The Wannacry Hacker Group in details
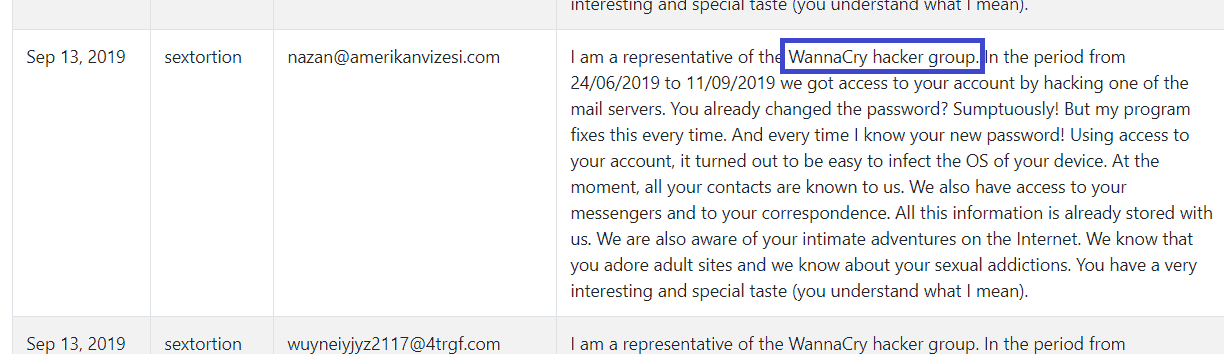
The information you’re about to read includes some very helpful details about a Trojan horse called Wannacry Hacker. This is one of the most recent internet threats and, if you have been compromised by it, on this page, you will learn how to remove this nasty Trojan once and for all. Here, we’ll clarify what you can expect from an infection like Wannacry Hacker and, most importantly, how to detect, and delete it from your system, both manually, and with the help of a professional removal tool. So, in case you need assistance, stay with us until the end, where you will find a comprehensive removal guide, with all the instructions for detecting the stealthy infection.
The Trojan Horses are malicious programs developed by cyber criminals for a variety of damaging purposes. Unfortunately, such malware pieces are very common on the internet, and every two out of three infections that occur on the web are typically Trojan-based. One of the main factors for the popularity of these threats is their flexibility, and the complex techniques they use to spread online, and to infect unsuspecting internet users. Threats such as Wannacry Hacker could be found almost everywhere, and the worst thing is that you can get infected with just one careless click on the malicious transmitter, especially if you aren’t careful with regard to what web materials you interact with. Once inside the machine, these threats would attempt to stay hidden, and quietly carry out all the criminal deeds they have been programmed for. It’s difficult to detect them, and in most cases you wouldn’t even be able to notice that a Trojan Horse is running on your system without the help of reputable antivirus software, since there are usually no visible symptoms that can give the malware away.
The Wannacry Hacker Group should be removed as soon as possible
There is a long list of possible malicious actions that could be carried out in the background of your computer if you don’t remove the Trojan Horse immediately. What precisely a threat like Wannacry Hacker can be used for is completely dependent on the intentions of the hackers who control it. They can erase your information, crash your system, insert other malware such as Ransomware, or other special viruses, and make multiple changes in your system configuration. They can also gain full unauthorized access to your computer, turn it it into a bot, and use it to mine cryptocurrency or spread malware via spam. Another terrible thing a Trojan can do is to spy on its victims, and steal private data. This is possible with the help of a keylogging technique, which helps the hackers record everything that you type on your keyboard, and thus gain access to your login credentials, and internet accounts. Of course, you won’t know what is happening until the crooks use the collected data to steal your money or identity. This is why such threats must be removed quickly. The longer they remain on the system, the worse the consequences could be.
Now, to remove Wannacry Hacker quickly and effectively, we recommend that you follow the directions in the manual below. Please, leave us a comment if you need any help and we will be happy to come to your aid.
SUMMARY:
| Name | Wannacry Hacker |
| Type | Trojan |
| Danger Level | High (Trojans are often used as a backdoor for Ransomware) |
| Symptoms | Trojans are very stealthy and rarely show visible symptoms that can give them away. |
| Distribution Method | Some of the most common transmitters include spam, fake ads, infected emails, torrents, illegal websites, pirated content. |
[add_third_banner]
Remove Wannacry Hacker Group Email Virus
1: Preparations
Note: Before you go any further, we advise you to bookmark this page or have it open on a separate device such as your smartphone or another PC. Some of the steps might require you to exit your browser on this PC.
2: Task Manager
Press Ctrl + Shift + Esc to enter the Task Manager. Go to the Tab labeled Processes (Details for Win 8/10). Carefully look through the list of processes that are currently active on you PC.
If any of them seems shady, consumes too much RAM/CPU or has some strange description or no description at all, right-click on it, select Open File Location and delete everything there.

Also, even if you do not delete the files, be sure to stop the process by right-clicking on it and selecting End Process.
3: IP related to Wannacry Hacker
Go to c:\windows\system32\drivers\etc\hosts. Open the hosts file with notepad.
Find where it says Localhost and take a look below that.

If you see any IP addresses there (below Localhost) send them to us here, in the comments since they might be coming from the Wannacry Hacker.
[add_forth_banner]
4: Disable Startup programs
Re-open the Start Menu and type msconfig.
Click on the first search result. In the next window, go to the Startup tab. If you are on Win 10, it will send you to the Startup part of the task manager instead, as in the picture:

If you see any sketchy/shady looking entries in the list with an unknown manufacturer or a manufacturer name that looks suspicious as there could be a link between them and Wannacry Hacker , disable those programs and select OK.
5: Registry Editor
Press Windows key + R and in the resulting window type regedit.
Now, press Ctrl + F and type the name of the virus.
Delete everything that gets found. If you are not sure about whether to delete something, do not hesitate to ask us in the comments. Keep in mind that if you delete the wrong thing, you might cause all sorts of issues to your PC.
6: Deleting potentially malicious data – Wannacry Hacker
Type each of the following locations in the Windows search box and hit enter to open the locations:
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
%Temp%
Delete everything you see in Temp linked to Wannacry Hacker Trojan. About the other folders, sort their contents by date and delete only the most recent entries. As always, if you are not sure about something, write to us in the comment section.
Leave a Reply