This page aims to help you remove .Kiratos for free. Our instructions also cover how any .Hrosas file can be recovered.
This post is dedicated to all the victims of .Kiratos – a recently reported Ransomware infection from the cryptovirus type which uses a very complex encryption algorithm to lock the files found on the computer so that it can later blackmail the victims for a ransom payment in exchange for the locked data’s liberation. In case that your most valuable documents, images, videos, audio files, archives or other types of data have had their file-extension replaced with some weird one and you are now not able to open or use them, then most probably you have been infected with this malware without your knowledge. In the next lines, however, we will do our best to help you effectively deal with .Kiratos and the consequences of its attack and, most importantly, remove the harmful code that is hiding inside your system.
Some more words about the nature of .Kiratos
.Kiratosis a ransomware infection of the same family tree as .Verasto Virus , .Norvasc and .Moresa and .Hrosas
.Kiratos is a creation of hackers with malicious intentions that wish to extort money from their victims by blocking the access to their most needed data and by requesting that a ransom gets paid for its liberation. The whole scheme is based on a very complex secret file-encryption process which uses an encryption code that renders the targeted files inaccessible without the application of a special decryption key. That key is stored on the hackers’ servers while the victims are ruthlessly blackmailed for the payment of a certain amount of money for it. Typically, once the Ransomware completes with the encryption process, it generates a ransom demanding message on the screen of the attacked computer. That message informs the victims about what has happened to the files and asks them to follow certain instructions if they want to obtain the decryption key necessary for the restoration of the captured data.
Typical Mode of operation for .Kiratos
The hacker behind .Kiratos may use different tactics such as threatening messages and tight deadlines in order to not give you time to look for alternative solutions. They may even go as far as offer to decrypt a file or two for free in order to assure you they have a working solution. One of their typical tactics is to scare the users by saying that the special key for the decryption of their files will be deleted from their servers if a payment is not made before the given time runs out.
Unfortunately, even if you carefully fulfill all of their ransom demands, you should know that there is absolutely no guarantee about the future of your computer and your files. The crooks may vanish with the money and never send you that key. On top of that, an active Ransomware in the system can make your PC useless because it can prevent you from storing any new data on it. That’s why we suggest you focus eradicating the infection and then explore some alternative solutions which may help you get some of your files back without paying a ransom to anyone. You can start with scanning the computer with a reliable malware removal tool such as the one below and by using the instructions that follow.
SUMMARY:
| Name | .Kiratos |
| Type | Ransomware |
| Danger Level | High (Ransomware is by far the worst threat you can encounter) |
| Symptoms | Very few and unnoticeable ones before the ransom notification comes up. |
| Distribution Method | From fake ads and fake system requests to spam emails and contagious web pages. |
[add_third_banner]
Can’t Remove .Kiratos? This page includes detailed instructions on how to remove .Kiratos that can be found at the bottom half of this article.
Remove .Kiratos
1: Preparations
Note: Before you go any further, we advise you to bookmark this page or have it open on a separate device such as your smartphone or another PC. Some of the steps might require you to exit your browser on this PC.
2: Task Manager
Press Ctrl + Shift + Esc to enter the Task Manager. Go to the Tab labeled Processes (Details for Win 8/10). Carefully look through the list of processes that are currently active on you PC.
If any of them seems shady, consumes too much RAM/CPU or has some strange description or no description at all, right-click on it, select Open File Location and delete everything there.
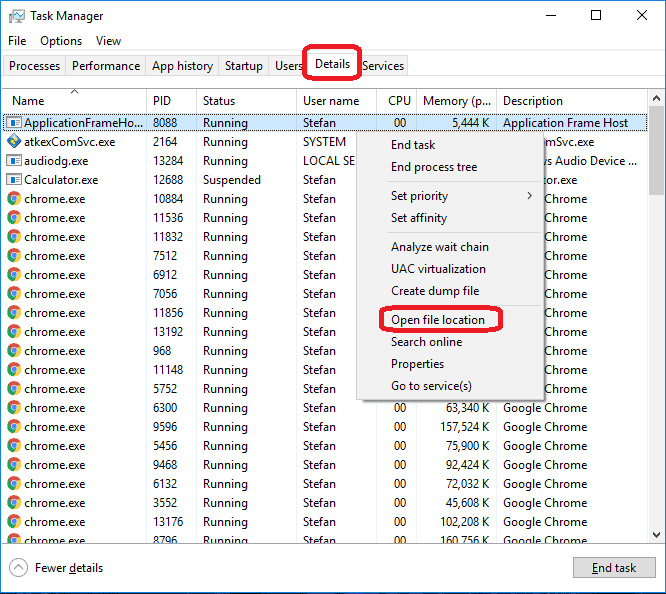
Also, even if you do not delete the files, be sure to stop the process by right-clicking on it and selecting End Process.
3: The Hosts file
Go to c:\windows\system32\drivers\etc\hosts. Open the hosts file with notepad.
Find where it says Localhost and take a look below that.

If you see any IP addresses there (below Localhost) send them to us here, in the comments since they might be coming from the virus.
4: Disable Startup programs
Re-open the Start Menu and type msconfig.
Click on the first search result. In the next window, go to the Startup tab. If you are on Win 10, it will send you to the Startup part of the task manager instead, as in the picture:

If you see any sketchy/shady looking entries in the list with an unknown manufacturer or a manufacturer name that looks suspicious, disable those programs and select OK.
5: Registry Editor
Press Windows key + R and in the resulting window type regedit.
Now, press Ctrl + F and type the name of the virus.
Delete everything that gets found. If you are not sure about whether to delete something, do not hesitate to ask us in the comments. Keep in mind that if you delete the wrong thing, you might cause all sorts of issues to your PC.
6: Deleting potentially malicious data
Type each of the following locations in the Windows search box and hit enter to open the locations:
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
%Temp%
Delete everything you see in Temp. About the other folders, sort their contents by date and delete only the most recent entries. As always, if you are not sure about something, write to us in the comment section.
7: Decryption
The previous steps were all aimed at removing the Ransomware from your PC. However, in order to regain access to your files, you will also need to decrypt them or restore them. For that, we have a separate article with detailed instructions on what you have to do in order to unlock your data. Here is a link to that guide.
Leave a Reply