.Codnat File Virus in Depth
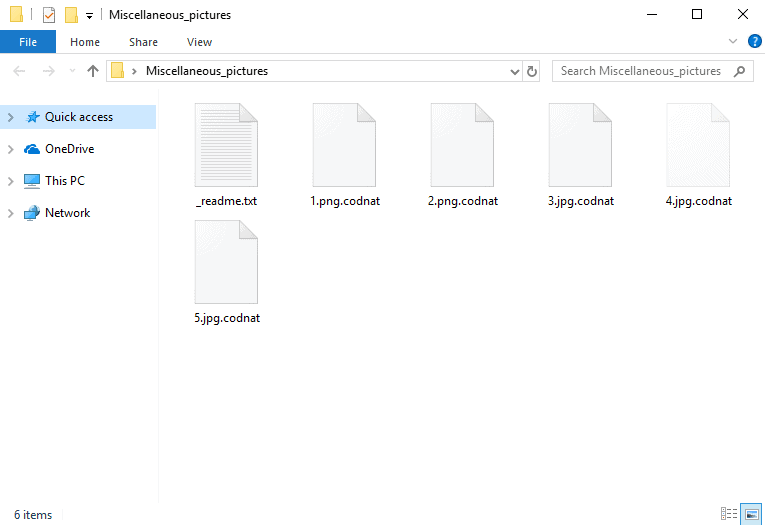

Down the page, you’re going to be presented with all the information you might want to know so as to potentially deal with Ransomware cryptoviruses like .Codnat, .Fordan, .Forasom, .Berost, .Fedasot – those are considered to be some of the biggest cyber threats these days. Lately, a new Ransomware virus program known as .Codnat has been developed and a lot of this article’s visitors probably have actually come to this page in search for help against it. The majority of Ransomware cryptoviruses function in a similar fashion. After the virus infects the computer system, it starts searching for some predetermined computer file types. Various kinds of data types can be focused on by a cryptovirus program – photos, text documents , video files or even, in certain instances, operating system data. As soon as the scanning phase is finished, the virus copies each preset document.
What is special regarding the copies is the fact they’re sealed due to the employment of an advanced file encryption code. Right after the virus completes the copying procedure of the infection, it would then carry on to remove the initial personal data which leaves the user with the locked-up copies which can’t be opened without having a special decryption key. What follows is the generation of a ransom-requesting message on your monitor saying that you need to pay a certain amount of money as a ransom in return for the restoration of your sealed files. In this article, we may possibly be able to help those of our readers that have already gone through all the things that we have mentioned so far – down below, there is a removal guide that can help users handle a Ransomware infection for all those of you that might need help for battling this form of cryptovirus.
How .Codnat File Virus Works
The first thing we think you should know is that the computer viruses from the Ransomware category don’t act like any type of malicious programs. Dealing with this malware sort is made even harder by the fact that very few antivirus programs in reality stand a chance at discovering such a risk on time. This comes from the fact that usually no representative of Ransomware can or will immediately damage your device in any way. For this reason, there is nothing to trigger the response of your antivirus tool. To be completely precise, the process of file encryption is not hazardous in itself – it could just block the access to the targeted data files, yet it can’t lead to any harm to the files. Basically, this kind of malicious software can make an otherwise beneficial file protection process harmful to the affected person. Searching for for infection signs, for example unusually increased usage of system resources like RAM, HDD or CPU, could help you to manually diagnose a Ransomware infection, but keep in mind that in many cases the encryption process develops way too fast and there’s little time to detect the malware or take proper measures.
.Codnat SUMMARY:
| Name | .Codnat |
| Type | Ransomware |
| Danger Level | High (.Codnat Ransomware encrypts all types of files) |
| Symptoms | .Codnat Ransomware is hard to detect and aside from increased use of RAM and CPU, there would barely be any other visible red flags. |
| Distribution Method | Most of the time, Trojans get distributed through spam e-mails and social network messages, malicious ads, shady and pirated downloads, questionable torrents and other similar methods. |
[add_third_banner]
Remove .Codnat File Virus Ransomware
1: Preparations
Note: Before you go any further, we advise you to bookmark this page or have it open on a separate device such as your smartphone or another PC. Some of the steps might require you to exit your browser on this PC.
2: Task Manager
Press Ctrl + Shift + Esc to enter the Task Manager. Go to the Tab labeled Processes (Details for Win 8/10). Carefully look through the list of processes that are currently active on you PC.
If any of them seems shady, consumes too much RAM/CPU or has some strange description or no description at all, right-click on it, select Open File Location and delete everything there.

Also, even if you do not delete the files, be sure to stop the process by right-clicking on it and selecting End Process.
3: IP related to .Codnat
Go to c:\windows\system32\drivers\etc\hosts. Open the hosts file with notepad.
Find where it says Localhost and take a look below that.

If you see any IP addresses there (below Localhost) send them to us here, in the comments since they might be coming from the .Codnat.
[add_forth_banner]
4: Disable Startup programs
Re-open the Start Menu and type msconfig.
Click on the first search result. In the next window, go to the Startup tab. If you are on Win 10, it will send you to the Startup part of the task manager instead, as in the picture:

If you see any sketchy/shady looking entries in the list with an unknown manufacturer or a manufacturer name that looks suspicious as there could be a link between them and .Codnat , disable those programs and select OK.
5: Registry Editor
Press Windows key + R and in the resulting window type regedit.
Now, press Ctrl + F and type the name of the virus.
Delete everything that gets found. If you are not sure about whether to delete something, do not hesitate to ask us in the comments. Keep in mind that if you delete the wrong thing, you might cause all sorts of issues to your PC.
6: Deleting potentially malicious data – .Codnat
Type each of the following locations in the Windows search box and hit enter to open the locations:
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
%Temp%
Delete everything you see in Temp linked to .Codnat Ransomware. About the other folders, sort their contents by date and delete only the most recent entries. As always, if you are not sure about something, write to us in the comment section.
7: .Codnat Decryption
The previous steps were all aimed at removing the .Codnat Ransomware from your PC. However, in order to regain access to your files, you will also need to decrypt them or restore them. For that, we have a separate article with detailed instructions on what you have to do in order to unlock your data. Here is a link to that guide.
Leave a Reply