The Jeanson Ancheta Email Virus in Depth
One of the toughest things when it comes to dealing with Trojan Horse infections like Jeanson Ancheta Email Virus, Xml/w97m/dropexe.a, Drive by exploit is to detect them. These threats are very good at staying hidden, as they use different types of disguise so that no one can spot and uncover them. They can secretly infect you, and with the same success they can hide deep within your system, and execute various malicious operations without you even knowing that you’ve been compromised. If you suspect that a threat named Jeanson Ancheta has sneaked inside your computer, however, in the next lines, we will help you to remove it.
Malicious programs like this one use different deceiving techniques to get inside your system. They can mask themselves as all sorts of random internet content, including advertisements, different apps, web links, email attachments, torrents, software installers, music, videos, and so on. Once you click on one of these infected transmitters, the contamination may occur without any noticeable symptoms. In some cases, the Trojan may remain latent within the system until the hackers behind it decide to activate the malicious operations for which it has been programmed. However, in some cases, indications of the possible infection may be related to sudden crashes of the system, or freezing of the software installed on it, mouse cursor movements on the screen without any user interaction, or high usage of the CPU. Most of the time, however, the Trojan stays hidden, and there is very little possibility of spotting it before the compromised computer faces some significant harm.
What can a Trojan do?
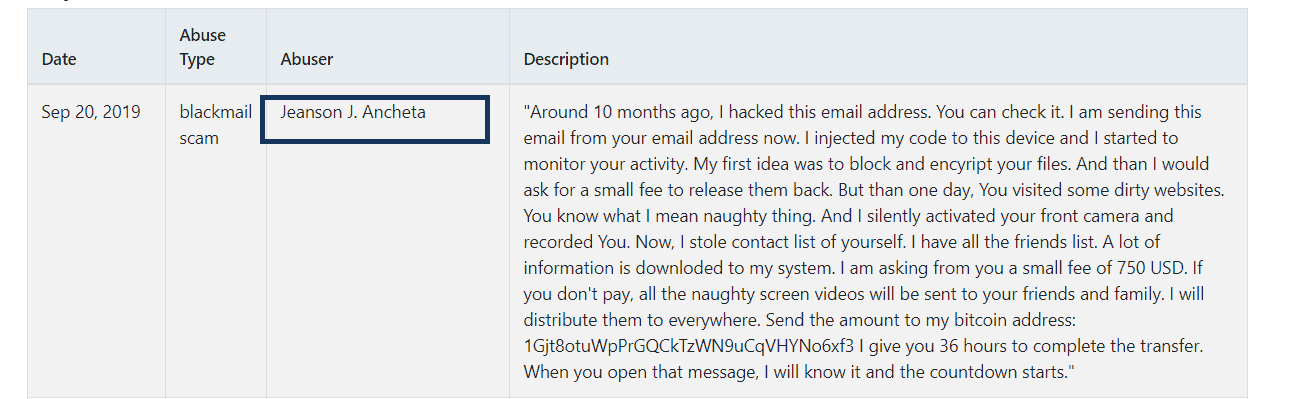
Threats such as Jeanson Ancheta are developed by cyber criminals with the purpose of damaging your system, and your virtual privacy with all kinds of illegal actions. The list of malicious tasks that a Trojan can execute can be very long, because it is possible to program such threats to do almost anything. Some of the most frequent Trojan-related criminal activities are system destruction, theft of personal information, file corruption, espionage, virus distribution, etc.
For instance, the hackers can use a threat like Jeanson Ancheta to monitor the keystrokes you make. This technique, known as keylogging, enables the hackers to collect data about your passwords, credit and debit card credentials, online banking accounts, and other sensitive details, which can later be used for money theft, banking fraud, or blackmailing. Another very frightening risk associated with the Trojans is the possibility of getting infected with Ransomware on top of the Trojan infection. This malware is a feared blackmailing tool, which the hackers use to lock all the information on your computer, and request a ransom to unlock it. Threats such as Jeanson Ancheta may play a key role in distributing Ransomware infections, as they assist it with finding its way inside the already compromised computers.
Due to all of what’s been mentioned above it is very important to remove the Trojan as quickly as possible, as this is the best way to protect your system against more harmful infections. The removal manual below will explain to you how to do this step-by-step, but for optimal results, and for a quick removal, it is advisable to scan the computer with reputable antivirus software. Keeping your system up-to-date can also prevent malicious threats from sneaking inside your system, so make sure you update it frequently to keep malware away.
Jeanson Ancheta SUMMARY:
| Name | Jeanson Ancheta |
| Type | Ransomware |
| Danger Level | High (Jeanson Ancheta Ransomware encrypts all types of files) |
| Symptoms | Typically there are no visible symptoms of the infection. |
| Distribution Method | Software from questionable download sites, malicious ads, spam, torrents, harmful email attachments, infected links. |
[add_third_banner]
Remove Jeanson Ancheta Email Virus Guide
1: Preparations
Note: Before you go any further, we advise you to bookmark this page or have it open on a separate device such as your smartphone or another PC. Some of the steps might require you to exit your browser on this PC.
2: Task Manager
Press Ctrl + Shift + Esc to enter the Task Manager. Go to the Tab labeled Processes (Details for Win 8/10). Carefully look through the list of processes that are currently active on you PC.
If any of them seems shady, consumes too much RAM/CPU or has some strange description or no description at all, right-click on it, select Open File Location and delete everything there.

Also, even if you do not delete the files, be sure to stop the process by right-clicking on it and selecting End Process.
3: IP related to Jeanson Ancheta
Go to c:\windows\system32\drivers\etc\hosts. Open the hosts file with notepad.
Find where it says Localhost and take a look below that.

If you see any IP addresses there (below Localhost) send them to us here, in the comments since they might be coming from the Jeanson Ancheta.
[add_forth_banner]
4: Disable Startup programs
Re-open the Start Menu and type msconfig.
Click on the first search result. In the next window, go to the Startup tab. If you are on Win 10, it will send you to the Startup part of the task manager instead, as in the picture:

If you see any sketchy/shady looking entries in the list with an unknown manufacturer or a manufacturer name that looks suspicious as there could be a link between them and Jeanson Ancheta , disable those programs and select OK.
5: Registry Editor
Press Windows key + R and in the resulting window type regedit.
Now, press Ctrl + F and type the name of the virus.
Delete everything that gets found. If you are not sure about whether to delete something, do not hesitate to ask us in the comments. Keep in mind that if you delete the wrong thing, you might cause all sorts of issues to your PC.
6: Deleting potentially malicious data – Jeanson Ancheta
Type each of the following locations in the Windows search box and hit enter to open the locations:
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
%Temp%
Delete everything you see in Temp linked to Jeanson Ancheta Ransomware. About the other folders, sort their contents by date and delete only the most recent entries. As always, if you are not sure about something, write to us in the comment section.
Leave a Reply