About .Harma Virus
Ransomware is the general term given to a class of malware that is able to block a computer’s screen and/or lock the files in the computer until a ransom is paid for the liberation of the screen and/or the files. The representatives of this category use various ways to block the access to the system, or to the files stored on it by placing complex file encryption on them. For the criminals to have a better chance of getting the ransom money, they typically place scary ransom-demanding notifications on the victim’s screen unexpectedly. Normally, the crooks set a deadline period for the users to pay the ransom, forcing them to send the money immediately after being infected.
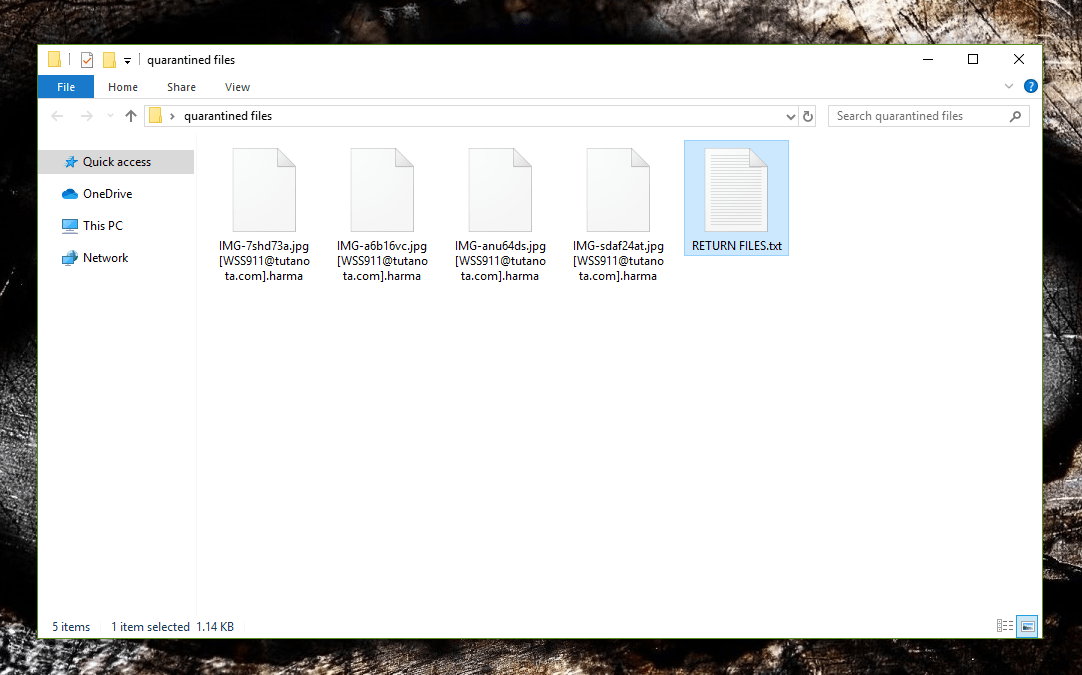
When all of your files have been encrypted .Harma Virus will leave a RETURN FILES.txt for you to find holding instructions for paying the ransom.
All FILES ENCRYPTED “RSA1024”
All YOUR FILES HAVE BEEN ENCRYPTED!!! IF YOU WANT TO RESTORE THEM, WRITE US TO THE E-MAIL [email protected]
IN THE LETTER WRITE YOUR ID, .Harma.HarmaXX
IF YOU ARE NOT ANSWERED, WRITE TO EMAIL: [email protected]
YOUR SECRET KEY WILL BE STORED ON A SERVER 7 DAYS, AFTER 7 DAYS IT MAY BE OVERWRITTEN BY OTHER KEYS, DON’T PULL TIME, WAITING YOUR EMAIL
FREE DECRYPTION FOR PROOF
You can send us up to 1 file for free decryption. The total size of files must be less than 1Mb (non archived), and files should not contain valuable information. (databases,backups, large excel sheets, etc.)
DECRYPTION PROCESS:
When you make sure of decryption possibility transfer the money to our bitcoin wallet. As soon as we receive the money we will send you:
1. Decryption program.
2. Detailed instruction for decryption.
3. And individual keys for decrypting your files.
!WARNING!
Do not rename encrypted files.
Do not try to decrypt your data using third party software, it may cause permanent data loss.
Decryption of your files with the help of third parties may cause increased price (they add their fee to our) or you can become a victim of a scam.
There are two different classes of Ransomware that are very commonly encountered: one that only locks the screen (known as Screen Lockers), and another that encrypts personal information (photos, videos, images, text documents, and others), known as Cryptoviruses. On this page, we will be discussing one of the latest cryptovirus representatives, named .Harma, which, according to the reports, seems to be causing a lot of trouble to a lot of web users. If you are one of the victims of .Harma Ransomware, below, you will find a detailed removal guide, and a professional removal tool, which may help you remove the infection. Our “How to remove” team has also come up with some file-recovery suggestions, which you will find in a separate section of the guide.
.Harma Virus is used to encrypt information through the application of a special file-encoding algorithm. The malware also generates a special decryption key which it stores in the servers of the criminals who stand behind the blackmailing scheme. In this way, the crooks can have full control of the access to the information and, once the ransom is paid, they promise to send the victim the recovery key. In a scenario like this, however, there are no guarantees that you will actually receive the key for your files, let alone, that it will work. Therefore, neither the authorities, nor the reputed security experts advise you to send your money to the hackers. Instead, they recommend that the victims of Ransomware to seek other, more legitimate ways to first remove the infection, and then restore their data with alternative methods when possible.
How can you get infected with a Ransomware like .Harma?
The most modern cryptoviruses, such as .Harma, .Lokas or .Cezor use some advanced methods to enter the system. They usually gain access to the computer through user interaction with infected files or malicious links sent by email or through malicious advertising.
Therefore, you must find a way to prevent your files from being at risk by following all of these tips:
- Back up your most important files on a regular basis. Store the backups on an external drive or on a cloud.
- Avoid clicking on unknown links. These can arrive in email messages, or even in messages sent via social platforms.
- Stay away from shady offers, spam, aggressive ads, and unknown websites and use your common sense when browsing the Internet.
- Constantly update your operating system and applications.
- Avoid installing pirated software and stick only to reputed software developers.
- Install reliable security software, preferably with anti-Ransomware protection and run regular scans with it.
SUMMARY:
| Name | .Harma |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Very few and unnoticeable ones before the ransom notification comes up. |
| Distribution Method | From fake ads and fake system requests to spam emails and contagious web pages. |
[add_third_banner]
Remove .Harma Ransomware Virus
1: Preparations
Note: Before you go any further, we advise you to bookmark this page or have it open on a separate device such as your smartphone or another PC. Some of the steps might require you to exit your browser on this PC.
2: Task Manager
Press Ctrl + Shift + Esc to enter the Task Manager. Go to the Tab labeled Processes (Details for Win 8/10). Carefully look through the list of processes that are currently active on you PC.
If any of them seems shady, consumes too much RAM/CPU or has some strange description or no description at all, right-click on it, select Open File Location and delete everything there.

Also, even if you do not delete the files, be sure to stop the process by right-clicking on it and selecting End Process.
3: IP related to .Harma
Go to c:\windows\system32\drivers\etc\hosts. Open the hosts file with notepad.
Find where it says Localhost and take a look below that.

If you see any IP addresses there (below Localhost) send them to us here, in the comments since they might be coming from the .Harma.
[add_forth_banner]
4: Disable Startup programs
Re-open the Start Menu and type msconfig.
Click on the first search result. In the next window, go to the Startup tab. If you are on Win 10, it will send you to the Startup part of the task manager instead, as in the picture:

If you see any sketchy/shady looking entries in the list with an unknown manufacturer or a manufacturer name that looks suspicious as there could be a link between them and .Harma , disable those programs and select OK.
5: Registry Editor
Press Windows key + R and in the resulting window type regedit.
Now, press Ctrl + F and type the name of the virus.
Delete everything that gets found. If you are not sure about whether to delete something, do not hesitate to ask us in the comments. Keep in mind that if you delete the wrong thing, you might cause all sorts of issues to your PC.
6: Deleting potentially malicious data – .Harma
Type each of the following locations in the Windows search box and hit enter to open the locations:
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
%Temp%
Delete everything you see in Temp linked to .Harma Ransomware. About the other folders, sort their contents by date and delete only the most recent entries. As always, if you are not sure about something, write to us in the comment section.
7: .Harma Decryption
The previous steps were all aimed at removing the .Harma Ransomware from your PC. However, in order to regain access to your files, you will also need to decrypt them or restore them. For that, we have a separate article with detailed instructions on what you have to do in order to unlock your data. Here is a link to that guide.
Leave a Reply