You have most likely had a close encounter with a specific type of a cyber attack if you’ve landed on this page, and [email protected] might be the reason for your problems. Now, to help you better understand what has happened to your computer, we will start by saying that [email protected] is a Ransomware cryptovirus, developed to encrypt your files, and to blackmail you for a ransom payment by keeping your PC’s data hostage. This is a really unpleasant kind of online threat, and we’re going to do our best to help you cope with it in the next few lines.
The [email protected] virus
Most probably, you want to know precisely what has happened to your files, how you got infected with [email protected], and how you can get back to your data. We’re going to address all these questions, and offer you some tips on how to avoid future Ransomware infections.
Unlike some other malware that will steal, corrupt, or completely delete your information once your PC has been infected, [email protected] does not do that. In no way will it delete or corrupt the files on your system. However, what it does is, it simply locks different documents, images, videos, audios, archives, and other important digital information, by applying a complex file encryption to it. This way, none of the files cannot be recognized and opened by any program. They all are still on the computer, but the victims cannot access them.
The [email protected] file encryption

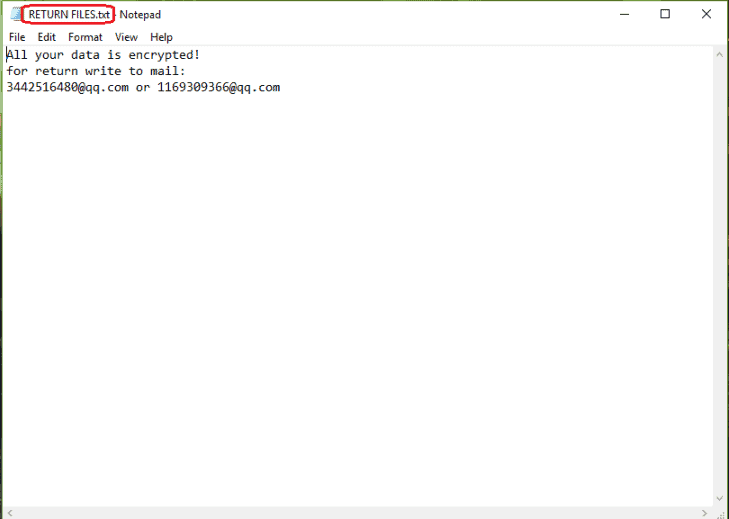
Only a unique decryption key can be used to decrypt the sealed information. And that’s what the hackers are asking a ransom for. Once the malware encrypts the information, the decryption key is generated on their server, and the crooks ask for a certain amount of money in order to send it to you. The hackers often give a short deadline to pay the ransom in case you want you information to be decrypted. Cryptocurrencies, such as BitCoin are the preferred methods of payment, since they are untraceable, and provide anonymity. Payment details are provided in the ransom note that appears on the screen of the victim. All of these practices are trying to scare the people, and make them pay as fast as possible without researching their alternatives.
Paying the ransom, however, is oftentimes the worst thing that could be done by the victims of Ransomware. Many security specialists, including our “How to Remove” team, advise the users to not give their money to the cyber criminals for a number of reasons. First of all, this helps the hackers get rich quickly, and transforms infections like [email protected] or Hese into a lucrative “business” model for more cyber crooks. Besides, there is no assurance that the decryption key will actually be received, and that it will operate correctly. What if it fails to decrypt the applied encryption code? In such a case, you would lose both your money, and your data. Moreover, the infected computer cannot be used safely if the Ransomware is still on the system. Therefore, a great place to start dealing with this malware, and its consequences is its removal from the infected computer.
For that, please ensure that you carefully follow the instructions in the removal guide below. Think about using a removal tool if you’re not sure how good you can manage the manual process. Also, check out the file-recovery section of the guide below, where there are steps which may help you restore some of your information.
[email protected] SUMMARY:
| Name | [email protected] |
| Type | Ransomware |
| Danger Level | High ([email protected] Ransomware encrypts all types of files) |
| Symptoms | [email protected] Ransomware is hard to detect and aside from increased use of RAM and CPU, there would barely be any other visible red flags. |
| Distribution Method | Most of the time, Trojans get distributed through spam e-mails and social network messages, malicious ads, shady and pirated downloads, questionable torrents and other similar methods. |
[add_third_banner]
Remove [email protected] Ransomware
1: Preparations
Note: Before you go any further, we advise you to bookmark this page or have it open on a separate device such as your smartphone or another PC. Some of the steps might require you to exit your browser on this PC.
2: Task Manager
Press Ctrl + Shift + Esc to enter the Task Manager. Go to the Tab labeled Processes (Details for Win 8/10). Carefully look through the list of processes that are currently active on you PC.
If any of them seems shady, consumes too much RAM/CPU or has some strange description or no description at all, right-click on it, select Open File Location and delete everything there.

Also, even if you do not delete the files, be sure to stop the process by right-clicking on it and selecting End Process.
3: IP related to [email protected]
Go to c:\windows\system32\drivers\etc\hosts. Open the hosts file with notepad.
Find where it says Localhost and take a look below that.

If you see any IP addresses there (below Localhost) send them to us here, in the comments since they might be coming from the [email protected].
[add_forth_banner]
4: Disable Startup programs
Re-open the Start Menu and type msconfig.
Click on the first search result. In the next window, go to the Startup tab. If you are on Win 10, it will send you to the Startup part of the task manager instead, as in the picture:

If you see any sketchy/shady looking entries in the list with an unknown manufacturer or a manufacturer name that looks suspicious as there could be a link between them and [email protected] , disable those programs and select OK.
5: Registry Editor
Press Windows key + R and in the resulting window type regedit.
Now, press Ctrl + F and type the name of the virus.
Delete everything that gets found. If you are not sure about whether to delete something, do not hesitate to ask us in the comments. Keep in mind that if you delete the wrong thing, you might cause all sorts of issues to your PC.
6: Deleting potentially malicious data – [email protected]
Type each of the following locations in the Windows search box and hit enter to open the locations:
%AppData%
%LocalAppData%
%ProgramData%
%WinDir%
%Temp%
Delete everything you see in Temp linked to [email protected] Ransomware. About the other folders, sort their contents by date and delete only the most recent entries. As always, if you are not sure about something, write to us in the comment section.
7: [email protected] Decryption
The previous steps were all aimed at removing the [email protected] Ransomware from your PC. However, in order to regain access to your files, you will also need to decrypt them or restore them. For that, we have a separate article with detailed instructions on what you have to do in order to unlock your data. Here is a link to that guide.
Leave a Reply