About ChaosCC Hacker Group Email
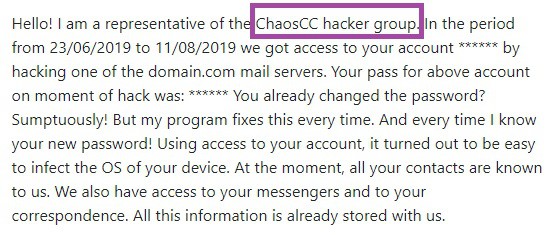
Trojans like ChaosCC Hacker Group are really problematic malware programs that can be particularly detrimental to the health of your computer. Many Trojans are known for causing the infected machine to become unresponsive, to crash every couple of minutes, to become extremely slow and to get a lot of system errors among other things. Those issues, however, are typically only a byproduct of the actual harm that infections of the Trojan Horse family may cause. While in your computer, a Trojan may keylog everything you type on your keyboard and thereby obtain information about your personal or professional life, it may get hold of your online account usernames and passwords, it may acquire your banking numbers, and even spy on your chat conversations. Another thing a Trojan can do is force your system to carry out different tasks that have been given to it by the hackers who are behind it. In many cases, computers infected by a Trojan are turned into cryptocurrency-mining bots or are collectively used to execute massive DDoS attacks, crashing the sites of big companies, of institutions, and even of governments. One other common use of a Trojan virus is for backdooring activities – in such cases, the Trojan virus plays a more secondary role to the primary role of the virus that it is supposed to backdoor into the targeted machine. One really common example is when a Trojan like ChaosCC Hacker Group allows Ransomware cryptoviruses to enter the computer of the user totally unnoticed. And, in case you don’t know what Ransomware cryptoviruses do, they block the user’s access to all personal files in the computer and then make the user pay a ransom to retrieve their locked data.
Of course, the examples we have given above are only that – examples. The Trojan infections are quite versatile and as long as they get Administrative rights inside the infected machine, there is not much that they couldn’t do with your computer. In general, you can expect all kinds of corruption and damage if a Trojan like ChaosCC Hacker Group is allowed to stay in your machine for too long. This is exactly why we strongly advise you to take care of this issue while you still can save your machine and data. The sooner you take action, the greater your chances of successfully overcoming the infection are. In a sense, you can consider yourself lucky, because you have at least noticed that something was wrong with your system, and because you now have the chance to do something about it – many victims of Trojan infections do not get such a chance.
Removing ChaosCC Hacker Group
The removal of this infection may be rather challenging, especially if your antivirus isn’t able to do anything about it or if you do not have an antivirus. In any case, the manual guide below should allow most of you to get rid of any Trojan-related data, and for those of you who haven’t been able to eliminate the threat through the manual removal steps, remember that you can also use the professional removal tool for infections like ChaosCC Hacker Group that we have linked below.
SUMMARY:
| Name | ChaosCC Hacker Group |
| Type | Trojan |
| Danger Level | High (Trojans are often used as a backdoor for Ransomware) |
| Symptoms | A Trojan may make your system sluggish or it may outright crash it to BSOD. |
| Distribution Method | Some of the distribution methods related to Trojan Horse infections are the use of malicious spam letters and malvertisements as well as the use of pirated games, and other software. |
[add_third_banner]
Remove ChaosCC Hacker Group Email
1: Preparations
Note: Before you go any further, we advise you to bookmark this page or have it open on a separate device such as your smartphone or another PC. Some of the steps might require you to exit your browser on this PC.
2: Task Manager
Press Ctrl + Shift + Esc to enter the Task Manager. Go to the Tab labeled Processes (Details for Win 8/10). Carefully look through the list of processes that are currently active on you PC.
If any of them seems shady, consumes too much RAM/CPU or has some strange description or no description at all, right-click on it, select Open File Location and delete everything there.

Also, even if you do not delete the files, be sure to stop the process by right-clicking on it and selecting End Process.
3: IP related to ChaosCC Hacker Group
Go to c:\windows\system32\drivers\etc\hosts. Open the hosts file with notepad.
Find where it says Localhost and take a look below that.

If you see any IP addresses there (below Localhost) send them to us here, in the comments since they might be coming from the ChaosCC Hacker Group.
[add_forth_banner]
4: Disable Startup programs
Re-open the Start Menu and type msconfig.
Click on the first search result. In the next window, go to the Startup tab. If you are on Win 10, it will send you to the Startup part of the task manager instead, as in the picture:

If you see any sketchy/shady looking entries in the list with an unknown manufacturer or a manufacturer name that looks suspicious as there could be a link between them and ChaosCC Hacker Group , disable those programs and select OK.
5: Registry Editor
Press Windows key + R and in the resulting window type regedit.
Now, press Ctrl + F and type the name of the virus.
Delete everything that gets found. If you are not sure about whether to delete something, do not hesitate to ask us in the comments. Keep in mind that if you delete the wrong thing, you might cause all sorts of issues to your PC.
6: Deleting potentially malicious data – ChaosCC Hacker Group
Type each of the following locations in the Windows search box and hit enter to open the locations:
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
%Temp%
Delete everything you see in Temp linked to ChaosCC Hacker Group. About the other folders, sort their contents by date and delete only the most recent entries. As always, if you are not sure about something, write to us in the comment section.
Leave a Reply