do not delete the files, be sure to stop the process by right-clicking on it and selecting End Process.
3: IP related to Godlua
Go to c:\windows\system32\drivers\etc\hosts. Open the hosts file with notepad.
Find where it says Localhost and take a look below that.

If you see any IP addresses there (below Localhost) send them to us here, in the comments since they might be coming from the Godlua.
[add_forth_banner]
4: Disable Startup programs
Re-open the Start Menu and type msconfig.
Click on the first search result. In the next window, go to the Startup tab. If you are on Win 10, it will send you to the Startup part of the task manager instead, as in the picture:

If you see any sketchy/shady looking entries in the list with an unknown manufacturer or a manufacturer name that looks suspicious as there could be a link between them and Godlua , disable those programs and select OK.
5: Registry Editor
Press Windows key + R and in the resulting window type regedit.
Now, press Ctrl + F and type the name of the virus.
Delete everything that gets found. If you are not sure about whether to delete something, do not hesitate to ask us in the comments. Keep in mind that if you delete the wrong thing, you might cause all sorts of issues to your PC.
6: Deleting potentially malicious data – Godlua
Type each of the following locations in the Windows search box and hit enter to open the locations:
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
%Temp%
Delete everything you see in Temp linked to Godlua Malware. About the other folders, sort their contents by date and delete only the most recent entries. As always, if you are not sure about something, write to us in the comment section.
Leave a Reply