About the [email protected] Virus
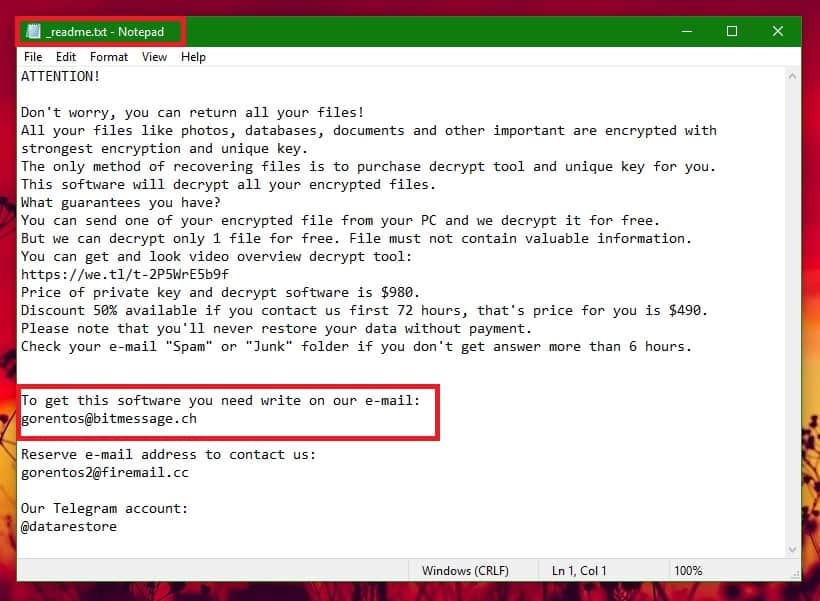
The technique of using valuable user data as a hostage has existed for decades but has gained more popularity in recent years thanks to a special type of malware known as Ransomware. If you are on this page, you most probably have already had a close encounter with one of the latest Ransomware representatives which the security researchers call [email protected]. This infection uses a special encryption algorithm to secretly lock different types of personal files, such as documents, images, audios, videos, archives, etc. and to make them inaccessible unless the corresponding decryption key is applied. The malware typically operates in the background of the system and rarely shows visible symptoms, which is the main reason its attack remains undetected up until the very last moment when a scary ransom-demanding message gets generated on the victim’s screen.
But how the [email protected] Virus exactly works?

Ransomware doesn’t damage or corrupt the files or the system it has invaded – the encrypted data stays intact and the only difference is that none of the files can be opened until the ransom payment is made. For the scheme to work, the users’ computers must be infected with the Ransomware virus without the knowledge of the users, which usually happens when they get tricked into clicking on a link, a file or some component that is a carrier of the infection. Imagine, for example, that you are sitting on your computer and you receive an email that claims to be from a well-known organization, some courier, an institution, an invoicing company, etc. Everything looks legitimate and you are prompted to click on some link or some confirmation immediately, without much thinking. This way the crooks are creating a sense of urgency, and effectively managing to compromise your machine after you click on the link.
Ransomware can also sneak inside your system if you click on an attached document, a fake ad, if you go to an infected website, or download a compromised software installer.
In recent years, spam emails have been used to distribute viruses contained in documents such as false delivery notices, energy bills or tax returns. Once the users click on the link, or the attachment, the malware encrypts the files present in the computer’s hard drive, blocking the people’s documents and asking for a ransom payment in exchange for their liberation.
Infections like [email protected], Gero, Masodas are very profitable for their creators because a large amount of important and sensitive information is usually stored in computers, and most people do not have extensive backups of their files. This is what makes modern attacks with Ransomware viruses so painful. Most people would panic if their computers get blocked or if they are denied access to their files. If some company’s network gets attacked by such a virus, it may lose productivity and, in the case of hospitals, having patients’ medical records blocked can put their lives at risk. This, of course, makes the attacks from Ransomware even more effective. Some hackers even have Ransomware “help desks”, returning to the victims some files to reassure them that they are not being completely cheated. But releasing the rest of your files and information may cost you a fortune and is not guaranteed at all. In many cases, the crooks simply disappear when they get the ransom payment and never release the encrypted files. Therefore, security experts, including our “How to remove” team, advice against giving money to the hackers. Opting for some potential alternatives focused on removing the malware is preferable as it will allow you to make your computer safe again and may still allow you to bring back some of the data.
SUMMARY:
| Name | [email protected] |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Very few and unnoticeable ones before the ransom notification comes up. |
| Distribution Method | From fake ads and fake system requests to spam emails and contagious web pages. |
[add_third_banner]
Remove [email protected] Ransomware
1: Preparations
Note: Before you go any further, we advise you to bookmark this page or have it open on a separate device such as your smartphone or another PC. Some of the steps might require you to exit your browser on this PC.
2: Task Manager
Press Ctrl + Shift + Esc to enter the Task Manager. Go to the Tab labeled Processes (Details for Win 8/10). Carefully look through the list of processes that are currently active on you PC.
If any of them seems shady, consumes too much RAM/CPU or has some strange description or no description at all, right-click on it, select Open File Location and delete everything there.

Also, even if you do not delete the files, be sure to stop the process by right-clicking on it and selecting End Process.
3: IP related to [email protected]
Go to c:\windows\system32\drivers\etc\hosts. Open the hosts file with notepad.
Find where it says Localhost and take a look below that.

If you see any IP addresses there (below Localhost) send them to us here, in the comments since they might be coming from the [email protected].
[add_forth_banner]
4: Disable Startup programs
Re-open the Start Menu and type msconfig.
Click on the first search result. In the next window, go to the Startup tab. If you are on Win 10, it will send you to the Startup part of the task manager instead, as in the picture:

If you see any sketchy/shady looking entries in the list with an unknown manufacturer or a manufacturer name that looks suspicious as there could be a link between them and [email protected] , disable those programs and select OK.
5: Registry Editor
Press Windows key + R and in the resulting window type regedit.
Now, press Ctrl + F and type the name of the virus.
Delete everything that gets found. If you are not sure about whether to delete something, do not hesitate to ask us in the comments. Keep in mind that if you delete the wrong thing, you might cause all sorts of issues to your PC.
6: Deleting potentially malicious data – [email protected]
Type each of the following locations in the Windows search box and hit enter to open the locations:
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
%Temp%
Delete everything you see in Temp linked to [email protected] Ransomware. About the other folders, sort their contents by date and delete only the most recent entries. As always, if you are not sure about something, write to us in the comment section.
7: [email protected] Decryption
The previous steps were all aimed at removing the [email protected] Ransomware from your PC. However, in order to regain access to your files, you will also need to decrypt them or restore them. For that, we have a separate article with detailed instructions on what you have to do in order to unlock your data. Here is a link to that guide.
Leave a Reply