[email protected] is a type of Ransomware that encodes your files and then blackmails you into paying for the decryption key. To learn how to remove [email protected] and potentially restore some of the files, be sure to read the next lines.
These threats may often come in the form of emails with attached files that will download the Ransomware virus to your computer the moment you click on the attachment. In other cases, the infection may be delivered to you the moment you click on a malicious link, an ad, a fake pop-up request, or on some random message. This is usually all that it takes for the infection to compromise your system, and do its dirty work. That’s why it is important to be very careful when browsing online, especially if you come across redirect links, or sketchy webpages, or when receiving such emails from unknown senders.
The [email protected] virus in depth
The [email protected], .Adame and .Kvag viruses typically have no visible symptoms, and are very difficult to remove. Once your computer has been successfully compromised, the [email protected] virus will then start encrypting your files, one by one. This may take a while depending on how much data your computer has stored, and how powerful your processor is. You may even notice in some cases that your PC is running extremely slowly, which is a reason to suspect you may have been infected. The easiest way to check is to go to the task manager, and look at the CPU/RAM consumption of the different processes. If you notice a suspicious or unfamiliar process using a lot of resources, there’s a chance that it may be related to a Ransomware infection.
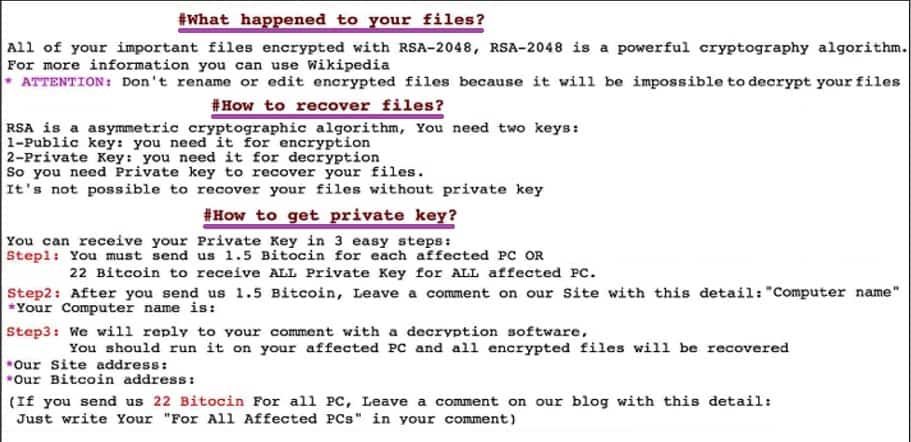
However, if you have not had the rare luck to discover the [email protected] Ransomware virus before it has completed its secret file encryption process, you will find out what has happened through a special ransom-demanding message. This message will probably say that your files have been encrypted and that, unless you pay a certain amount of money, you won’t be able to access them again.
The [email protected] file encryption
The [email protected] file encryption is what the hackers use to block the access to your most needed files. The applied [email protected] file encryption is typically reversible only after the application of a special decryption key. The hackers behind the Ransomware typically promise to send it to you the moment you pay, or they threaten to destroy it if you don’t send them the ransom money.
While this the promise of receiving the decryption key may sound tempting, remember that you are still dealing with criminals. If they have already hacked into your computer, there is no guarantee they’re going to send the promised key to you even if you strictly follow their demands. In fact, there is a always a significant chance that they may not send the key, and instead ask for another payment since you’ve agreed to pay once.
Obviously, you can choose whether to risk sending the hackers your money or not, but our suggestion is to first try the instructions in the guide below. They will help you to locate, and remove the Ransomware, and possibly avoid the ransom payment by recovering your files.
SUMMARY:
| Name | [email protected] |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Very few and unnoticeable ones before the ransom notification comes up. |
| Distribution Method | From fake ads and fake system requests to spam emails and contagious web pages. |
[add_third_banner]
[email protected] Virus Removal
1: Preparations
Note: Before you go any further, we advise you to bookmark this page or have it open on a separate device such as your smartphone or another PC. Some of the steps might require you to exit your browser on this PC.
2: Task Manager
Press Ctrl + Shift + Esc to enter the Task Manager. Go to the Tab labeled Processes (Details for Win 8/10). Carefully look through the list of processes that are currently active on you PC.
If any of them seems shady, consumes too much RAM/CPU or has some strange description or no description at all, right-click on it, select Open File Location and delete everything there.

Also, even if you do not delete the files, be sure to stop the process by right-clicking on it and selecting End Process.
3: IP related to [email protected]
Go to c:\windows\system32\drivers\etc\hosts. Open the hosts file with notepad.
Find where it says Localhost and take a look below that.

If you see any IP addresses there (below Localhost) send them to us here, in the comments since they might be coming from the [email protected].
[add_forth_banner]
4: Disable Startup programs
Re-open the Start Menu and type msconfig.
Click on the first search result. In the next window, go to the Startup tab. If you are on Win 10, it will send you to the Startup part of the task manager instead, as in the picture:

If you see any sketchy/shady looking entries in the list with an unknown manufacturer or a manufacturer name that looks suspicious as there could be a link between them and [email protected] , disable those programs and select OK.
5: Registry Editor
Press Windows key + R and in the resulting window type regedit.
Now, press Ctrl + F and type the name of the virus.
Delete everything that gets found. If you are not sure about whether to delete something, do not hesitate to ask us in the comments. Keep in mind that if you delete the wrong thing, you might cause all sorts of issues to your PC.
6: Deleting potentially malicious data – [email protected]
Type each of the following locations in the Windows search box and hit enter to open the locations:
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
%Temp%
Delete everything you see in Temp linked to [email protected] Ransomware. About the other folders, sort their contents by date and delete only the most recent entries. As always, if you are not sure about something, write to us in the comment section.
7: [email protected] Decryption
The previous steps were all aimed at removing the [email protected] Ransomware from your PC. However, in order to regain access to your files, you will also need to decrypt them or restore them. For that, we have a separate article with detailed instructions on what you have to do in order to unlock your data. Here is a link to that guide.
Leave a Reply