.Neras File Virus Details
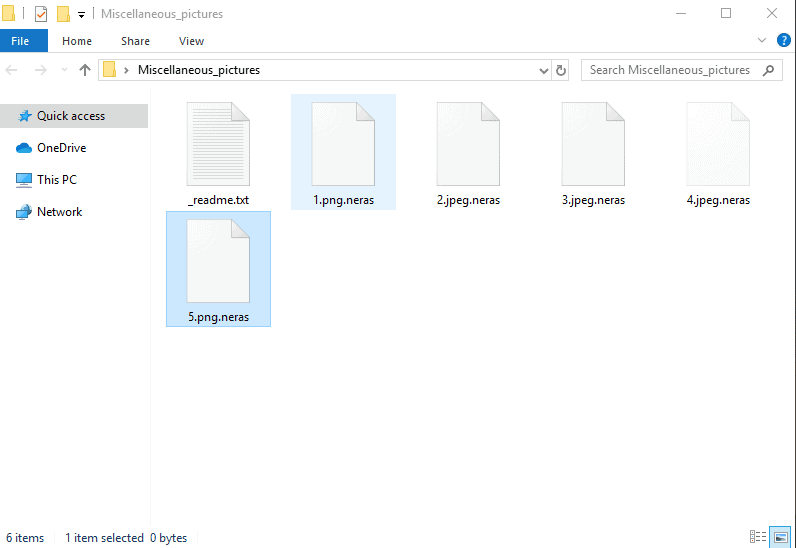
After the ransomware encrypt your files, it leaves a _readme.txt file with instructions to follow:
ATTENTION!
Don’t worry, you can return all your files!
All your files like photos, databases, documents and other important are encrypted with strongest encryption and unique key.
The only method of recovering files is to purchase decrypt tool and unique key for you.
This software will decrypt all your encrypted files.
What guarantees you have?
You can send one of your encrypted file from your PC and we decrypt it for free.
But we can decrypt only 1 file for free. File must not contain valuable information.
You can get and look video overview decrypt tool:
*Redacted for security reasons*
Price of private key and decrypt software is $980.
Discount 50% available if you contact us first 72 hours, that’s price for you is $490.
Please note that you’ll never restore your data without payment.
Check your e-mail “Spam” or “Junk” folder if you don’t get answer more than 6 hours.To get this software you need write on our e-mail:
[email protected]Reserve e-mail address to contact us:
[email protected]Our Telegram account:
Recently, our “How to remove” team has been getting flooded with messages concerning one recently released Ransomware infection called .Neras. The concerned web users refer to this infection as a cryptovirus and have been asking for help with its removal and with the reversal of the harmful effects that .Neras has brought on. Now, most people use the term “virus” to refer to all types of malware. Actually, a virus is just one of the many types of malware that exist. Other common types are Worms, Trojans, Spyware, and Ransomware. Each type of malware has a specific purpose. The Worms worsen the performance of the computer. Viruses are designed to copy themselves many times in the system and, to cause file corruption, and then spread to new hosts. The Trojans are looking for a secret backdoor to access the system and get the victim’s personal information. The reasons that lead cybercriminals to create and distribute these types of malware are numerous.
In the case of Ransomware, the reason is very clear: the attacker wants money. In general, the goal of a Ransomware isn’t to damage or destroy anything. It’s not even about stealing your identity, but about convincing you to pay a certain amount of money in the form of a ransom in order to regain access to what the Ransomware has blocked. .Neras, for instance, uses a special file encryption algorithm to secretly block the access to your personal files and then places a ransom-demanding message on your screen, asking you to pay a ransom in exchange for the decryption of the sealed files. A ransom-demanding message typically gets displayed on the screen and acts as a notification which provides the victims with instructions on how to transfer the payment. Those who refuse to follow the payment instructions are threatened to never access their files again, while those who pay are promised to receive a special decryption key for decoding the encrypted data.
This type of malware, like .Horon .Gerosan, .Vesad targets companies and individual users around the world and over the years has become one of the favorite weapons of hackers who try to make money at the expense of the unsuspecting web users whose valuable data gets encrypted. But, how can these malicious programs be removed and how to protect your data against them? The hackers exploit the weaknesses of the system as well as different distribution techniques and transmitters to infect as many computers as they can. Infected web pages, different email attachments, spam, video files, system updates or programs that seem generally reliable are the tools that allow such malicious software to infect a computer in seconds.
Can I Remove .Neras File Virus Myself?
Sadly, infections like .Neras operate without any noticeable symptoms. When they infiltrate a given system, there are usually no visible suspicious activities until the Ransomware is done locking-up the files. Therefore, in order to detect .Neras and other similar threats, it is very important to use a reliable antivirus with special anti-ransomware protection as well as to remember to always backup your important files. It is not a good idea to pay the hackers as there is absolutely no guarantee that they will send you anything that may help you with the data’s recovery. However, what you can do is you can carefully remove the infection and give a try to some alternative file-recovery methods such as the ones in the removal guide below.
.Neras SUMMARY:
| Name | .Neras |
| Type | Ransomware |
| Danger Level | High (.Neras Ransomware encrypts all types of files) |
| Symptoms | .Neras Ransomware is hard to detect and aside from increased use of RAM and CPU, there would barely be any other visible red flags. |
| Distribution Method | Most of the time, Trojans get distributed through spam e-mails and social network messages, malicious ads, shady and pirated downloads, questionable torrents and other similar methods. |
[add_third_banner]
Remove .Neras Fiel Virus Ransomware
1: Preparations
Note: Before you go any further, we advise you to bookmark this page or have it open on a separate device such as your smartphone or another PC. Some of the steps might require you to exit your browser on this PC.
2: Task Manager
Press Ctrl + Shift + Esc to enter the Task Manager. Go to the Tab labeled Processes (Details for Win 8/10). Carefully look through the list of processes that are currently active on you PC.
If any of them seems shady, consumes too much RAM/CPU or has some strange description or no description at all, right-click on it, select Open File Location and delete everything there.

Also, even if you do not delete the files, be sure to stop the process by right-clicking on it and selecting End Process.
3: IP related to .Neras
Go to c:\windows\system32\drivers\etc\hosts. Open the hosts file with notepad.
Find where it says Localhost and take a look below that.

If you see any IP addresses there (below Localhost) send them to us here, in the comments since they might be coming from the .Neras.
[add_forth_banner]
4: Disable Startup programs
Re-open the Start Menu and type msconfig.
Click on the first search result. In the next window, go to the Startup tab. If you are on Win 10, it will send you to the Startup part of the task manager instead, as in the picture:

If you see any sketchy/shady looking entries in the list with an unknown manufacturer or a manufacturer name that looks suspicious as there could be a link between them and .Neras , disable those programs and select OK.
5: Registry Editor
Press Windows key + R and in the resulting window type regedit.
Now, press Ctrl + F and type the name of the virus.
Delete everything that gets found. If you are not sure about whether to delete something, do not hesitate to ask us in the comments. Keep in mind that if you delete the wrong thing, you might cause all sorts of issues to your PC.
6: Deleting potentially malicious data – .Neras
Type each of the following locations in the Windows search box and hit enter to open the locations:
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
%Temp%
Delete everything you see in Temp linked to .Neras Ransomware. About the other folders, sort their contents by date and delete only the most recent entries. As always, if you are not sure about something, write to us in the comment section.
7: .Neras Decryption
The previous steps were all aimed at removing the .Neras Ransomware from your PC. However, in order to regain access to your files, you will also need to decrypt them or restore them. For that, we have a separate article with detailed instructions on what you have to do in order to unlock your data. Here is a link to that guide.
Leave a Reply