The Godes Virus – Details
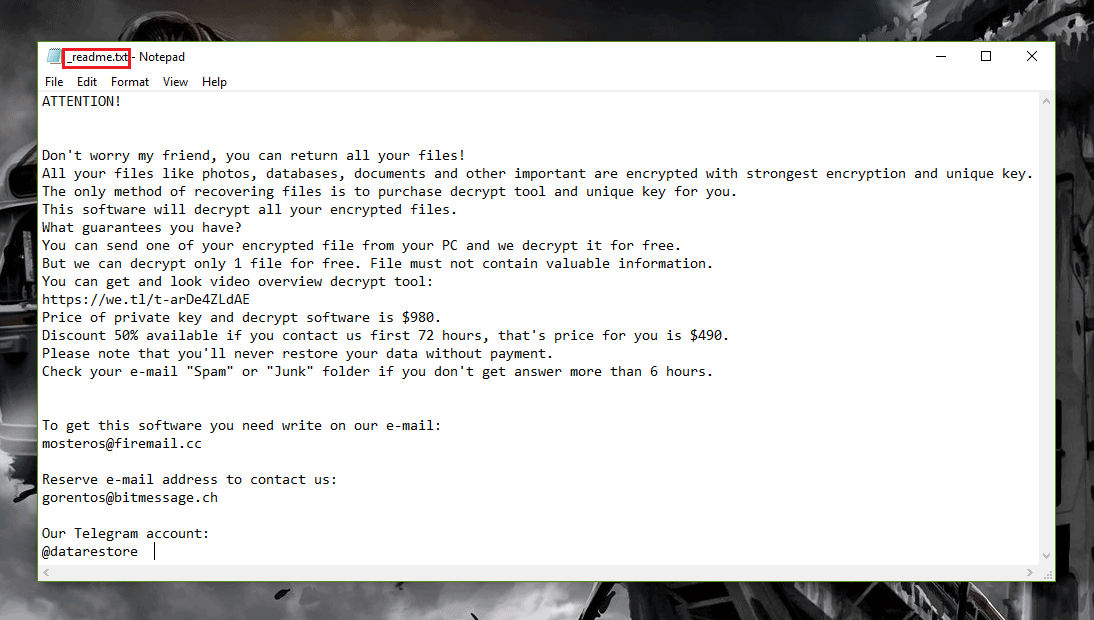
Ransomware is a notorious form of malicious computer programs that are very widespread and can be encountered everywhere on the Internet. Typically, this type of malware gets distributed through pirated computer games, illegally distributed music and movies as well as via spam letter attachments and different forms of social engineering. Currently, there is a significant increase in the number of Ransomware threats that are getting created and pretty much every day several new Ransomware infections get released online. One of the newest additions to this malware family is the nasty .Godes Virus. This infection, similarly to other Ransomware cryptoviruses, uses the so-called data encryption method as means of making the files of its victims inaccessible to their owners. The goal of this action is to allow the criminal behind the virus to later blackmail their victims. The attacked user is supposed to make a sizeable payment to the hacker if they want to get the locked-up files brought back to their accessible state. Usually, the way the user gets informed about the requested payment is through a ransom message that gets displayed on the screen of the infected computer once the encryption has bee fully completed and all targeted data has been made inaccessible by the insidious .Godes Ransomware. Now, if the file that got locked are important to the user, the latter is likely to see the payment as a “necessary evil” that needs to be accepted in order to restore the files. However, the problem is that even if the user chooses to comply to the hackers’ ransom payment instructions from the ransom message, there is no actual guarantee about what would happen to the files after the payment is made. After all, what’s stopping the hacker from refusing to keep their promise to send a decryption key to anyone who pays? That’s right, there is absolutely nothing that a Ransomware cryptovirus victim could do if they pay and do not receive a decryption key for their files. In such instances, the users simply lose some money and are left with no way of opening their files.
.Godes Ransomware is a part of the DJVU Family/STOP Ransomware, like .Lokas or .Cezor.
How can I recover a Godes File?

Sadly, the alternatives to the ransom payment aren’t all that many. Nevertheless, if you are a victim of .Godes Ransomware and do not want to pay anything to the hackers, then we strongly advise you to try out the instructions that you will find in the .Godes Virus removal guide down below. With the help of the guide, you should be able to eliminate .Godes from your machine and your computer will no longer have a cryptovirus in it. The next thing you ought to do is try the data recovery options we have added to our data-recovery section in the guide. Those may not always be as effective as we would hope they are, yet it is still preferable to try the alternatives first before you consider sending some hard-earned money to people who are definitely not very trustworthy and who may easily trick you and lie to you so that you send them your money without really getting any of your files restored.
SUMMARY:
| Name | .Godes |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Ransomware threats are known for the lack of symptoms during the encryption process of the users’ files. |
| Distribution Method | Malicious advertisements,clickbait pop-ups, spam letters, pirated games and so on. |
[add_third_banner]
Remove .Godes Virus Ransomware
1: Preparations
Note: Before you go any further, we advise you to bookmark this page or have it open on a separate device such as your smartphone or another PC. Some of the steps might require you to exit your browser on this PC.
2: Task Manager
Press Ctrl + Shift + Esc to enter the Task Manager. Go to the Tab labeled Processes (Details for Win 8/10). Carefully look through the list of processes that are currently active on you PC.
If any of them seems shady, consumes too much RAM/CPU or has some strange description or no description at all, right-click on it, select Open File Location and delete everything there.

Also, even if you do not delete the files, be sure to stop the process by right-clicking on it and selecting End Process.
3: IP related to .Godes
Go to c:\windows\system32\drivers\etc\hosts. Open the hosts file with notepad.
Find where it says Localhost and take a look below that.

If you see any IP addresses there (below Localhost) send them to us here, in the comments since they might be coming from the .Godes.
[add_forth_banner]
4: Disable Startup programs
Re-open the Start Menu and type msconfig.
Click on the first search result. In the next window, go to the Startup tab. If you are on Win 10, it will send you to the Startup part of the task manager instead, as in the picture:

If you see any sketchy/shady looking entries in the list with an unknown manufacturer or a manufacturer name that looks suspicious as there could be a link between them and .Godes , disable those programs and select OK.
5: Registry Editor
Press Windows key + R and in the resulting window type regedit.
Now, press Ctrl + F and type the name of the virus.
Delete everything that gets found. If you are not sure about whether to delete something, do not hesitate to ask us in the comments. Keep in mind that if you delete the wrong thing, you might cause all sorts of issues to your PC.
6: Deleting potentially malicious data – .Godes
Type each of the following locations in the Windows search box and hit enter to open the locations:
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
%Temp%
Delete everything you see in Temp linked to .Godes Ransomware. About the other folders, sort their contents by date and delete only the most recent entries. As always, if you are not sure about something, write to us in the comment section.
7: .Godes Decryption
The previous steps were all aimed at removing the .Godes Ransomware from your PC. However, in order to regain access to your files, you will also need to decrypt them or restore them. For that, we have a separate article with detailed instructions on what you have to do in order to unlock your data. Here is a link to that guide.
Leave a Reply