This page aims to help you remove 19qqYeGgbzhT8Lic5WsbDZgJkzAy82R6fF. Our removal instructions work for every version of Windows.
19qqYeGgbzhT8Lic5WsbDZgJkzAy82R6fF in depth
Every web user knows that the web space is full of security hazards and one wrong click can land them on webpages that contain infections like Viruses, Trojans, Ransomware or Spyware.
19qqYeGgbzhT8Lic5WsbDZgJkzAy82R6fF is very reminiscent of another similar case – the 14DvFghvkzQujf5Kd5AL2VKjxaYm5KidxR Bitcoin Email Scam.
One viral email scam that has been spreading around the web lately is yet another email BitCoin blackmailing scam. The victims of this scam typically get spammed with email messages in their inbox which contain a warning from a self-proclaimed hacker, whose sole goal is to scare them into sending money to the scammer’s BitCoin wallet. The threat in the messages can be different but are generally something like this: The “hacker” claims that a hidden Trojan Horse is lying dormant in your computer and they will activate it if you don’t pay a ransom to his cryptocurrency account. The scammer threatens to corrupt your system, delete your personal data or make some sensitive details about you publicly available and then gives you a deadline to fulfill the ransom demands.
In case you’ve landed on our guide because you have recently been spammed with a message with a similar scenario, then you are most probably worried about the possibility of having a real malware inside your machine. After all, it is a well-known fact that Trojans can hide deep in the system without the users’ knowledge and do a lot of nasty stuff once they get activated by the hackers’ command. What is more, such threats can often get distributed with the help of spam messages and scam emails. In fact, there is an infection named 19qqYeGgbzhT8Lic5WsbDZgJkzAy82R6fF, which is currently on the loose and can travel the web with the help of different email scams, including BitCoin scams like this one. That’s why the best way to ensure your system is safe is to run a full scan with a reliable security program and remove any hidden threats or suspicious data that may get detected.
How dangerous is 19qqYeGgbzhT8Lic5WsbDZgJkzAy82R6fF?
The email scams can include different threats and can be both annoying and dangerous as you may never be fully sure if there isn’t’ some actual malware in your computer. However, even if you have been getting aggressively spammed with blackmailing messages in your inbox, you should not get too stressed about it. In most of the cases, the crooks who spread such emails don’t actually have access to your computer, let alone control over a Trojan hidden in it. Still, to be on the safer side, we highly recommend you double-check your entire computer with a reliable security program and remove anything that appears to be suspicious. After all, infections like 19qqYeGgbzhT8Lic5WsbDZgJkzAy82R6fF are a serious threat to any system and can do nasty stuff if not removed on time which is why the guide below has been posted for those of you who may want to ensure their systems are safe and malware-free.
Hello, minx! …… YES! With a single keystroke, I can send these photos to all your contacts in the mail, phone and social networks. I can also publish access to all your accounts that you use, including the current one. If you do not want to allow this, then: transfer $539 to my bitcoin address (if you don’t understand something, write to Google: “Buy bitcoin”). My Bitcoin address (BTC wallet): 19qqYeGgbzhT8Lic5WsbDZgJkzAy82R6fF After receiving the payment, I will delete all your photos and other data, and you will never see me again. I will also launch a team that will remove my virus from your device! I give you 48 hours (2 days) for payment. I have a notice of this letter being read, and the countdown will work when you see this letter. There is no point in complaining or writing anywhere, since this letter cannot be traced. I’m never wrong! …… Be clever girl! Your respectable observer.
SUMMARY:
| Name | 19qqYeGgbzhT8Lic5WsbDZgJkzAy82R6fF |
| Type | Trojan |
| Danger Level | High (Trojans are often used as a backdoor for Ransomware) |
| Symptoms | Trojans rarely show any visible symptoms, thus they often require the use of reliable antivirus program to be detected. |
| Distribution Method | Spam messages and malicious emails are some of the most common sources of Trojan-based infections. |
[add_third_banner]
Remove 19qqYeGgbzhT8Lic5WsbDZgJkzAy82R6fF Bitcoin Email Guide
1: Preparations
Note: Before you go any further, we advise you to bookmark this page or have it open on a separate device such as your smartphone or another PC. Some of the steps might require you to exit your browser on this PC.
2: Task Manager
Press Ctrl + Shift + Esc to enter the Task Manager. Go to the Tab labeled Processes (Details for Win 8/10). Carefully look through the list of processes that are currently active on you PC.
If any of them seems shady, consumes too much RAM/CPU or has some strange description or no description at all, right-click on it, select Open File Location and delete everything there.
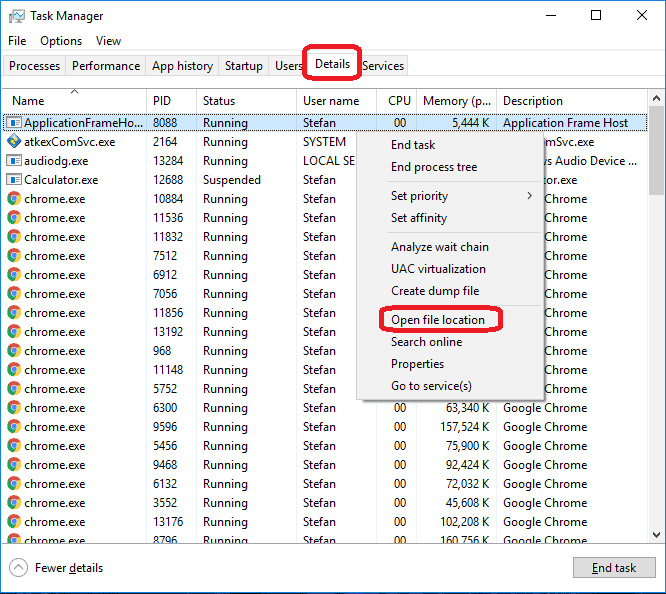
Also, even if you do not delete the files, be sure to stop the process by right-clicking on it and selecting End Process.
3: IP related to 19qqYeGgbzhT8Lic5WsbDZgJkzAy82R6fF
Go to c:\windows\system32\drivers\etc\hosts. Open the hosts file with notepad.
Find where it says Localhost and take a look below that.

If you see any IP addresses there (below Localhost) send them to us here, in the comments since they might be coming from the 19qqYeGgbzhT8Lic5WsbDZgJkzAy82R6fF.
[add_forth_banner]
4: Disable Startup programs
Re-open the Start Menu and type msconfig.
Click on the first search result. In the next window, go to the Startup tab. If you are on Win 10, it will send you to the Startup part of the task manager instead, as in the picture:

If you see any sketchy/shady looking entries in the list with an unknown manufacturer or a manufacturer name that looks suspicious as there could be a link between them and 19qqYeGgbzhT8Lic5WsbDZgJkzAy82R6fF , disable those programs and select OK.
5: Registry Editor
Press Windows key + R and in the resulting window type regedit.
Now, press Ctrl + F and type the name of the virus.
Delete everything that gets found. If you are not sure about whether to delete something, do not hesitate to ask us in the comments. Keep in mind that if you delete the wrong thing, you might cause all sorts of issues to your PC.
6: Deleting potentially malicious data – 19qqYeGgbzhT8Lic5WsbDZgJkzAy82R6fF
Type each of the following locations in the Windows search box and hit enter to open the locations:
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
%Temp%
Delete everything you see in Temp linked to 19qqYeGgbzhT8Lic5WsbDZgJkzAy82R6fF Ransomware. About the other folders, sort their contents by date and delete only the most recent entries. As always, if you are not sure about something, write to us in the comment section.
Leave a Reply