The Imagine Prime Virus in Depth
Annoying browser components like Imagine Prime Virus are generally referred to as Browser Hijackers due to their ability to mess with the browser’s settings and to initiate automatic page-redirects. If you are reading this post because your Safari, Chrome, Firefox or another favorite browser of yours has recently been taken over by ads, pop-ups, banners and sponsored messages “Generated by Imagine Prime”, and if you current homepage or search engine have the Imagine Prime name on them, then, on this page, you will find out exactly how to remove this irritation. The negative effects of the Browser Hijackers are mostly limited to browser interruptions and disruptions because these software components are not pieces of malware that can target your data like Ransomware or scam you like Trojans. Yet, sometimes, they can take you to pages that can be sketchy, and are generally very annoying. In older computers, hijackerslike Imagine Prime can seriously affect their performance and cause sluggishness and unresponsiveness because they can use a significant amount of the CPU and RAM resources for their ad-generating and page-redirecting activities. Thus, in most of the cases, those browser elements are seen as potentially unwanted and the users who have them are advised to uninstall them.
Bundled with other free and attractive programs, most Browser Hijackers are installed in the system by accident when the users don’t pay close attention to the setup settings of a given installer. Once inside, they change the homepage and/or the search engine and bombard you with pop-up windows of dubious ads, aggressive banners, and click-prompt requests. In some more extreme cases, some hijackers may even modify the searches you do in Google in order to redirect you to certain sponsored sites. Oftentimes, it may seem that the browser is out of your control and operates on its own: it enters different third-party pages on its own and does not follow the users’ commands when they try to open a certain site. That’s why it is not a surprise that a lot of web users may initially take hijackers like Imagine Prime for viruses.
Fortunately, the goal of those invasive page-redirecting components is not to attack the user’s computer, but rather to force the people to click on some sponsored third-party advertising content through pop-up windows and automatic page-redirects that appear without control all over the screen. Yet, despite not sharing the malicious traits of real security hazards such as Ransomware or Trojan Horses, annoyances like Imagine Prime should better be removed from the system with the help of a professional removal tool or manually.
There are many well-functioning security programs capable of uninstalling browser hijackers, but in the guide below, we have linked a trusted tool that deals with them in just a few seconds. You can safely use this tool to eliminate Imagine Prime along with other potentially unwanted apps or malware, like Mac Cleaner.pkg, that you might have gotten on the computer without even knowing it.
One way to avoid browser hijackers in the future is to keep away from any software that may be suspicious or untrustworthy. Also, when installing new software, always use the most detailed installation options (usually these are called Advanced or Custom), and carefully read every small text or pre-selected checkbox that allows the installation of additional apps, search engines and browser extensions that you may not want to get on your computer and browser.
SUMMARY:
| Name | Imagine Prime |
| Type | Browser Redirect or Adware for Mac |
| Danger Level | Medium (nowhere near threats like Ransomware, but still a security risk) |
| Symptoms | You may notice changes in your browser’s homepage or search engine and aggressive ad-generation all over your screen. |
| Distribution Method | Software bundling is a common method of distribution along with spam, torrents, ads and free downloads.. |
[add_third_banner]
Imagine Prime Virus Removal
Step 1: Closing Safari (or any other browser that you may be using at the moment)
First, you will need to close your browser if it is still open. If you can’t do that normally, you will need to Force Quit it:
Open the Apple Menu and select Force Quit to do that. You can also use the ⌘ key + Option Key combination to open the Force Quit Applications dialog box. In this box, select the Safari browser (or whatever browser you are using) and then click on the Quit button. Confirm the action by selecting Force Quit again.
Step 2: Killing suspicious processes
Open Finder and go to Applications > Utilities and then open Activity Monitor. Now take a careful look at the processes there – look for any that seem suspicious, unknown and questionable. If you think that a given process may be the culprit behind the issue or may at least be related to it, highlight it with the mouse and select the i option at its top.
In the box that opens, click on Sample.
Scan the sample files with the online scanner we have on this page and if any of them get flagged as malicious, delete them and then kill their processes.
Step 3: Safely launching the browser
Hold the Shift from your keyboard and then launch Safari – holding Shift will prevent any previously opened pages to load again, just in case any of them were related to the problem.
If any problematic pages still load after you safe-launch the browser, then do the following:
Force-Quit the browser (Safari) again and then turn off your Wi-Fi connection by clicking on the Wi-Fi off option from the Mac Menu. If you are using cable Internet, simply disconnect the cable from your Mac.
Step 4: Uninstalling suspicious extensions
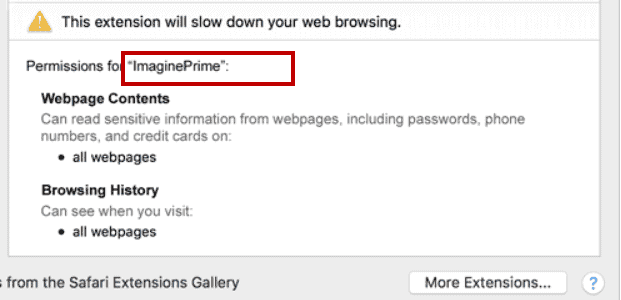
After you safe-launch Safari and are sure none of the previously opened pages load now, go to Preferences > Extensions.
Select and uninstall (by clicking on the Uninstall button) all extensions there that are unfamiliar to you or that you think may be suspicious. If you are not sure about a certain extension, it’s better to uninstall it – no extension is required for the normal functioning of the browser.
Step 5: Cleaning Safari
If you have other browsers aside from Safari, do the following:
In Safari, open Preferences from the browser’s menu and go to Privacy.
Select Remove All Website Data and then Remove Now. Note that this will delete all stored site data including any saved passwords and usernames. In other words, you will have to manually log-in to every site where you have a registration so make sure you remember your usernames and passwords.
Back in Preferences, click on General and see what your Safari’s homepage is. If it has been changed without your permission, change it back to what it used to be or to whatever you like it to be now.
Now go to the History menu and select the Clear History option.
Do the same to all other browsers you may have in your computer – here are examples with Chrome and Firefox.
[add_forth_banner]
Cleaning Chrome
Open Chrome and open its main menu, then go to More Tools > Extensions. Click on the Remove button next to all of the extensions that you do not trust.

Next, from the main menu, go to Settings and type Manage Search Engines in the search bar. Open the result that shows up and then delete all search engines other than the one you normally use by clicking on the three-dot icon next to the other ones and selecting Remove from list.

Back in Settings, type Reset and clean up and open the option that shows up (Restore settings to their original defaults). Confirm by selecting Reset Settings.

Cleaning Firefox
Open Firefox and then open its main menu. Go to Add-ons and open the Extensions menu from the left. Look at the extensions and Remove the ones you do not trust.

Next, open the menu again, go to Help > Troubleshooting information and in the page that opens, select Refresh Firefox and then confirm the action in the window that opens.

Leave a Reply