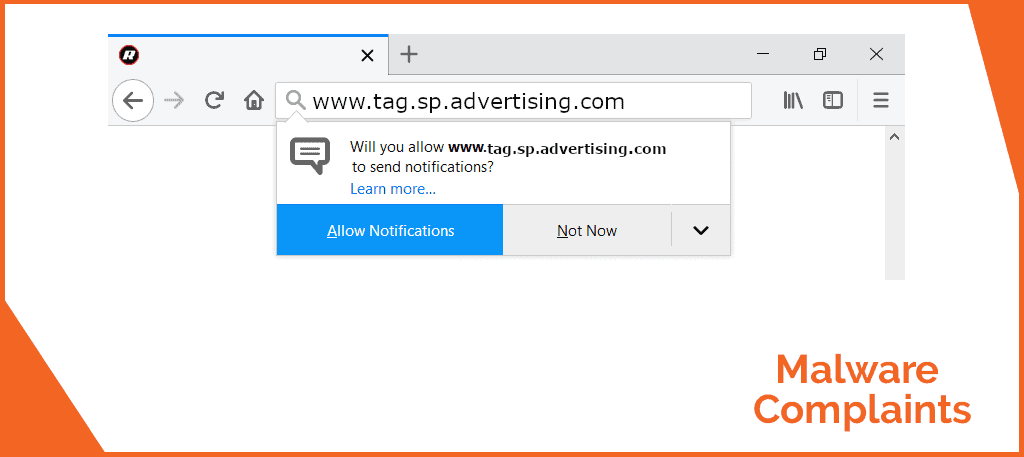
The presence of Tag.sp.advertising.com inside your PC is probably the cause for the big number of unwanted pop-up windows or browser redirects you have been seeing as of late. The term you are looking for is “browser hijacker” and it’s associated with a type of applications that focuses on dirty forms of advertising strategies.
Details about Tag.sp.advertising.com
Tag.sp.advertising.com is very similar to other browser redirects like www1.ecleneue.com and www2.savemax.store. Many users are convinced that browser hijacker applications are made purely for the display of adverts and they are not far from the truth. However, because only a handful of people would generally keep such an application on their machine for long, various browser hijacker programs have some type of functionality included in them. The owners of such pesky apps want users to keep the software for this supposed useful functionality in spite of the adverts.
One particular approach to determine if an application is browser hijacker, is to establish whether the uses it provides are worth enduring the ads it generates. Browser hijacker applications are certainly what one would regard as undesirable when such criteria is applied. The guide written for this article will assist users in the eradication of this potential risk from their computers.
Dealing with Tag.sp.advertising.com
Tag.sp.advertising.com is without a doubt not the only browser hijacker program in existence and unless you learn to identify these apps on time, there’s a good chance you will get infected again. That’s the reason why we’ll try to teach you how to identify them before it’s too late. In fact, most browser hijacker programs are quite akin to one another – surely the pop-ups and ads may differ but the central goal remains the same – display of pay-per-click ads. The ways through which hijackers infect computers are, likewise, quite identical.
Since most browser hijacker programs are not illegal, this means they may easily be spread through legal channels too. With this information in your mind, please remember that simply because your antivirus program tells you that a specific executable does not contain any viruses, this doesn’t necessarily mean you can just install the latter without paying any attention to what it contains. A program bundle can be virus free, yet it can still cause you frustration for hours to come. Just because a piece of software is legal doesn’t mean it’s helpful or that it should be allowed to remain your computer and the browser hijackers are only one of many examples of unwanted software. The majority of such programs fall under the category of PUPs – potentially unwanted programs.
As for the undesirable program itself, it is generally hidden under some guise – quite often, you can find it bundled with the installation file of a 3rd party program – a method generally referred to as file-bundling. Software bundles are the means with the help of which many browser hijacker programs can get inside a computer from a single source. If you pay attention to the installation menu of a file bundle, however, you could easily spot the presence of added programs and stop them before they could cause problems. The most likely spot to conceal the auto-agree option for added software components is the Advanced installation options of the installer. Anybody using the Quick option will also get the added installs – this includes the browser hijacker. Opting for the Advanced installation will allow you to block any unwanted program.
SUMMARY:
| Name | Tag.sp.advertising.com |
| Type | Browser Hijacker |
| Danger Level | Medium (nowhere near threats like Ransomware, but still a security risk) |
| Symptoms | The invasive ads that show up on every site and page are a sure sign of the installation of a hijacker in your computer. |
| Distribution Method | Spam messages with sketchy attachments and clickbait download prompts as well as software bundles. |
| Ip | 152.195.32.163 |
[add_third_banner]
How To Remove Tag.sp.advertising.com “Virus”
Tag.sp.advertising.com Android Removal guide
Tag.sp.advertising.com Mac Removal guide.
The following guide is only for windows users, it will help our readers get rid of the unpleasant Tag.sp.advertising.com software. Follow the instructions and complete each step for best results. If you have any questions, feel free to ask them using our comment section down below.
Preparation: Entering Safe Mode and Revealing Hidden Files and Folders
Before you proceed with the actual removal instructions, you will need to take two extra steps in order to ensure that the guide has maximum effect.
For best results, we advise our readers to boot into Safe Mode prior to attempting to remove Tag.sp.advertising.com. If you do not know how to do that, here is a separate How to Enter Safe Mode guide.
Also, in order to be able to see any potentially undesirable files, you should reveal any hidden files and folders on your PC – here is how to do that.
Removing Tag.sp.advertising.com From Windows
Step 1: Checking the Task Manager
Before we start deleting files related to Tag.sp.advertising.com we want to make sure that all services related to the viruses are killed before we proceed. Open your Task Manager by using the Ctrl + Shift + Esc keys and go to the Processes tab. Look for any suspicious processes. For example, any unfamiliar process that uses high amounts of RAM and/or CPU. If you aren’t sure if a certain process comes from malware, tell us in the comments.
Right-click on any process that you consider shady and select Open File Location. Delete anything from the file location of the process.

Step 2: Disabling Startup programs
Use the Winkey + R keyboard combination to open the Run search bar and type msconfig. Hit Enter and in the newly opened window, go to the Startup tab. There, look for suspicious entries with unknown manufacturer or ones that have the name Tag.sp.advertising.com on them. Right-click on those, and select disable.

Step 3: Uninstalling unwanted programs
Go to Start Menu > Control Panel > Uninstall a Program. Click on Installed On to sort the entries by date from most recent to oldest and look through the programs that come at the top of the list. Right-click on any entries that appear shady and unwanted and then select Uninstall to remove them from your PC. If you see the name Tag.sp.advertising.com in the list of programs, be sure to remove the software without hesitation.

Step 4: Checking for shady IP’s
Open your Start Menu and copy-paste notepad %windir%/system32/Drivers/etc/hosts in the search bar. In the notepad file, look below Localhost and see if there are any IP addresses there. If there are some, send them to us in the comments and we will tell you if you should take any action. [add_forth_banner]
Step 5: Cleaning-up the browsers
You will also have to uninstall any undesirable browser extensions from your browser programs. Here’s how to do that for some of the more popular browsers:
Getting rid of Tag.sp.advertising.com from Chrome
Open Chrome and open its main menu. Go to More Tools > Extensions. Look through the list of extensions and uninstall any that you think could be suspicious. To remove them – click on the trash can icon next to each extension.
You can also use a specialized Chrome CleanUp tool if you cannot manually remove a certain extension. Here is an article where you can learn more about the CleanUp tool.
Removing Tag.sp.advertising.com From Firefox
Open Firefox and go to its Menu. Select the Add-ons button.From the left panel, select Extensions and take a look at the different entries. Remove any of the that might be unwanted.
Removing Tag.sp.advertising.com From Windows Internet Explorer
Once you open your IE browser, click on the Tools button at the top-right corner of the program and from the drop-down menu select Manage Add-ons. Check each one of the four different groups of add-ons and search for anything that seems undesirable. If you find anything, click on it and them select Remove.
Removing Tag.sp.advertising.com From Windows Edge
Open the main menu of Microsoft Edge and go to Extensions. Find the extensions that you believe could be unwanted and right-click on them. Then, select Uninstall.
Step 6: Checking the Registry Editor
Open the Run search bar again and type regedit in it. Hit Enter and once the Registry Editor opens press Ctrl + F. In the search field type Tag.sp.advertising.com and click on Find Next. Tell us in the comments if any results came up when you searched for Tag.sp.advertising.com in your PC’s Registry.

Step 7: Deleting recent entries
For this step, you will have to open your Start Menu and copy-paste the following lines, one by one:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Hit Enter after each one to open a file directory. In the directories, delete the most recent entries that you find there. In the Temp folder, delete all files.

Step 8: System Restore
In order to be fully sure that the unwanted software has been removed from your machine, you can also try using a Restore Point to roll back your system its last stable configuration. However, in order to do that, you would have to previously had had a restore point created. On most systems, such points get created automatically but this isn’t always the case.
- If you want to learn how to configure System Restore and how to manually create Restore Points, follow this link.
- Open your Start Menu and type System Restore.
- Click on the first result – a setup wizard should open.
- Read the brief description of the process and select Next.
- Now, choose a restore from the presented list. You can also check the Show more restore points option in order to reveal any other restore points that might be saved on your PC.
- Click on Scan for affected programs to see what programs will get deleted or restored after you use the Restore Point. (optional)

- Click on next and take and then select Finish.
- A warning window will appear telling you that once the process starts, it shouldn’t be interrupted. Select Yes and be patient as this might take some time. Do not do anything on your PC throughout the duration of the process.
Step 9: Windows Refresh/Reset
Use this method only if nothing else has worked so far as it is a last resort option. If you do not know how to do it, this separate guide will give you the information that you need.
Leave a Reply