About .Acute
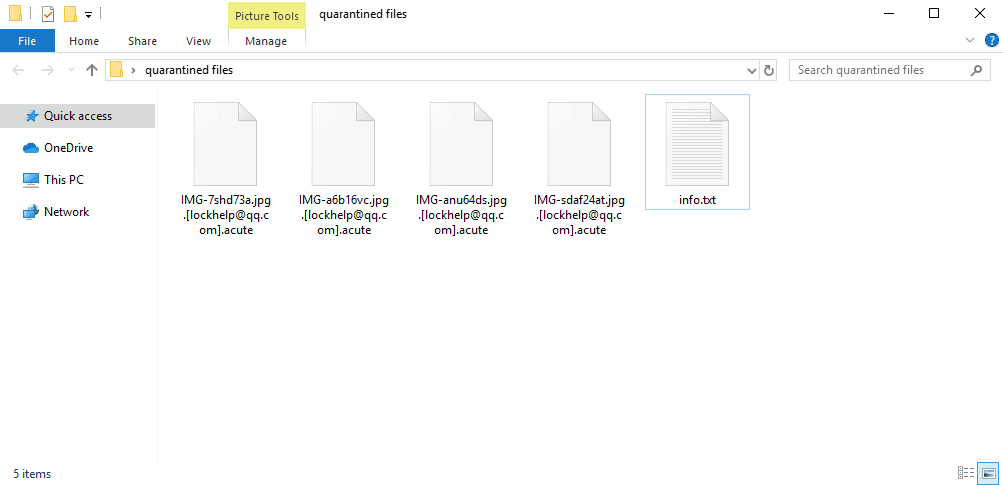
Once the encryption is complete you will find an info.txt file with the instructions meant to be followed by you:
!!! All of your files are encrypted !!!
To decrypt them send e-mail to this address: [email protected].
If there is no response from our mail, you can install the Jabber client and write to us in support of [email protected]
Have you ever wondered what all that fuss about Ransomware is? You have probably heard about it in the office or read about it in the news. There may even be a pop-up ransom message on your computer’s screen now that alerts you to one particular Ransomware infection named .Acute. Whatever is the reason that landed you on this page, if you are curious to learn everything there is to know about this type of software, you have come to the right place. Here we will tell you about the different forms of Ransomware threats and how they encrypt your files or block your device, and most importantly what are the alternative ways to deal with a threat such as .Acute, .Nusar or .Neras if you really have been attacked.
The term Ransomware is used to describe a type of malware that prevents users from accessing their system or their personal files through complex encryption and requires the payment of a ransom in order to provide the decryption key. The first variants of this malware were created at the end of the 80s, and the payment had to be made by postal mail. Today the creators of Ransomware infections ask a payment through much more modern methods such as untraceable cryptocurrencies like BitCoins. The basic blackmail scheme, however, is more or less the same. The virus sneaks inside the system silently and immediately blocks access to what is considered as most valuable to the victim with the hope to extort money out of them in the form or ransom.
There are versions of Ransomware which just block the access to the screen by placing a ransom-demanding banner that covers the entire monitor. There are other variants that target mobile devices, as well as variants that operate as scareware and just try to scare the web users into giving their money.
Is .Acute Dangerous?
.Acute, is a cryptovirus – a version of Ransomware that uses a complex file-encryption in order to render the files stored on the machine inaccessible. Security experts consider the cryptoviruses as some of the most challenging to deal with because, without the application of a special decryption key, the files that have been encrypted cannot be accessed even if the Ransomware gets removed from the system.
If you have been infected with .Acute Virus, you probably have been asked to pay a certain amount of money to obtain that key in order to unlock your files from the applied encryption. Giving your money to the criminals behind the blackmail scheme, however, is not what most security experts would advise you. For one, there is absolutely no guarantee that once you pay, the crooks will really send you the key. And, for a second, you never know whether the decryption key will actually work. That’s why, instead of risking your money, our “How to remove” team would suggest you to first explore some methods that may help you remove the infection and restore your files through other means. If you don’t know where to start, take a look at the instructions in the Removal Guide below and the file-recovery suggestions included in it. If nothing works, you still can contact a legitimate professional of your choice and ask them for assistance and avoid paying ransom to some anonymous hackers.
SUMMARY:
| Name | .Acute |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Very few and unnoticeable ones before the ransom notification comes up. |
| Distribution Method | From fake ads and fake system requests to spam emails and contagious web pages. |
[add_third_banner]
Remove .Acute Virus Ransomware
1: Preparations
Note: Before you go any further, we advise you to bookmark this page or have it open on a separate device such as your smartphone or another PC. Some of the steps might require you to exit your browser on this PC.
2: Task Manager
Press Ctrl + Shift + Esc to enter the Task Manager. Go to the Tab labeled Processes (Details for Win 8/10). Carefully look through the list of processes that are currently active on you PC.
If any of them seems shady, consumes too much RAM/CPU or has some strange description or no description at all, right-click on it, select Open File Location and delete everything there.

Also, even if you do not delete the files, be sure to stop the process by right-clicking on it and selecting End Process.
3: IP related to .Acute
Go to c:\windows\system32\drivers\etc\hosts. Open the hosts file with notepad.
Find where it says Localhost and take a look below that.

If you see any IP addresses there (below Localhost) send them to us here, in the comments since they might be coming from the .Acute.
[add_forth_banner]
4: Disable Startup programs
Re-open the Start Menu and type msconfig.
Click on the first search result. In the next window, go to the Startup tab. If you are on Win 10, it will send you to the Startup part of the task manager instead, as in the picture:

If you see any sketchy/shady looking entries in the list with an unknown manufacturer or a manufacturer name that looks suspicious as there could be a link between them and .Acute , disable those programs and select OK.
5: Registry Editor
Press Windows key + R and in the resulting window type regedit.
Now, press Ctrl + F and type the name of the virus.
Delete everything that gets found. If you are not sure about whether to delete something, do not hesitate to ask us in the comments. Keep in mind that if you delete the wrong thing, you might cause all sorts of issues to your PC.
6: Deleting potentially malicious data – .Acute
Type each of the following locations in the Windows search box and hit enter to open the locations:
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
%Temp%
Delete everything you see in Temp linked to .Acute Ransomware. About the other folders, sort their contents by date and delete only the most recent entries. As always, if you are not sure about something, write to us in the comment section.
7: .Acute Decryption
The previous steps were all aimed at removing the .Acute Ransomware from your PC. However, in order to regain access to your files, you will also need to decrypt them or restore them. For that, we have a separate article with detailed instructions on what you have to do in order to unlock your data. Here is a link to that guide.
Leave a Reply