About the .Nemty Virus
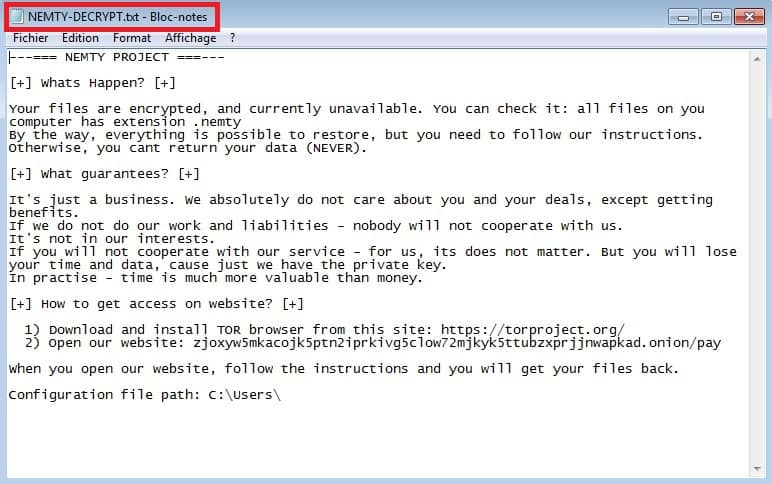
Every web user knows that the Internet is filled with all forms of dangerous software hazards. In this post, we will focus on one really dangerous and difficult to handle type of computer viruses which researchers tend to call Ransomware. This type of viruses is especially dangerous and challenging to handle since they differ greatly from all other forms of malware. You most probably have come to this page because you’ve been searching for information about Nemty – a recently launched Ransomware that belongs to the cryptovirus subcategory. What Nemty does is it locks the user’s files with a very complex and highly-advanced file encryption code. If the victims want to unlock them and regain their access, they would need to pay a fixed amount of money as a ransom in exchange for a special decryption key. All the details about the ransom transaction would usually be described in a ransom pop-up note that, in most cases, would get displayed on the infected Computer’s screen immediately after the file-encryption process completes. Giving your money to the hackers behind an infection like Nemty is neither the best nor the most advisable course of action. That’s why, down below, you can find an instruction manual which is focused on helping our visitors deal with the Ransomware virus in an alternative way which does not involve paying ransom to anyone. Feel free to use it in case the nasty Nemty cryptovirus has already infected your system and let us know the outcome in the comments section after the article.
What to do with .Nemty files?

Those of you, who want to effectively counteract Ransomware threats (Masodas, Versato) need to be familiar with their main traits and specifics in order to increase their chance for successful removal and recovery. Keep in mind, though, that this sort of malicious software is unique in the way it functions and this is the main reason why nobody can give any guarantees about the recovery from its attack. The thing that you can expect from illegal software like Nemty is that it would initiate a system scan on all your hard drives. The malware is generally looking for a number of specific file types which later would be encrypted rather than harming your Computer in a specific way or corrupting its software. This itself is very different than what some other types of malware would normally do. The data types that the Ransomware will likely look for are photos, documents and also videos/sounds, personal files, etc. Once the scan is completed, each one of the targeted files gets copied by the Ransomware. When the file copy is created, the initial file would get deleted by the malware. The special thing about the copies made by the illegal software is that they are all secured by an advanced encryption code. With the help of this encryption code, the criminal that is controlling the malware is able to block their victim access to the targeted private files and later require a ransom transaction in order to send the user the decryption key needed for the sealed data.
The most serious problem that comes from the use of the data encryption is the fact this process is not seen as dangerous by a number of commonly used system security applications. This allows threats like Nemty to encrypt files without being detected and helps the criminals to blackmail the web users once they are denied access to their information.
SUMMARY:
| Name | Nemty |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Very few and unnoticeable ones before the ransom notification comes up. |
| Distribution Method | From fake ads and fake system requests to spam emails and contagious web pages. |
[add_third_banner]
Nemty Virus Removal
1: Preparations
Note: Before you go any further, we advise you to bookmark this page or have it open on a separate device such as your smartphone or another PC. Some of the steps might require you to exit your browser on this PC.
2: Task Manager
Press Ctrl + Shift + Esc to enter the Task Manager. Go to the Tab labeled Processes (Details for Win 8/10). Carefully look through the list of processes that are currently active on you PC.
If any of them seems shady, consumes too much RAM/CPU or has some strange description or no description at all, right-click on it, select Open File Location and delete everything there.

Also, even if you do not delete the files, be sure to stop the process by right-clicking on it and selecting End Process.
3: IP related to Nemty
Go to c:\windows\system32\drivers\etc\hosts. Open the hosts file with notepad.
Find where it says Localhost and take a look below that.

If you see any IP addresses there (below Localhost) send them to us here, in the comments since they might be coming from the Nemty.
[add_forth_banner]
4: Disable Startup programs
Re-open the Start Menu and type msconfig.
Click on the first search result. In the next window, go to the Startup tab. If you are on Win 10, it will send you to the Startup part of the task manager instead, as in the picture:

If you see any sketchy/shady looking entries in the list with an unknown manufacturer or a manufacturer name that looks suspicious as there could be a link between them and Nemty , disable those programs and select OK.
5: Registry Editor
Press Windows key + R and in the resulting window type regedit.
Now, press Ctrl + F and type the name of the virus.
Delete everything that gets found. If you are not sure about whether to delete something, do not hesitate to ask us in the comments. Keep in mind that if you delete the wrong thing, you might cause all sorts of issues to your PC.
6: Deleting potentially malicious data – Nemty
Type each of the following locations in the Windows search box and hit enter to open the locations:
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
%Temp%
Delete everything you see in Temp linked to Nemty Ransomware. About the other folders, sort their contents by date and delete only the most recent entries. As always, if you are not sure about something, write to us in the comment section.
7: Nemty Decryption
The previous steps were all aimed at removing the Nemty Ransomware from your PC. However, in order to regain access to your files, you will also need to decrypt them or restore them. For that, we have a separate article with detailed instructions on what you have to do in order to unlock your data. Here is a link to that guide.
Leave a Reply