This page aims to help you remove “Anonymous Hacker” Email Bitcoin Scam. Our removal instructions work for every version of Windows.
Have you recently been receiving threatening phishing e-mails within which the sender tells you that they have been able to infect your computer with an insidious Trojan Horse virus that has gathered some sensitive info about you and that you must pay a ransom if you don’t want the said information to be released online and made public? If that is the situation you are currently in, then it is advisable you read the next lines, where we will tell you what the best course of action is.
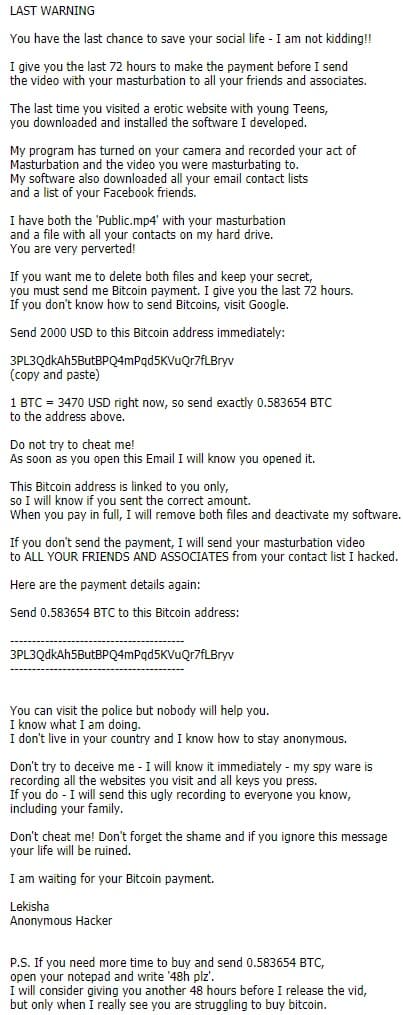
Now, this particular blackmailing scheme is a very popular one and, in most of the cases, it is nothing more than a simple scam. In reality, there is probably no malware inside your computer and the scammer is simply relying on your naivete and on the shock factor of receiving such a scary e-mail that could make you pay the demanded money without taking a moment to actually assess the situation and think about what the best course of action may be. However, since you are on this post, we assume that you, at the very least, are not willing to directly pay anything to such scammers without first researching the potential alternatives. In such a case, our advice for you is to not give in to the demands of the scammers. As we already said, there’s likely no malware on your PC and the blackmailer is most probably bluffing. However, since Trojan viruses are not threats to be taken lightly, we have added a removal guide for one of the newest and most dangerous Trojan Horse viruses – a threat named “Anonymous Hacker”. We advise you to take a look at the guide and complete its instructions so that you can be sure that there really is nothing hazardous inside your machine.
Some info on Trojans like “Anonymous Hacker”
Though phishing e-mails like the ones you are likely receiving at the moment are mostly scammers’ attempts to extort money from less experienced users, it’s still important to have an overall understanding of what a Trojan Horse threat may be capable of and how to protect your machine against such viruses. First and foremost, Trojans are highly versatile, they can harm important system data, insert other infections the likes of Rootkits, Ransomware and Worms inside a given PC, gather sensitive data from the machine and even remotely control its processes. There are actually many other harmful tasks that a threat like “Anonymous Hacker” may be capable of – there’s no end to its malicious abilities. The same applies to most other threats of the Trojan Horse malware family. In addition, these infections could come to your PC disguised in many ways – attachments to spam e-mails such as the one you are currently receiving, added elements to pirated software, hidden inside misleading advertisement and so on and so forth. It is, therefore, essential that you remain vigilant at all times during online time and also that you remember to regularly update your antivirus software.
SUMMARY:
| Name | “Anonymous Hacker” |
| Type | Trojan |
| Danger Level | High |
| Symptoms | “Anonymous Hacker” Trojan is hard to detect and aside from increased use of RAM and CPU, there would barely be any other visible red flags. |
| Distribution Method | Most of the time, Trojans get distributed through spam e-mails and social network messages, malicious ads, shady and pirated downloads, questionable torrents and other similar methods. |
Remove “Anonymous Hacker” Email Bitcoin Virus
1: Preparations
Note: Before you go any further, we advise you to bookmark this page or have it open on a separate device such as your smartphone or another PC. Some of the steps might require you to exit your browser on this PC.
[add_third_banner]
2: Task Manager
Press Ctrl + Shift + Esc to enter the Task Manager. Go to the Tab labeled Processes (Details for Win 8/10). Carefully look through the list of processes that are currently active on you PC.
If any of them seems shady, consumes too much RAM/CPU or has some strange description or no description at all, right-click on it, select Open File Location and delete everything there.

Also, even if you do not delete the files, be sure to stop the process by right-clicking on it and selecting End Process.
3: The Hosts file
Go to c:\windows\system32\drivers\etc\hosts. Open the hosts file with notepad.
Find where it says Localhost and take a look below that.

If you see any IP addresses there (below Localhost) send them to us here, in the comments since they might be coming from the virus.
[add_forth_banner]
4: Disable Startup programs
Re-open the Start Menu and type msconfig.
Click on the first search result. In the next window, go to the Startup tab. If you are on Win 10, it will send you to the Startup part of the task manager instead, as in the picture:

If you see any sketchy/shady looking entries in the list with an unknown manufacturer or a manufacturer name that looks suspicious , disable those programs and select OK.
5: Registry Editor
Press Windows key + R and in the resulting window type regedit.
Now, press Ctrl + F and type the name of the virus.
Delete everything that gets found. If you are not sure about whether to delete something, do not hesitate to ask us in the comments. Keep in mind that if you delete the wrong thing, you might cause all sorts of issues to your PC.
6: Deleting potentially malicious data
Type each of the following locations in the Windows search box and hit enter to open the locations:
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
%Temp%
Delete everything you see in Temp linked to “Anonymous Hacker”. About the other folders, sort their contents by date and delete only the most recent entries. As always, if you are not sure about something, write to us in the comment section.
Leave a Reply