About .Muslat Virus File
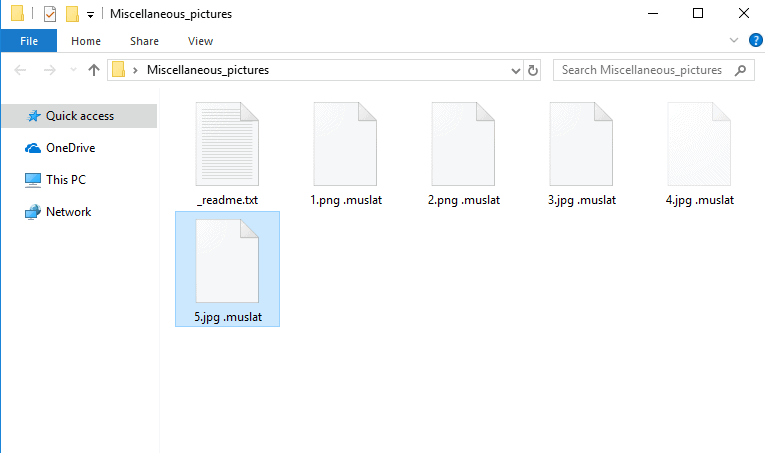
After the ransomware encrypt your files, it leaves a _readme.txt file with instructions to follow:
ATTENTION!
Don’t worry my friend, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
https ://we .tl/t-pPLXOv9XTI
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.
.Muslat is the name of a newly discovered Ransomware cryptovirus which is used for blackmailing purposes. This threat uses something called “encryption” to lock personal files and different types of data stored on the infected computer and to render it inaccessible without the application of a special decryption key. The victims of .Muslat are usually blackmailed to pay a certain amount of money to the hackers who control the infection in order to receive that decryption key and to regain access to their files. The target of Ransomware cryptoviruses like .Muslat, .Heroset ,.Pidon .Davda could be big companies and public institutions as well as individual users. In the companies, the attack of this type of malware can cause economic losses due to massive loss of sensitive and valuable business-related data. In such situations, the desperation to recover the normal activity of a company and access the sealed data can lead some companies to consider giving in to the blackmailing scheme and paying in order to obtain the key which is needed for accessing their information.
In most situations, however, security experts recommend keeping a cool head and never pay the ransom, as there is no assurance that the access to the encrypted files will really be restored. In addition, the ransom payment can be an incentive for the cybercriminals to focus on attacking again and again those companies that seem to be more susceptible to giving in to such blackmailing and harassment tactics. The consequence is that the situation may get repeated, there may be new attacks and the amount of money requested for recovering the data again may go up.
What do I do if you are infected with .Muslat Virus File?
If you are already infected with .Muslat, you should know that there really isn’t a universal method that can help you deal with a Ransomware like this one. How effectively you will be able to remove the infection and regain access to your files depends on whether prior to the attack you have implemented some security measures, for instance, creating backups for your files on an external storage, updating your OS and antivirus, etc. However, even if you have not taken some specific protection measures, we suggest you explore some alternative methods of dealing with this malware and try not to sponsor the hackers’ criminal scheme with your money. For instance, in the removal guide below, there are instructions which may help you to detect and safely remove .Muslat from your PC, as well as some file-recovery steps that do not involve paying ransom to anyone.
In any case, if you detect that you are infected, it is important that you immediately disconnect the computer from the network (cable or WiFi) and other devices to prevent the malware from spreading to other computers in the network. Then you may need to scan your PC with a reliable malware removal tool (such as the one on this page), in order to quickly detect the infection and remove it. After you have successfully cleaned the computer, you may want to explore some file-recovery solutions like those on the file-recovery section in the guide below. If you have backup copies of your files that you store on an external drive or on a cloud, you can fully avoid the ransom payment and still recover your data by simply restoring the needed data on the Ransomware-free computer from the backup.
.Muslat SUMMARY:
| Name | .Muslat |
| Type | Ransomware |
| Danger Level | High (.Muslat Ransomware encrypts all types of files) |
| Symptoms | .Muslat Ransomware is hard to detect and aside from increased use of RAM and CPU, there would barely be any other visible red flags. |
| Distribution Method | Most of the time, Trojans get distributed through spam e-mails and social network messages, malicious ads, shady and pirated downloads, questionable torrents and other similar methods. |
[add_third_banner]
Remove .Muslat File Virus Ransomware
1: Preparations
Note: Before you go any further, we advise you to bookmark this page or have it open on a separate device such as your smartphone or another PC. Some of the steps might require you to exit your browser on this PC.
2: Task Manager
Press Ctrl + Shift + Esc to enter the Task Manager. Go to the Tab labeled Processes (Details for Win 8/10). Carefully look through the list of processes that are currently active on you PC.
If any of them seems shady, consumes too much RAM/CPU or has some strange description or no description at all, right-click on it, select Open File Location and delete everything there.

Also, even if you do not delete the files, be sure to stop the process by right-clicking on it and selecting End Process.
3: IP related to .Muslat
Go to c:\windows\system32\drivers\etc\hosts. Open the hosts file with notepad.
Find where it says Localhost and take a look below that.

If you see any IP addresses there (below Localhost) send them to us here, in the comments since they might be coming from the .Muslat.
[add_forth_banner]
4: Disable Startup programs
Re-open the Start Menu and type msconfig.
Click on the first search result. In the next window, go to the Startup tab. If you are on Win 10, it will send you to the Startup part of the task manager instead, as in the picture:

If you see any sketchy/shady looking entries in the list with an unknown manufacturer or a manufacturer name that looks suspicious as there could be a link between them and .Muslat , disable those programs and select OK.
5: Registry Editor
Press Windows key + R and in the resulting window type regedit.
Now, press Ctrl + F and type the name of the virus.
Delete everything that gets found. If you are not sure about whether to delete something, do not hesitate to ask us in the comments. Keep in mind that if you delete the wrong thing, you might cause all sorts of issues to your PC.
6: Deleting potentially malicious data – .Muslat
Type each of the following locations in the Windows search box and hit enter to open the locations:
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
%Temp%
Delete everything you see in Temp linked to .Muslat Ransomware. About the other folders, sort their contents by date and delete only the most recent entries. As always, if you are not sure about something, write to us in the comment section.
7: .Muslat Decryption
The previous steps were all aimed at removing the .Muslat Ransomware from your PC. However, in order to regain access to your files, you will also need to decrypt them or restore them. For that, we have a separate article with detailed instructions on what you have to do in order to unlock your data. Here is a link to that guide.
Leave a Reply