There are many things that can go wrong with a computer system, and oftentimes the problem would be related to some form of unwanted or dangerous program. However, not all unwanted software is necessarily a Trojan, a Ransomware, or some other kind of computer virus. In fact,in many cases, the undesirable software that users face is something that isn’t really meant to harm their systems and compromise their computer. One good example of that are the browser hijackers – annoying pieces of software that are typically intended to operate as browser extension-like apps. The main difference between them and any actual browser add-on, however, is the fact that they may be rather intrusive and unpleasant to have in your Chrome, Safari, Edge or Firefox browser (or inside some other browsing program).
About The Laubeyrietechnology.com Virus
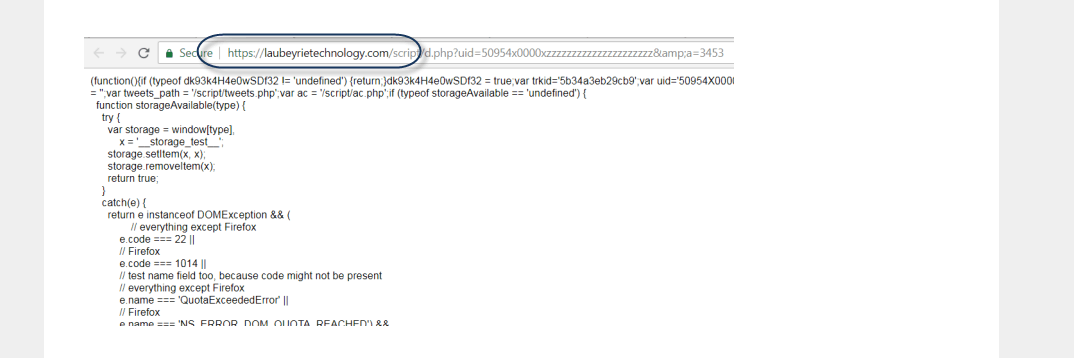
If your homepage is Laubeyrietechnology.com, your search engine has been replaced, and you get page-redirected to advertisement-heavy sites, then you most probably have one of the more recently released hijackers. One that seems to be primarily focused on popularizing the Laubeyrietechnology.com page. This, however, doesn’t mean that other sites, products, and services won’t start to get promoted on your screen if this hijacker (which we will refer to as Laubeyrietechnology.com) is in your computer right now. Obviously, it can be quite frustrating if every time you open your browser you start to get unceremoniously redirected to pages you did not intend to visit and shown big banners and other advertising messages that cover most of your screen and prevent you from using your browser normally. However, we should say that the irritation coming from hijackers may not always be that severe. Sometimes, such apps would simply replace the homepage and maybe the search engine and would leave it at that. This leads to a lot of users actually allowing the hijacker to stay in their browser instead of taking action to remove it. After all, if it isn’t too bothering and it isn’t a virus, there isn’t really a need to get rid of it, right? Well, while it is true that a hijacker like Laubeyrietechnology.com or www1.ecleneue.com wouldn’t try to encrypt your files like a Ransomware cryptovirus or make harmful changes in your system like a Trojan, it’s still best if you make sure that the intrusive app gets eliminated as soon as possible. The reason for that is the uncontrollable nature of these pieces of software – they don’t typically ask you what ads you want to get shown on your screen or if you’d prefer to put an end to the ad-generation as a whole. They also tend to enforce the new search engine and homepage, without letting the user to choose ones preferred by them. And while none of this is harmful in and of itself, it is possible that the random redirects, ad pop-ups, and intrusive banners may sometimes land you on unsafe online locations – sites filled with unreliable content that you should definitely stay away from. It is, therefore, best if you make sure to uninstall Laubeyrietechnology.com and remove the Laubeyrietechnology.com page from your browser. To do this quickly and easily, we suggest you use the guide that you will find right below.
SUMMARY:
| Name | Laubeyrietechnology.com |
| Type | Browser Hijacker |
| Danger Level | Medium (nowhere near threats like Ransomware, but still a security risk) |
| Symptoms | Hijackers are easily-noticeable due to their intrusive adverts. |
| Distribution Method | Hijackers are distributed through the help of other program’s installers. |
[add_third_banner]
How To Remove Laubeyrietechnology.com Pop up Ads
Laubeyrietechnology.com Android Removal guide
Laubeyrietechnology.com Mac Removal guide.
The following guide is only for windows users, it will help our readers get rid of the unpleasant Laubeyrietechnology.com software. Follow the instructions and complete each step for best results. If you have any questions, feel free to ask them using our comment section down below.
Preparation: Entering Safe Mode and Revealing Hidden Files and Folders
Before you proceed with the actual removal instructions, you will need to take two extra steps in order to ensure that the guide has maximum effect.
For best results, we advise our readers to boot into Safe Mode prior to attempting to remove Laubeyrietechnology.com. If you do not know how to do that, here is a separate How to Enter Safe Mode guide.
Also, in order to be able to see any potentially undesirable files, you should reveal any hidden files and folders on your PC – here is how to do that.
Removing Laubeyrietechnology.com From Windows
Step 1: Checking the Task Manager
Before we start deleting files related to Laubeyrietechnology.com we want to make sure that all services related to the viruses are killed before we proceed. Open your Task Manager by using the Ctrl + Shift + Esc keys and go to the Processes tab. Look for any suspicious processes. For example, any unfamiliar process that uses high amounts of RAM and/or CPU. If you aren’t sure if a certain process comes from malware, tell us in the comments.
Right-click on any process that you consider shady and select Open File Location. Delete anything from the file location of the process.

Step 2: Disabling Startup programs
Use the Winkey + R keyboard combination to open the Run search bar and type msconfig. Hit Enter and in the newly opened window, go to the Startup tab. There, look for suspicious entries with unknown manufacturer or ones that have the name Laubeyrietechnology.com on them. Right-click on those, and select disable.

Step 3: Uninstalling unwanted programs
Go to Start Menu > Control Panel > Uninstall a Program. Click on Installed On to sort the entries by date from most recent to oldest and look through the programs that come at the top of the list. Right-click on any entries that appear shady and unwanted and then select Uninstall to remove them from your PC. If you see the name Laubeyrietechnology.com in the list of programs, be sure to remove the software without hesitation.

Step 4: Checking for shady IP’s
Open your Start Menu and copy-paste notepad %windir%/system32/Drivers/etc/hosts in the search bar. In the notepad file, look below Localhost and see if there are any IP addresses there. If there are some, send them to us in the comments and we will tell you if you should take any action. [add_forth_banner]
Step 5: Cleaning-up the browsers
You will also have to uninstall any undesirable browser extensions from your browser programs. Here’s how to do that for some of the more popular browsers:
Getting rid of Laubeyrietechnology.com from Chrome
Open Chrome and open its main menu. Go to More Tools > Extensions. Look through the list of extensions and uninstall any that you think could be suspicious. To remove them – click on the trash can icon next to each extension.
You can also use a specialized Chrome CleanUp tool if you cannot manually remove a certain extension. Here is an article where you can learn more about the CleanUp tool.
Removing Laubeyrietechnology.com From Firefox
Open Firefox and go to its Menu. Select the Add-ons button.From the left panel, select Extensions and take a look at the different entries. Remove any of the that might be unwanted.
Removing Laubeyrietechnology.com From Windows Internet Explorer
Once you open your IE browser, click on the Tools button at the top-right corner of the program and from the drop-down menu select Manage Add-ons. Check each one of the four different groups of add-ons and search for anything that seems undesirable. If you find anything, click on it and them select Remove.
Removing Laubeyrietechnology.com From Windows Edge
Open the main menu of Microsoft Edge and go to Extensions. Find the extensions that you believe could be unwanted and right-click on them. Then, select Uninstall.
Step 6: Checking the Registry Editor
Open the Run search bar again and type regedit in it. Hit Enter and once the Registry Editor opens press Ctrl + F. In the search field type Laubeyrietechnology.com and click on Find Next. Tell us in the comments if any results came up when you searched for Laubeyrietechnology.com in your PC’s Registry.

Step 7: Deleting recent entries
For this step, you will have to open your Start Menu and copy-paste the following lines, one by one:
- %AppData%
- %LocalAppData%
- %ProgramData%
- %WinDir%
- %Temp%
Hit Enter after each one to open a file directory. In the directories, delete the most recent entries that you find there. In the Temp folder, delete all files.

Step 8: System Restore
In order to be fully sure that the unwanted software has been removed from your machine, you can also try using a Restore Point to roll back your system its last stable configuration. However, in order to do that, you would have to previously had had a restore point created. On most systems, such points get created automatically but this isn’t always the case.
- If you want to learn how to configure System Restore and how to manually create Restore Points, follow this link.
- Open your Start Menu and type System Restore.
- Click on the first result – a setup wizard should open.
- Read the brief description of the process and select Next.
- Now, choose a restore from the presented list. You can also check the Show more restore points option in order to reveal any other restore points that might be saved on your PC.
- Click on Scan for affected programs to see what programs will get deleted or restored after you use the Restore Point. (optional)

- Click on next and take and then select Finish.
- A warning window will appear telling you that once the process starts, it shouldn’t be interrupted. Select Yes and be patient as this might take some time. Do not do anything on your PC throughout the duration of the process.
Step 9: Windows Refresh/Reset
Use this method only if nothing else has worked so far as it is a last resort option. If you do not know how to do it, this separate guide will give you the information that you need.
Leave a Reply