About .NHCR Virus File

Inside the current article, you will learn some crucial specifics about a computer virus known as .NHCR. This cyber threat is part of the Ransomware class, meaning that it’s able to lock all your essential documents. Once the files have been made inaccessible by the malware code, a message gets displayed on the PC screen which informs the user about the Ransomware invasion and also demands a money transaction from them.
The actual purpose of this sort of Ransomware notification would be to provide you with information on how you must make the money payment to the hacker that’s attacked your machine via the Ransomware virus. This insidious practice is actually a method of harassing the targeted user into paying a ransom for a unique decryption key which could decrypt the locked data. Normally, the malware victim is threatened that they wouldn’t be able to regain access to their files again should they choose to not pay the ransom. If you’re one of the numerous users that are being harassed by .NHCR, we could provide you with some additional information concerning the insidious Ransomware along with a Ransomware removal guide located at the bottom of this article.
How .NHCR Virus File Works
One of the main factors that contribute to the high success rate of Ransomware cryptoviruses like .NHCR, .Rectot, .Ferosas, .Radman is their stealth and ability to operate without getting spotted by any security software. Even in the event that there is a top-notch protection tool on the Machine, the ransomware victim may still not be able to identify the malware attack in time. This all stems from the process which is used to lock the data files – encryption isn’t actually an inherently malicious technique. Unfortunately, due to this, the chances of detecting a Ransomware before it gets far too late are really slim as you, in most cases, cannot depend upon your anti-malware tool. Hence, if you would like to possibly have the ability to detect a Ransomware virus infection on time, you have to be highly attentive and observant for the indicators it might cause.
As an example, in the event that you think that your PC is operating in a unusual way, have a look at the Task Manager and see whether there are virtual memory or Processor use spikes that could give away a potential infection. In addition, during the file encryption, Ransomware viruses necessitate free physical memory that could, too, serve as a warning sign that something suspicious is taking place on your Machine.
In such a case, it might actually be beneficial if you own a less powerful computer machine since the mentioned signs and symptoms may be easier to spot and also the duration of the data encryption process would be prolonged providing you with a bigger window of opportunity to take action. If you happen to see anything suspicious taking place on your PC, power down the system immediately and, if possible, have a specialist take a look at the computer.
.NHCR SUMMARY:
| Name | .NHCR |
| Type | Ransomware |
| Danger Level | High (.NHCR Ransomware encrypts all types of files) |
| Symptoms | .NHCR Ransomware is hard to detect and aside from increased use of RAM and CPU, there would barely be any other visible red flags. |
| Distribution Method | Most of the time, Trojans get distributed through spam e-mails and social network messages, malicious ads, shady and pirated downloads, questionable torrents and other similar methods. |
[add_third_banner]
Remove .NHCR Virus File Ransomware
1: Preparations
Note: Before you go any further, we advise you to bookmark this page or have it open on a separate device such as your smartphone or another PC. Some of the steps might require you to exit your browser on this PC.
2: Task Manager
Press Ctrl + Shift + Esc to enter the Task Manager. Go to the Tab labeled Processes (Details for Win 8/10). Carefully look through the list of processes that are currently active on you PC.
If any of them seems shady, consumes too much RAM/CPU or has some strange description or no description at all, right-click on it, select Open File Location and delete everything there.

Also, even if you do not delete the files, be sure to stop the process by right-clicking on it and selecting End Process.
3: IP related to .NHCR
Go to c:\windows\system32\drivers\etc\hosts. Open the hosts file with notepad.
Find where it says Localhost and take a look below that.

If you see any IP addresses there (below Localhost) send them to us here, in the comments since they might be coming from the .NHCR.
[add_forth_banner]
4: Disable Startup programs
Re-open the Start Menu and type msconfig.
Click on the first search result. In the next window, go to the Startup tab. If you are on Win 10, it will send you to the Startup part of the task manager instead, as in the picture:

If you see any sketchy/shady looking entries in the list with an unknown manufacturer or a manufacturer name that looks suspicious as there could be a link between them and .NHCR , disable those programs and select OK.
5: Registry Editor
Press Windows key + R and in the resulting window type regedit.
Now, press Ctrl + F and type the name of the virus.
Delete everything that gets found. If you are not sure about whether to delete something, do not hesitate to ask us in the comments. Keep in mind that if you delete the wrong thing, you might cause all sorts of issues to your PC.
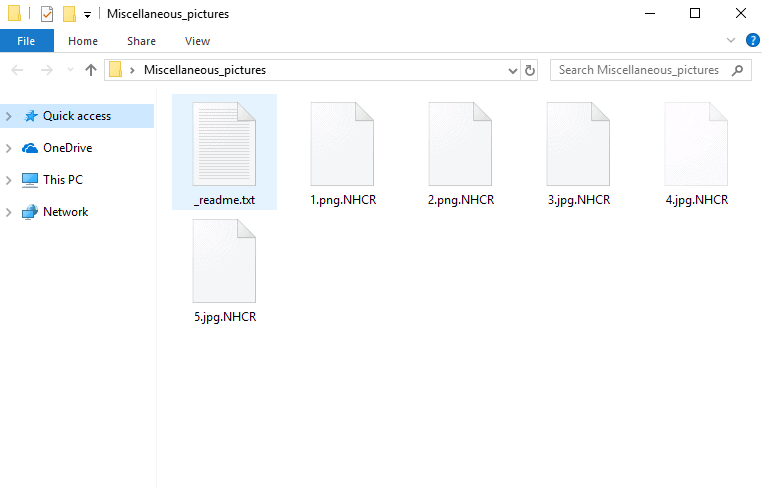
6: Deleting potentially malicious data – .NHCR
Type each of the following locations in the Windows search box and hit enter to open the locations:
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
%Temp%
Delete everything you see in Temp linked to .NHCR Ransomware. About the other folders, sort their contents by date and delete only the most recent entries. As always, if you are not sure about something, write to us in the comment section.
7: .NHCR Decryption
The previous steps were all aimed at removing the .NHCR Ransomware from your PC. However, in order to regain access to your files, you will also need to decrypt them or restore them. For that, we have a separate article with detailed instructions on what you have to do in order to unlock your data. Here is a link to that guide.
Leave a Reply