In the event that your computer has been secretly compromised by a Ransomware cryptovirus called Nacro, you may be at risk of losing some of your most important files. Ransomware infections like this one specialize in the secret encryption of many types of digital information, which people store on their machines. The files that Nacro targets may include images, documents, audio and video files, system files, and more, and the reason why such viruses are called Ransomware is because they demand a ransom payment in exchange for undoing the applied encryption. This ransom amount can range from anything several hundred to several thousands of dollars, depending on the virus, and the victims that have been targeted.
In case you have been infected, we think it’s important that you learn more about this virus before we provide you with the instructions on how to remove it. Therefore, we recommend that you read the information that follows, and after that make use of our detailed removal guide below.
How does the .Nacro virus work?
Ransomware cryptoviruses, such as Nacro, are some of the most terrible computer threats because they actually block the access to your personal files by means of file-encryption and then blackmail you to pay a ransom for their decryption. This is a sophisticated blackmailing scheme that is not only incredibly difficult to deal with, but also very tricky to prevent. The reason is, the Ransomware that does all that bad stuff to your data is typically very difficult to detect and manages to remain under the radar of most antivirus programs. That is because the file-encryption itself is not something harmful that corrupts the system or destroys your information. This is a data-protection method which is commonly used in many sectors where digital information should be kept safe from unauthorized access. Therefore, due to a lack of any actual damage, most security software does not identify the file-encrypting process as a threat.
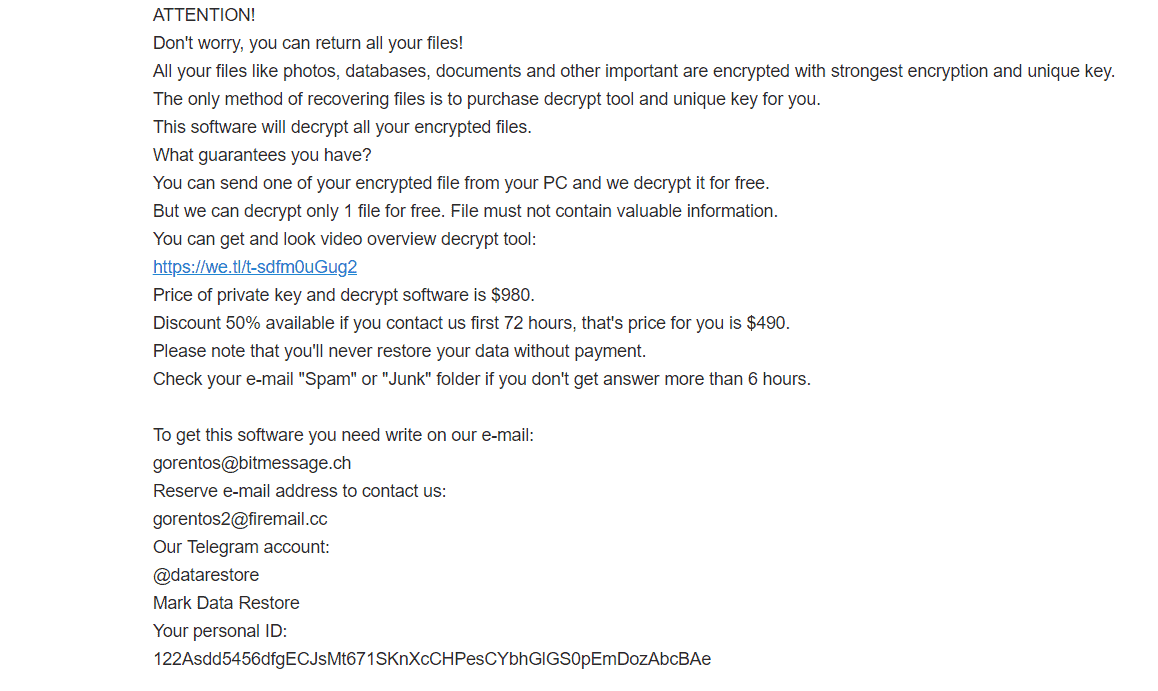
People behind threats like Nacro, Coharos or Nasoh however, use that otherwise useful data-protection method as the basis for a money extortion scheme. They keep the decryption key, needed for accessing your files on their servers and ask you to pay a certain amount of money for it in order to obtain it.
Saving the encrypted .Nacro files

The hackers threaten that if you don’t pay the ransom, they will destroy the decryption key, and leave your important files inaccessible forever. Security experts, however, warn that giving your money to the hackers only encourages them to blackmail you even more. Besides, there is no guarantee that after you fulfill all of their demands they will really send you the decryption key, let alone that it will work.
Therefore, our suggestion is to focus on removing the insidious Nacro from your computer and then try some other ways of restoring your sealed files. The removal guide below will help you with that. There is also a section with some file-recovery suggestions, which don’t involve paying ransom to anyone. Feel free to give them a try, and let us know if you have any questions by leaving us a comment below the article.
Nacro SUMMARY:
| Name | Nacro |
| Type | Ransomware |
| Danger Level | High (Nacro Ransomware encrypts all types of files) |
| Symptoms | Nacro Ransomware is hard to detect and aside from increased use of RAM and CPU, there would barely be any other visible red flags. |
| Distribution Method | Most of the time, Trojans get distributed through spam e-mails and social network messages, malicious ads, shady and pirated downloads, questionable torrents and other similar methods. |
[add_third_banner]
Nacro Virus Removal
1: Preparations
Note: Before you go any further, we advise you to bookmark this page or have it open on a separate device such as your smartphone or another PC. Some of the steps might require you to exit your browser on this PC.
2: Task Manager
Press Ctrl + Shift + Esc to enter the Task Manager. Go to the Tab labeled Processes (Details for Win 8/10). Carefully look through the list of processes that are currently active on you PC.
If any of them seems shady, consumes too much RAM/CPU or has some strange description or no description at all, right-click on it, select Open File Location and delete everything there.

Also, even if you do not delete the files, be sure to stop the process by right-clicking on it and selecting End Process.
3: IP related to Nacro
Go to c:\windows\system32\drivers\etc\hosts. Open the hosts file with notepad.
Find where it says Localhost and take a look below that.

If you see any IP addresses there (below Localhost) send them to us here, in the comments since they might be coming from the Nacro.
[add_forth_banner]
4: Disable Startup programs
Re-open the Start Menu and type msconfig.
Click on the first search result. In the next window, go to the Startup tab. If you are on Win 10, it will send you to the Startup part of the task manager instead, as in the picture:

If you see any sketchy/shady looking entries in the list with an unknown manufacturer or a manufacturer name that looks suspicious as there could be a link between them and Nacro , disable those programs and select OK.
5: Registry Editor
Press Windows key + R and in the resulting window type regedit.
Now, press Ctrl + F and type the name of the virus.
Delete everything that gets found. If you are not sure about whether to delete something, do not hesitate to ask us in the comments. Keep in mind that if you delete the wrong thing, you might cause all sorts of issues to your PC.
6: Deleting potentially malicious data – Nacro
Type each of the following locations in the Windows search box and hit enter to open the locations:
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
%Temp%
Delete everything you see in Temp linked to Nacro Ransomware. About the other folders, sort their contents by date and delete only the most recent entries. As always, if you are not sure about something, write to us in the comment section.
7: Nacro Decryption
The previous steps were all aimed at removing the Nacro Ransomware from your PC. However, in order to regain access to your files, you will also need to decrypt them or restore them. For that, we have a separate article with detailed instructions on what you have to do in order to unlock your data. Here is a link to that guide.
Leave a Reply