The Trojan Horse malware category is widely-known as one of the most devastating PC virus classes out there. Such threats are commonly used for all kinds of insidious cyber crimes – from personal espionage and system destruction to unauthorized access to the infiltrated machine and distribution of other virus programs, those nasty malicious malware pieces are basically the Swiss Army knife of modern malware. This is also one of the reasons why those threats are so widespread and also why newer and improved Trojan Horse versions tend to pop-up pretty much every week or so. Case in point, recently yet another infection that seems to possess Trojan Horse-like capabilities has been detected. It’s name is ServHelper Backdoor RAT and there are any who have already experienced the unpleasant consequences of having this dangerous piece of malware on their computers. Unfortunately, it can be quite challenging to successfully remove a threat like ServHelper from one’s computer even if the infection gets detected on time. Still, we have done our best to provide the visitors to this site with a reliable guide for manually eliminating the malicious program. You can find the guide at the bottom of this article and you are free to use it in case your machine has also gotten infiltrated by the insidious ServHelper Malware. If, for some reason, the instructions from the guide have not been enough to get rid of the malware in your case or if you simply feel like you might not be able to accurately execute all of the listed manual removal steps, we recommend you use the removal software tool that we have posted within the guide as it can assist you with the successful elimination of the Trojan infection. Generally, it’s best if you make use of both of the suggested removal options – the guide and the anti-malware program, as this is likely to give you the highest chances of fully eliminating the ServHelper RAT infection. Now, before you start removing the infection (or maybe after you have eliminated it), it is advisable that you take your time to read the rest of this write-up. It is essential to be well-informed about the specifics of the main types of malware that you might stumble upon and since Trojan viruses are some of the most commonly encountered ones, it’s essential that you at least have some basic understanding of the main traits of this malware class.
[add_third_banner]
Remove ServHelper Backdoor RAT Malware
1: Preparations
Note: Before you go any further, we advise you to bookmark this page or have it open on a separate device such as your smartphone or another PC. Some of the steps might require you to exit your browser on this PC.
2: Task Manager
Press Ctrl + Shift + Esc to enter the Task Manager. Go to the Tab labeled Processes (Details for Win 8/10). Carefully look through the list of processes that are currently active on you PC.
If any of them seems shady, consumes too much RAM/CPU or has some strange description or no description at all, right-click on it, select Open File Location and delete everything there.
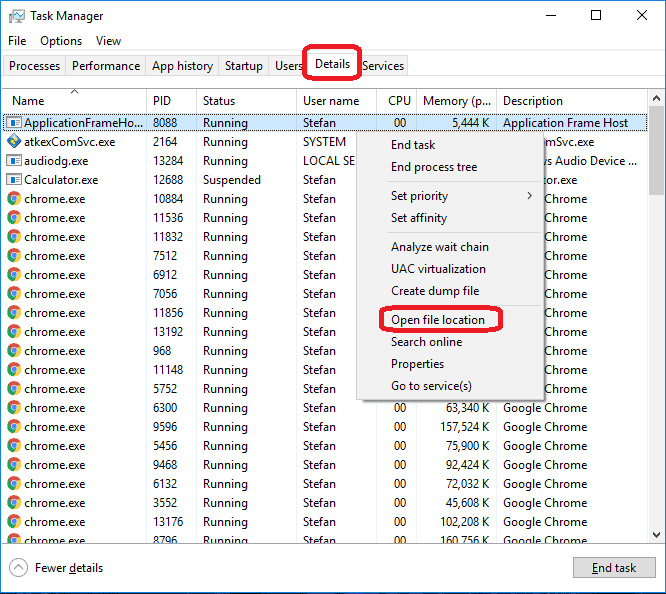
Also, even if you do not delete the files, be sure to stop the process by right-clicking on it and selecting End Process.
3: The Hosts file
Go to c:\windows\system32\drivers\etc\hosts. Open the hosts file with notepad.
Find where it says Localhost and take a look below that.

If you see any IP addresses there (below Localhost) send them to us here, in the comments since they might be coming from the virus.
[add_forth_banner]
4: Disable Startup programs
Re-open the Start Menu and type msconfig.
Click on the first search result. In the next window, go to the Startup tab. If you are on Win 10, it will send you to the Startup part of the task manager instead, as in the picture:

If you see any sketchy/shady looking entries in the list with an unknown manufacturer or a manufacturer name that looks suspicious , disable those programs and select OK.
5: Registry Editor
Press Windows key + R and in the resulting window type regedit.
Now, press Ctrl + F and type the name of the virus.
Delete everything that gets found. If you are not sure about whether to delete something, do not hesitate to ask us in the comments. Keep in mind that if you delete the wrong thing, you might cause all sorts of issues to your PC.
6: Deleting potentially malicious data
Type each of the following locations in the Windows search box and hit enter to open the locations:
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
%Temp%
Delete everything you see in Temp linked to ServHelper . About the other folders, sort their contents by date and delete only the most recent entries. As always, if you are not sure about something, write to us in the comment section.
Stealth and sneakiness
Trojans Horse infections are known for their stealthy behavior and overall lack of symptoms both when the malware initially infiltrates the computer and during the time it stays inside the attacked system. In most instances, a virus program like ServHelper would be getting distributed under the guise of some piece of content that would initially seem legitimate or at the very least harmless. Such a piece of content could be an attachment (file or link) added to some spam message to your e-mail, Skype or social network accounts, a attractive-looking online offer, a fake update request or maybe a misleading advert. Pirated program downloads are also very commonly used malware distribution tools and oftentimes they might contain Trojan infections. There are numerous other possible ways a Trojan Horse virus could be getting distributed – the ones mentioned above were only some of the more popular ones. The important thing to remember is that, in order to keep your system safe, you really need to be very cautious with the content you tend to interact with while online and with the locations that you normally visit. This is the only way to decrease the chances of running into some malicious malware source.
As we already mentioned, Trojans are difficult to detect while inside the system and though certain PC behavior irregularities like sudden errors, crashes and unusual system resources consumption might indicate that there’s an infection, oftentimes the only somewhat reliable way of spotting such a threat would be through the use of a dedicated security program like a strong antivirus or anti-malware tool.
A multipurpose threat
As we pointed out at the start of this article, Trojans are versatile threats and could oftentimes be used for a variety of insidious task. A virus like ServHelper might be employed to corrupt the data on your system (or the system itself), to spy on your activities, to steal sensitive information, to load other malware programs like Ransomware, Rootkits, Worms, etc. inside your PC and so on. There could really be many ways in which such a threat could harm your machine, data and your virtual privacy which is why you need to make sure to take away the malicious malware piece before it has managed to fully carry out its task.
SUMMARY:
| Name | ServHelper |
| Type | Trojan |
| Danger Level | High (Trojans are often used as a backdoor for Ransomware) |
| Symptoms | Trojans might cause different irregularities like high RAM or CPU use for no visible reason but oftentimes there won’t be any symptoms whatsoever. |
| Distribution Method | Malvertising, spam, illegal downloads, pirated content, etc. |
Leave a Reply