.Ferosas File Ransomware in Depth
In case you desire to find out more regarding a recently created computer virus program known as .Ferosas, the following paragraphs will offer you some important and beneficial details with regards to it. The malware threat which is going to be the focus of our article is what experts regard as Ransomware. The thing that makes Ransomware viruses like .Ferosas,.Radman, .Dotmap, different from the other malware forms is the fact that they apply a highly-advanced encryption procedure so as to render the targeted user’s documents unavailable. Once all of those files have been locked up by .Ferosas, the victim is displayed a notification message which has been created by the malware. Inside the message, a money payment is demanded. Generally, the dreaded notification message the computer virus shows features instructions about the way the required ransom is to be transfered. Additionally, the cyber criminals often resort to threats towards the ransomware victim concerning the future of the documents in order to evoke fear inside the user, making them more likely to agree to carry out the transaction. If you have recently had .Ferosas infiltrate your PC system, we suggest that you cautiously read through the the remainder of this article and also the manual that has been added below so to be able to get a better understanding of what you’re actually dealing with and how you can possibly deal with this situation.
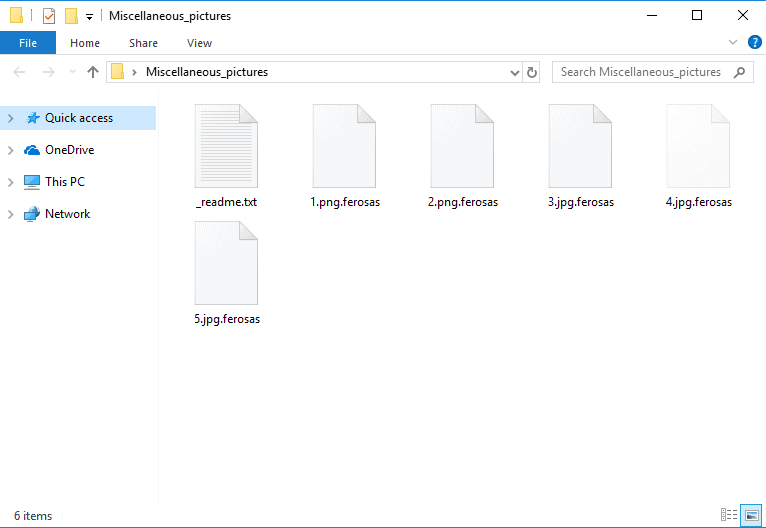
After the infection take over your system, the virus drops a _readme.txt file with instructions for you to follow:

How .Ferosas File Ransomware Works
For those of our readers that wish to effectively fight such a cryptovirus threat, you’d have to be familiar with its main traits.
A vital element which ought to be pointed out concerning Ransomware is that the way it functions is fairly different from how other virus sorts operate. If a Ransomware infects your system, it’d typically issue a system scan, seeking out certain data file types. Normally, the malware virus will be in search of pictures, written docs, audio or video files and others. When the scan is accomplished, each one of the targeted file documents gets copied by the Ransomware. After a copy gets made, the initial document gets removed by the computer virus. The file copies are left intact and are indistinguishable from the original personal data, however, they are made unavailable to the cryptovirus’ victim since they have been secured via a complex code. The procedure we’ve just described is known as encryption and is the thing that allows hackers who work with Ransomware to gain money from the targeted users by blackmailing them using the locked-up personal documents as leverage.
Can I Remove Myself .Ferosas File Ransomware?
What’s most bothering with regards to the file encryption procedure is the fact a lot of system security applications do not see it as a potential hazard no matter whether it’s ran by a regular application or by a Ransomware virus, which, in turn, makes it even more difficult to notice and take care of this sort of virus infections.
Typically, it isn’t impossible to manually spot the ongoing Ransomware attack. However,this could only happen if you are always looking for certain particular red flags like increased use of ram and cpu time. And even if you are super vigilant, you may still not notice anything before a ransom message gets shown on your screen and you are then forced to choose between paying the money to the blackmailers or opting for an alternative solution such as the one below.
.Ferosas SUMMARY:
| Name | .Ferosas |
| Type | Ransomware |
| Danger Level | High (.Ferosas Ransomware encrypts all types of files) |
| Symptoms | .Ferosas Ransomware is hard to detect and aside from increased use of RAM and CPU, there would barely be any other visible red flags. |
| Distribution Method | Most of the time, Trojans get distributed through spam e-mails and social network messages, malicious ads, shady and pirated downloads, questionable torrents and other similar methods. |
[add_third_banner]
Remove .Ferosas File Virus Ransomware
1: Preparations
Note: Before you go any further, we advise you to bookmark this page or have it open on a separate device such as your smartphone or another PC. Some of the steps might require you to exit your browser on this PC.
2: Task Manager
Press Ctrl + Shift + Esc to enter the Task Manager. Go to the Tab labeled Processes (Details for Win 8/10). Carefully look through the list of processes that are currently active on you PC.
If any of them seems shady, consumes too much RAM/CPU or has some strange description or no description at all, right-click on it, select Open File Location and delete everything there.

Also, even if you do not delete the files, be sure to stop the process by right-clicking on it and selecting End Process.
3: IP related to .Ferosas
Go to c:\windows\system32\drivers\etc\hosts. Open the hosts file with notepad.
Find where it says Localhost and take a look below that.

If you see any IP addresses there (below Localhost) send them to us here, in the comments since they might be coming from the .Ferosas.
[add_forth_banner]
4: Disable Startup programs
Re-open the Start Menu and type msconfig.
Click on the first search result. In the next window, go to the Startup tab. If you are on Win 10, it will send you to the Startup part of the task manager instead, as in the picture:

If you see any sketchy/shady looking entries in the list with an unknown manufacturer or a manufacturer name that looks suspicious as there could be a link between them and .Ferosas , disable those programs and select OK.
5: Registry Editor
Press Windows key + R and in the resulting window type regedit.
Now, press Ctrl + F and type the name of the virus.
Delete everything that gets found. If you are not sure about whether to delete something, do not hesitate to ask us in the comments. Keep in mind that if you delete the wrong thing, you might cause all sorts of issues to your PC.
6: Deleting potentially malicious data – .Ferosas
Type each of the following locations in the Windows search box and hit enter to open the locations:
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
%Temp%
Delete everything you see in Temp linked to .Ferosas Ransomware. About the other folders, sort their contents by date and delete only the most recent entries. As always, if you are not sure about something, write to us in the comment section.
7: .Ferosas Decryption
The previous steps were all aimed at removing the .Ferosas Ransomware from your PC. However, in order to regain access to your files, you will also need to decrypt them or restore them. For that, we have a separate article with detailed instructions on what you have to do in order to unlock your data. Here is a link to that guide.
Leave a Reply