.Meka Virus
.Meka virus
.Meka virus is malicious software from the Ransomware type that blocks access to user data and demands a ransom. To do that, .Meka virus uses file encryption which renders digital data inaccessible for an indefinite period of time.
.Meka virus is a Ransomware-based infection and in the next lines, we will do our best to help you remove it. The removal guide that you will find below is specifically created for this purpose and will direct you through all the necessary steps. Removing .Meka virus alone, however, may not restore access to the files that it has encrypted. That’s why we’ve also included some file-recovery steps in the guide to help you retrieve some of your encrypted data. We can’t promise they’ll work for all the files but we do encourage you to give them a try as they won’t cost you anything.
What is Meka virus?
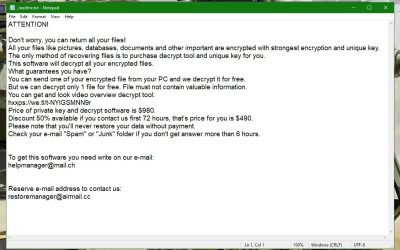
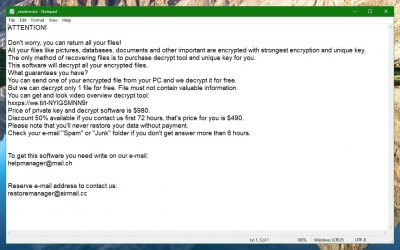
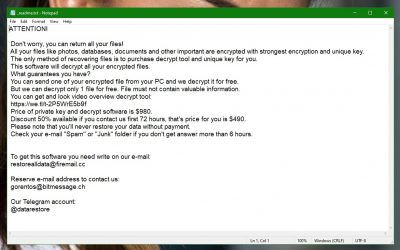
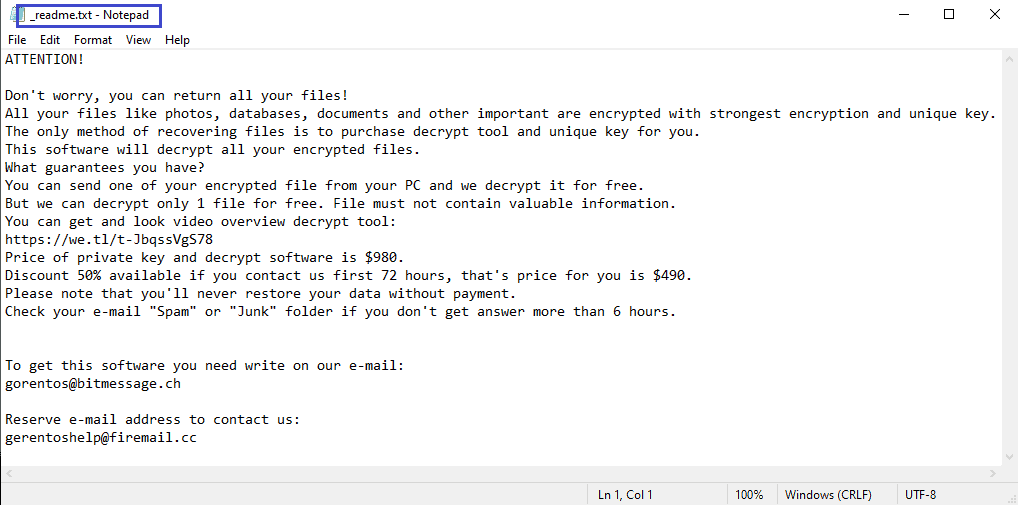
.Meka virus is ransomware, the attacks of which are typically carried out in stealth. After completing the file encryption, the .Meka virus displays a ransom-demanding notification on the victims’ screen.
Cyber security researchers have been warning that the so-called malvertisements are the main sources of Ransomware infections such as .Meka virus. These are different online advertisements, usually banners or pop-up messages, which the hackers use to embed the malicious program in. After clicking on one of these malvertisements, the victim either installs the virus directly on the device or gets redirected to a malicious website from which the viruses can enter the system. Therefore, most reputed security specialists, including our “How to remove” team, advise the web users to avoid interacting with any kind of sketchy ads or random messages, especially those with questionable origin which appear on shady websites.
Unfortunately, this is not the only method for Ransomware distribution. Trojans are another favorite carrier of various infections, including threats like .Meka virus. Once the computer gets compromised by a Trojan, it’s easy for the hackers to download more malware on the targeted computer. Most commonly, the infection occurs when the web users click on malicious emails or their attachments. Sadly, they are often unable to realize when they have received a malicious message since the cyber criminals have learned to mask their spam emails in elaborate ways. For example, you can be looking at a message that appears to be sent by one of your friends or colleagues, or a popular online store. However, in fact, this could be a well-masked Trojan infection, the purpose of which is to deliver the Ransomware inside your system. That’s why it is important that you pay attention to even the smallest details and use reliable antimalware software to stop the hackers from tricking you into downloading the malicious payload. To further improve the security of your online experience and of your system in general, make sure that you frequently install all the needed software updates for your OS and programs.
The .Meka virus file encryption
The .Meka virus file encryption is a process that happens in stealth. The .Meka virus file encryption can only be reversed with a special decryption key which is held by the hackers.
As every Ransomware cryptovirus, .Meka virus is all about extorting people’s money through blackmailing and tricking them into paying ransom for a secret file-decryption key which they may never receive.
When it invades a targeted computer, the malware typically seeks commonly used files and automatically encrypts them without showing visible symptoms. Encryption may be placed over almost any file type, including images, audio or video files, documents, archives, and even system files. After the encryption has successfully rendered all the information on the computer inaccessible, the Ransomware then announces its presence through a ransom note. This note would usually contain information about the ransom amount which the hackers want in exchange for the decryption key, as well as instructions on how to pay. Oftentimes, there may be even a deadline in order to pressure the victims and make them pay sooner.
Taking time to search for solutions, however, may help you not only help you avoid the ransom payment but also it could allow you to remove the infection. That’s why we suggest that you check the removal guide below and give a try to the instructions there.
.Meka Virus Summary:
| Name | .Meka virus |
| Type | Ransomware |
| Danger Level | High (.Meka virus Ransomware encrypts all types of files) |
| Symptoms | .Meka virus Ransomware is hard to detect and aside from increased use of RAM and CPU, there would barely be any other visible red flags. |
| Distribution Method | Most of the time, Trojans get distributed through spam e-mails and social network messages, malicious ads, shady and pirated downloads, questionable torrents and other similar methods. |
.Meka Virus Ransomware Removal Instructions
1: Preparations
Note: Before you go any further, we advise you to bookmark this page or have it open on a separate device such as your smartphone or another PC. Some of the steps might require you to exit your browser on this PC.
2: Task Manager
Press Ctrl + Shift + Esc to enter the Task Manager. Go to the Tab labeled Processes (Details for Win 8/10). Carefully look through the list of processes that are currently active on you PC.
If any of them seems shady, consumes too much RAM/CPU or has some strange description or no description at all, right-click on it, select Open File Location and delete everything there.
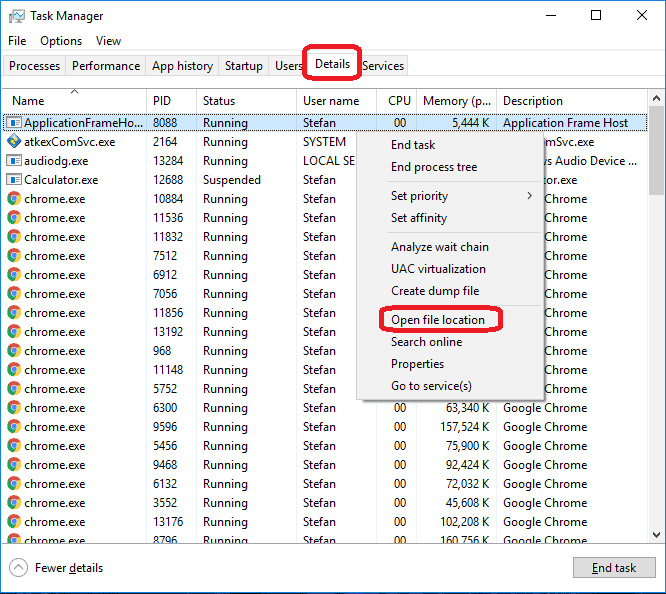
Also, even if you do not delete the files, be sure to stop the process by right-clicking on it and selecting End Process.
3: IP related to .Meka virus
Go to c:\windows\system32\drivers\etc\hosts. Open the hosts file with notepad.
Find where it says Localhost and take a look below that.

If you see any IP addresses there (below Localhost) send them to us here, in the comments since they might be coming from the .Meka virus.
[add_forth_banner]
4: Disable Startup programs
Re-open the Start Menu and type msconfig.
Click on the first search result. In the next window, go to the Startup tab. If you are on Win 10, it will send you to the Startup part of the task manager instead, as in the picture:
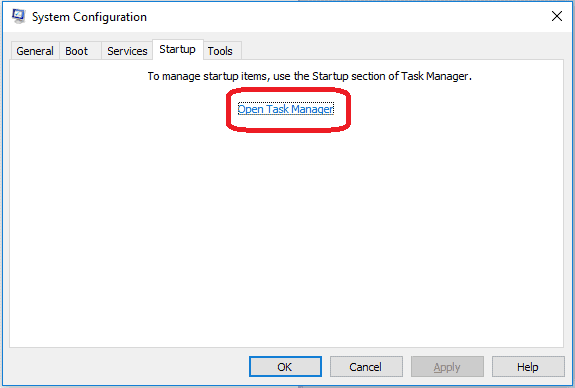
If you see any sketchy/shady looking entries in the list with an unknown manufacturer or a manufacturer name that looks suspicious as there could be a link between them and .Meka virus , disable those programs and select OK.
5: Registry Editor
Press Windows key + R and in the resulting window type regedit.
Now, press Ctrl + F and type the name of the virus.
Delete everything that gets found. If you are not sure about whether to delete something, do not hesitate to ask us in the comments. Keep in mind that if you delete the wrong thing, you might cause all sorts of issues to your PC.
6: Deleting potentially malicious data – .Meka virus
Type each of the following locations in the Windows search box and hit enter to open the locations:
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
%Temp%
Delete everything you see in Temp linked to .Meka virus Ransomware. About the other folders, sort their contents by date and delete only the most recent entries. As always, if you are not sure about something, write to us in the comment section.
7: .Meka virus Decryption
The previous steps were all aimed at removing the .Meka virus Ransomware from your PC. However, in order to regain access to your files, you will also need to decrypt them or restore them. For that, we have a separate article with detailed instructions on what you have to do in order to unlock your data. Here is a link to that guide.