Trojan Horses like I know Email Scam are infamous for their many abilities and ways of causing harm to the targeted computer and its user. Hopefully, after you read the next paragraphs, and check out the guide below them, you would have a better understanding of the specifics of these threats, and would know how to take care of I know in case it has entered your system and is currently carrying out its nefarious activities.
The email from I Know Scam is annoying.
This is probably one of the most varied categories of malware, but even so, there are certain things that most Trojan Horse threats have in common.
One such thing is the stealth they are infamous for. It is no coincidence that this particular type of malware threats has been named after the mythological wooden horse from the Greek myth about the Trojan war. The name is a metaphor for stealth – something harmful disguised as something that doesn’t raise suspicion. This perfectly describes the Trojan Horse malware programs – on the outside, most of them look like harmless, and even helpful pieces of data. Case in point, a many Trojans are get disguised by their creators as software installers. This is especially common among installation files downloaded from sites that distribute pirated content. Such sites don’t typically have good control over the stuff that gets uploaded there, which allows the hackers to sneak in compromised files, that are disguised as harmless program installers. If you download something from a pirate site, don’t be surprised if it turns out to be a malicious Trojan Horse in disguise. Therefore, this is one more reason not to visit and download stuff from such websites, with the other reason being the fact that doing so would be illegal, and punishable by the government.
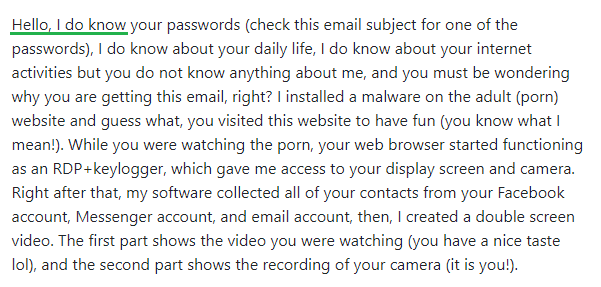
The I Know Email Scam
Another important characteristic of the Trojan Horse family is the versatility of these infections. Due to this, and also, due to the fact I know is a rather new malicious program, we can’t really tell you the exact end-goal of this malware. It could be to spy on you, to use your computer as a cryptocurrency-mining bot, to infect your machine with Ransomware, to steal money from your banking account from under your nose, and more. In any case, you should definitely not wait to find out what the malware is trying to achieve. As soon as you notice that the Trojan is in your system, you should take the necessary precautions and actions to rid your computer of its presence. One way to do that is to use the guide offered on this page. Its instructions, as well as the professional anti-malware solution linked inside of it, should be enough to allow you to liberate your system from the nefarious threat. In case you run into any difficulties while trying to remove the malware, the comments section below is open to your requests and queries.
SUMMARY:
| Name | I know |
| Type | Trojan |
| Danger Level | High (Trojans are often used as a backdoor for Ransomware) |
| Symptoms | The symptoms of a Trojan may include heavy use of RAM and CPU, sudden BSOD crashes, software errors, and more. |
| Distribution Method | Distribution methods commonly used for spreading these threats are pirated programs, misleading spam letters, clickbaits ads, and more. |
[add_third_banner]
Remove The I Know Email Scam
1: Preparations
Note: Before you go any further, we advise you to bookmark this page or have it open on a separate device such as your smartphone or another PC. Some of the steps might require you to exit your browser on this PC.
2: Task Manager
Press Ctrl + Shift + Esc to enter the Task Manager. Go to the Tab labeled Processes (Details for Win 8/10). Carefully look through the list of processes that are currently active on you PC.
If any of them seems shady, consumes too much RAM/CPU or has some strange description or no description at all, right-click on it, select Open File Location and delete everything there.

Also, even if you do not delete the files, be sure to stop the process by right-clicking on it and selecting End Process.
3: IP related to I know
Go to c:\windows\system32\drivers\etc\hosts. Open the hosts file with notepad.
Find where it says Localhost and take a look below that.

If you see any IP addresses there (below Localhost) send them to us here, in the comments since they might be coming from the I know .
[add_forth_banner]
4: Disable Startup programs
Re-open the Start Menu and type msconfig.
Click on the first search result. In the next window, go to the Startup tab. If you are on Win 10, it will send you to the Startup part of the task manager instead, as in the picture:

If you see any sketchy/shady looking entries in the list with an unknown manufacturer or a manufacturer name that looks suspicious as there could be a link between them and I know , disable those programs and select OK.
5: Registry Editor
Press Windows key + R and in the resulting window type regedit.
Now, press Ctrl + F and type the name of the virus.
Delete everything that gets found. If you are not sure about whether to delete something, do not hesitate to ask us in the comments. Keep in mind that if you delete the wrong thing, you might cause all sorts of issues to your PC.
6: Deleting potentially malicious data – I know
Type each of the following locations in the Windows search box and hit enter to open the locations:
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
%Temp%
Delete everything you see in Temp linked to I know Trojan. About the other folders, sort their contents by date and delete only the most recent entries. As always, if you are not sure about something, write to us in the comment section.
7: I know Decryption
The previous steps were all aimed at removing the I know Trojan from your PC. However, in order to regain access to your files, you will also need to decrypt them or restore them. For that, we have a separate article with detailed instructions on what you have to do in order to unlock your data. Here is a link to that guide.
Leave a Reply